Azure Daily 2022
Materialized view provides the ability to create Apache Cassandra tables with different primary/partition keys. This reduces write latency for your source table since the service handles populating the materialized views automatically and asynchronously. Benefit from low latency point reads directly from the views and overall greater compatibility with native Apache Cassandra.
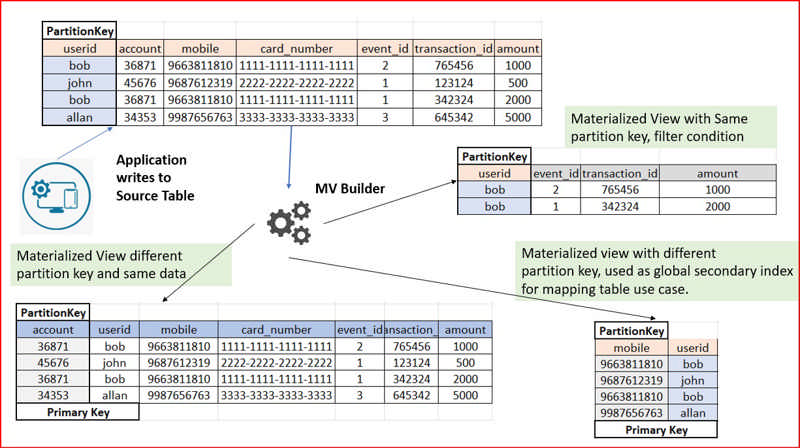
Source: Public Preview: Materialized view for Azure Cosmos DB for Apache Cassandra
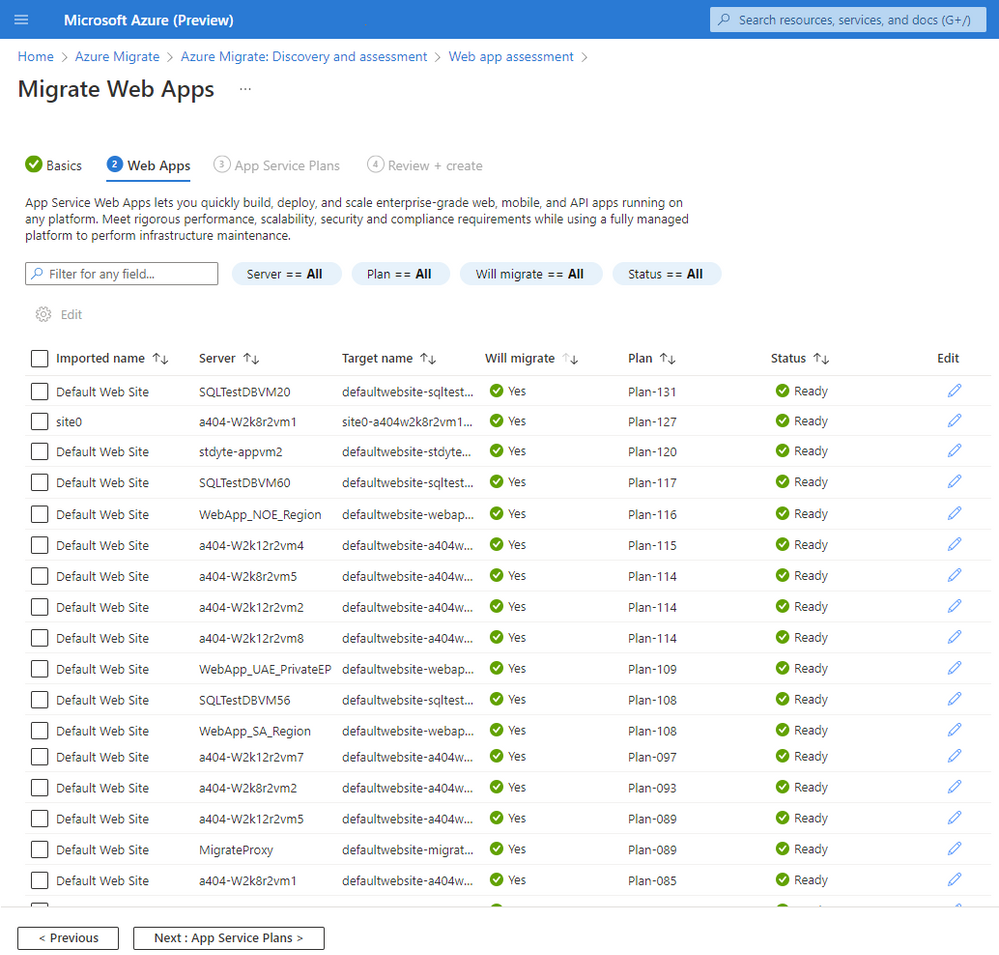
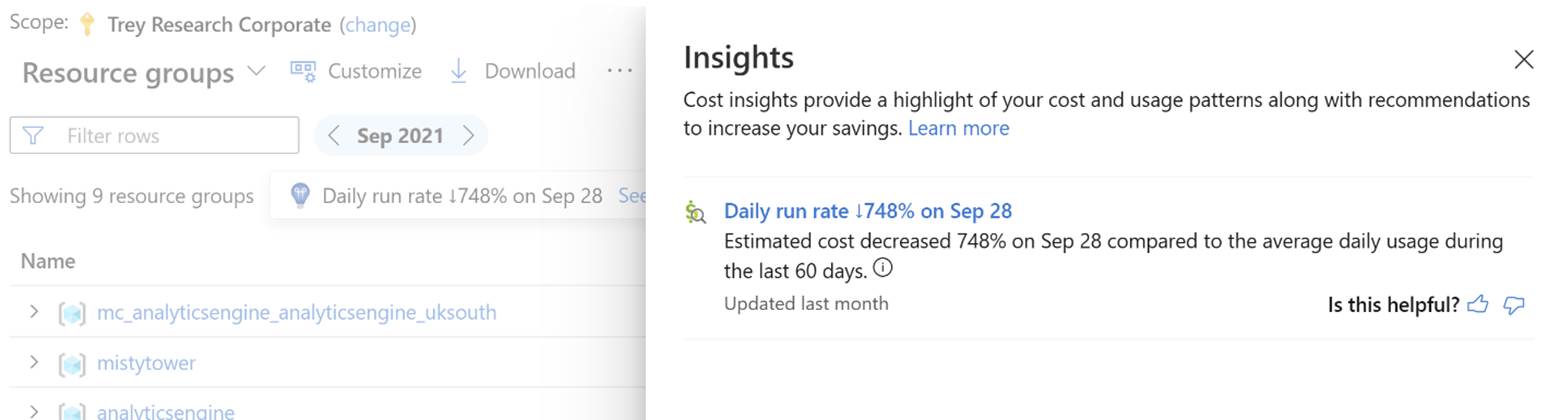
The Business case capability in Azure Migrate helps you build business proposals to understand how Azure can bring the most value. It can help you understand the return on investment for migrating your servers, SQL Server deployments and ASP.NET web apps running in your VMware environment to Azure. The business case can be created with just a few clicks and can help you understand:
- On-premises vs Azure total cost of ownership and year on year cashflow.
- Resource utilization-based insights to identify servers and workloads that are ideal for cloud and right-sized recommendations in Azure.
- Quick wins for migration and modernization including end of support Windows OS and SQL versions.
- Long term cost savings by moving from a capital expenditure model to an Operating expenditure model, by paying for only what you use.
Build your first business case today. Learn more
Source: Public preview: Build a business case with Azure Migrate
Durable Functions for Java is now generally available. Durable Functions makes it easy to orchestrate stateful workflows as-code in a serverless environment. Some common stateful application patterns that Durable Functions facilitates include "function chaining", "fan out/fan in", "async http APIs", "monitor", and "human interaction". More details about Durable Functions concepts and patterns can be found in our documentation.
Source: Generally Available: Durable Functions support for Java
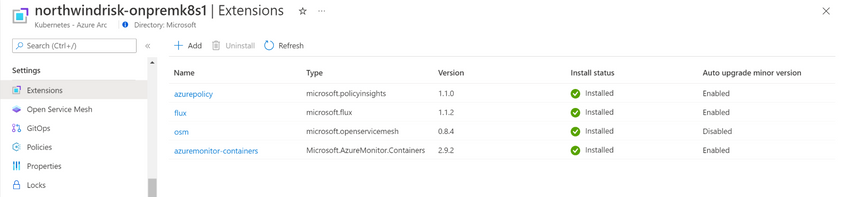
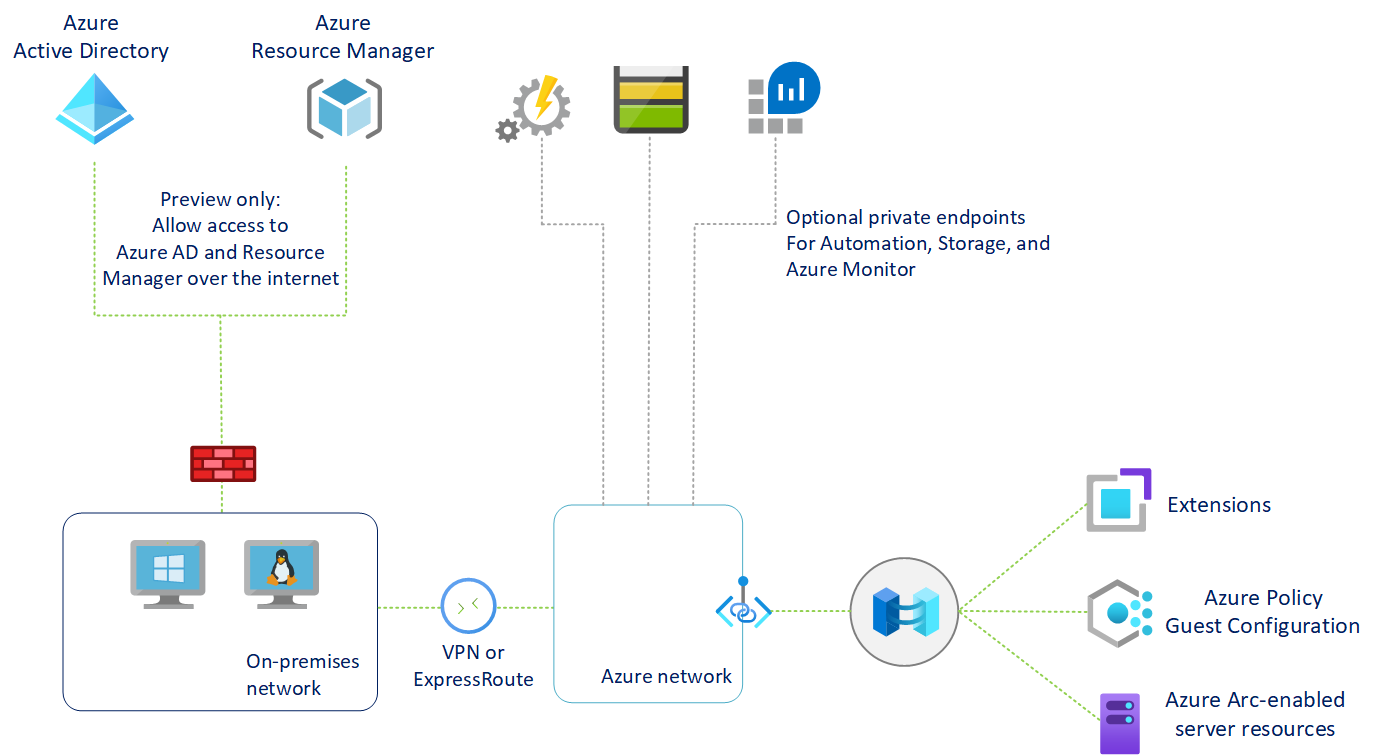
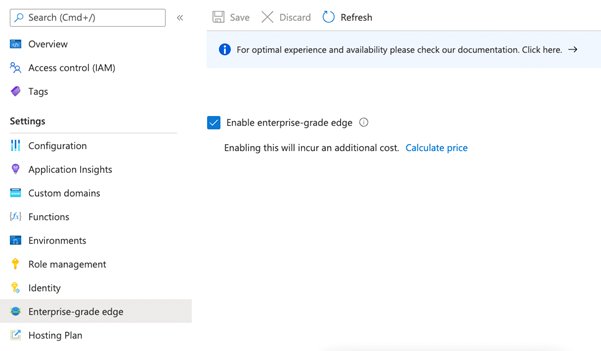
Public preview: Azure Arc enabled Azure Container Apps
The cluster can be on-premises or hosted in a third-party cloud. This approach allows developers to take advantage of the features and developer productivity of Azure Container Apps. Meanwhile it allows IT Administrators to maintain corporate compliance by hosting the application in Hybrid environments.
Azure Container Apps allows developers to rapidly build and deploy microservices and containerized applications. Common uses of Azure Container Apps include, but are not limited to: API endpoints, background or event-driven processing, and running microservices. Applications can dynamically scale within the limits of the Arc-enabled Kubernetes cluster.
By deploying an Arc extension on the Azure Arc-enabled Kubernetes cluster, IT administrators gain control of the underlying hardware and environment, while still enabling the high productivity of Azure PaaS services from within a hybrid environment.
Source: Public preview: Azure Arc enabled Azure Container Apps
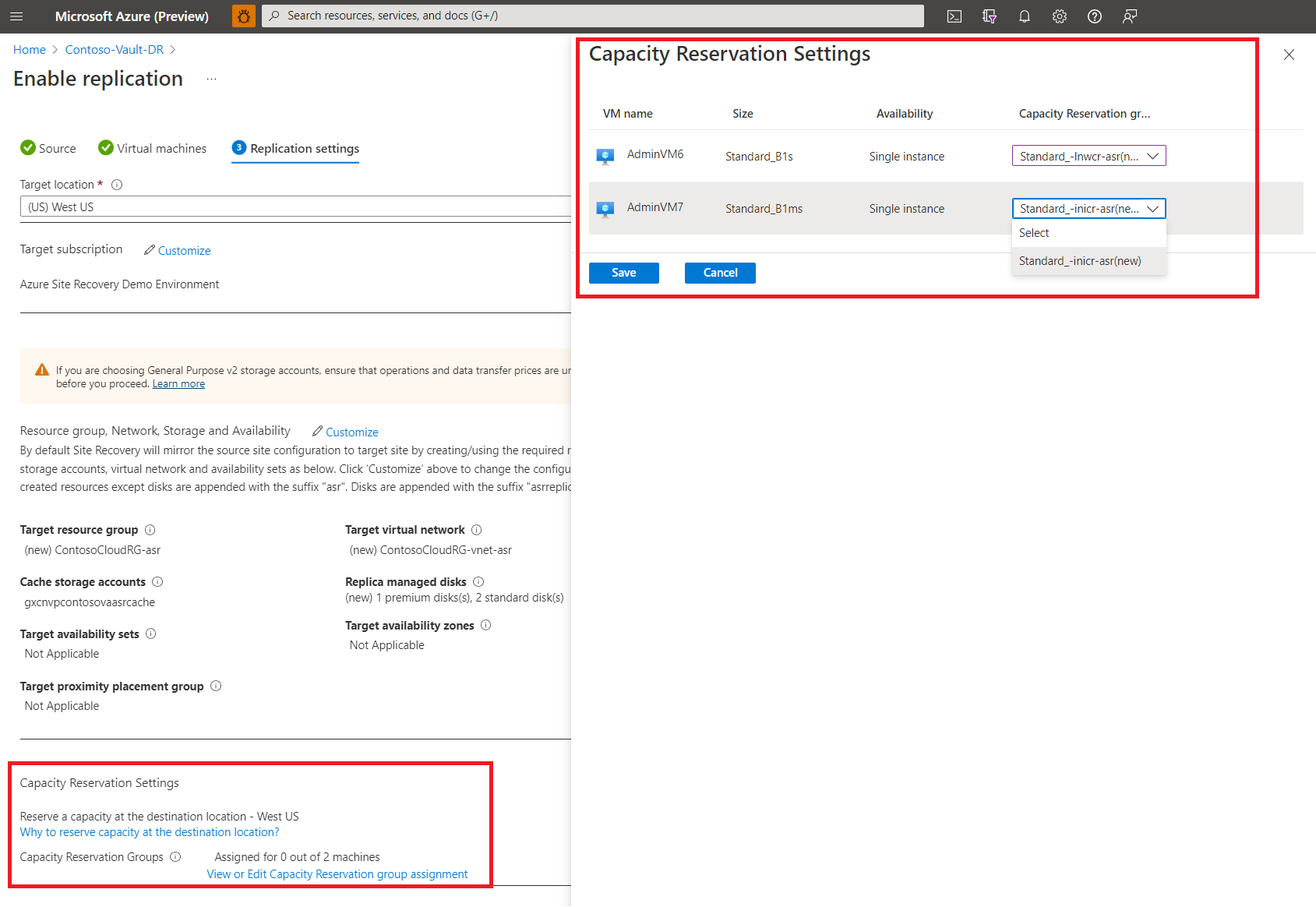
Azure Site Recovery (ASR) has increased its data churn limit by approximately 2.5x to 50 MB/s per disk. With this, you can configure disaster recovery (DR) for Azure VMs having data churn up to 100 MB/s. This helps you to enable DR for more IO intensive workloads.
To opt for the higher churn limit is very easy – you need to select the option High Churn (Public Preview) when enabling the replication. By default, Normal Churn option is selected. If you want to use the higher churn limit for Azure VMs already protected using ASR, you need to disable replication and re-enable replication with the High Churn (Public Preview) option selected. Please note that this feature is only available for Azure-to-Azure scenarios.
Source: Public Preview: Azure Site Recovery Higher Churn Support
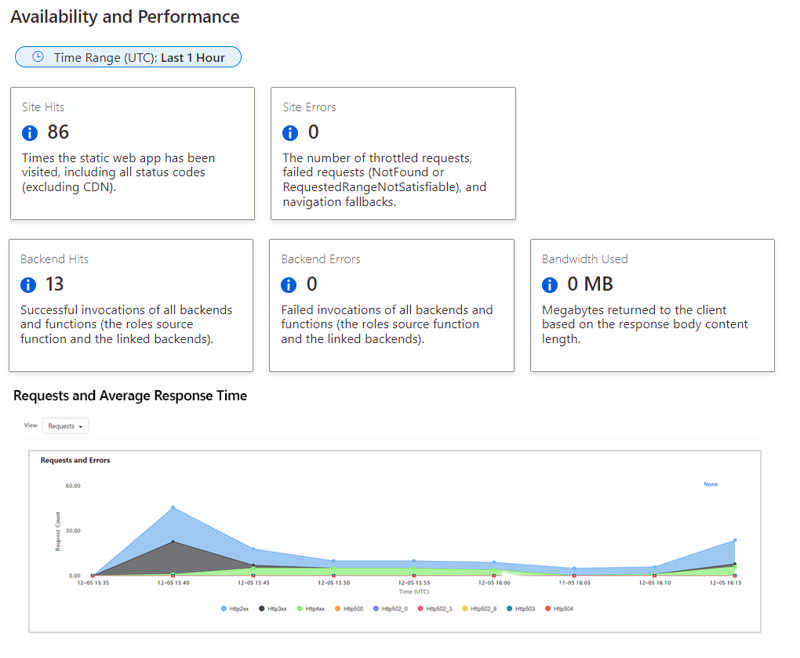
Generally available: Static Web Apps Diagnostics
Azure Static Web Apps Diagnostics is an intelligent tool to help you troubleshoot your static web app directly from the Azure Portal. When issues arise, Static Web Apps diagnostics will help you diagnose what went wrong and will show you how to resolve the issues. This guidance helps you improve the reliability of your site and track its performance.
Enable higher throughput levels for Azure Service Bus premium via two new features in public preview today.
First, we are releasing scaling partitions, allowing the use of partitioning for the premium messaging tier. Service Bus partitions enable messaging entities to be partitioned across multiple message brokers. This means that the overall throughput of a partitioned entity is no longer limited by the performance of a single message broker. Additionally, a temporary outage of a message broker, for example during an upgrade, does not render a partitioned queue or topic unavailable, as messages will be retried on a different partition.
Second, we are making a change to our infrastructure, which will result in more consistent low latency. This is accomplished by switching our storage to a different implementation called local store. During public preview we will create partitioned namespaces using this new feature, but in the future all new namespaces will be created on local store.
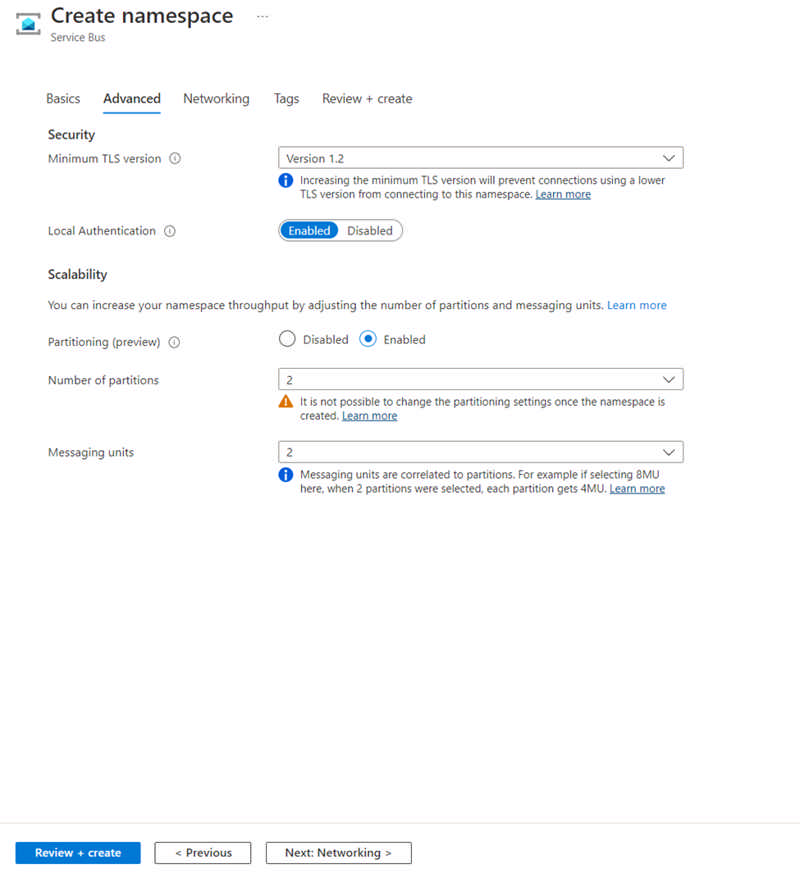
Source: Public preview: Performance improving features for Azure Service Bus premium
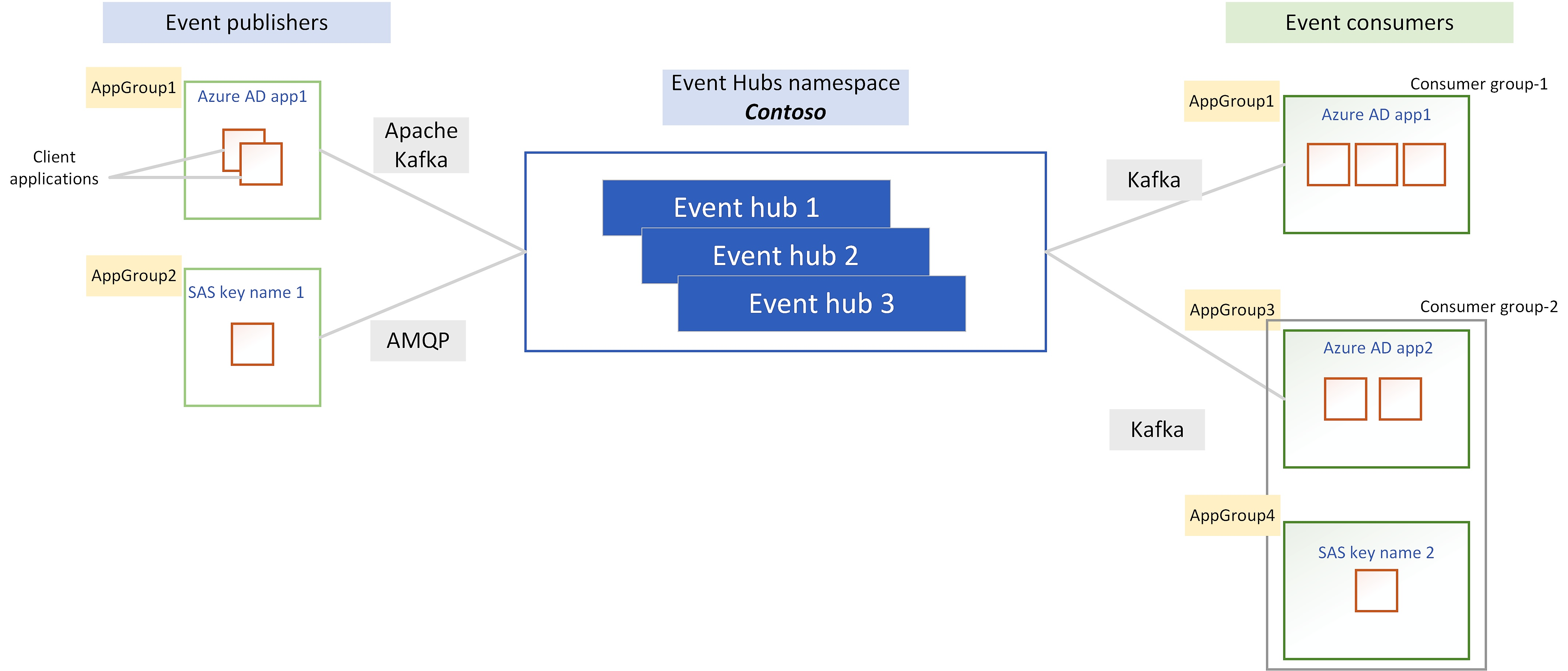
Log compaction is a way of retaining events in Event Hubs. Rather using time based retention, you can use key-based retention mechanism where Event Hubs retrains the last known value for each event key of an event hub or Kafka topic. Event Hubs service runs a compaction job internally and purges old events in a compacted event hub. The partition key that you set with each event is used as the compaction key and users can also mark events that needs to be deleted from the event log by publishing event with a key and null payload.
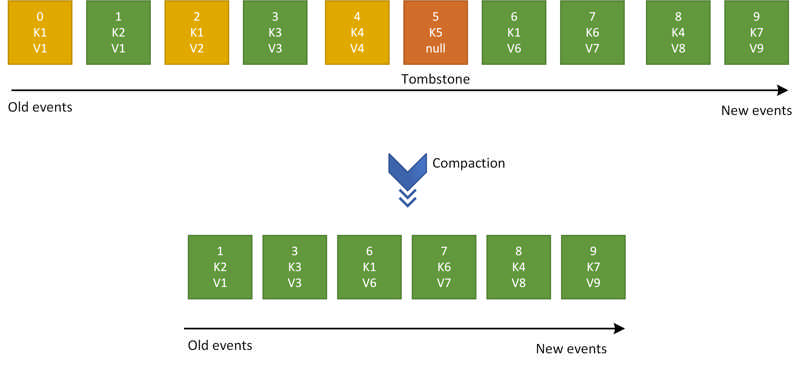
To learn more about log compaction, please check out Log Compaction documentation.
Source: Public preview: Log compaction support in Azure Event Hubs
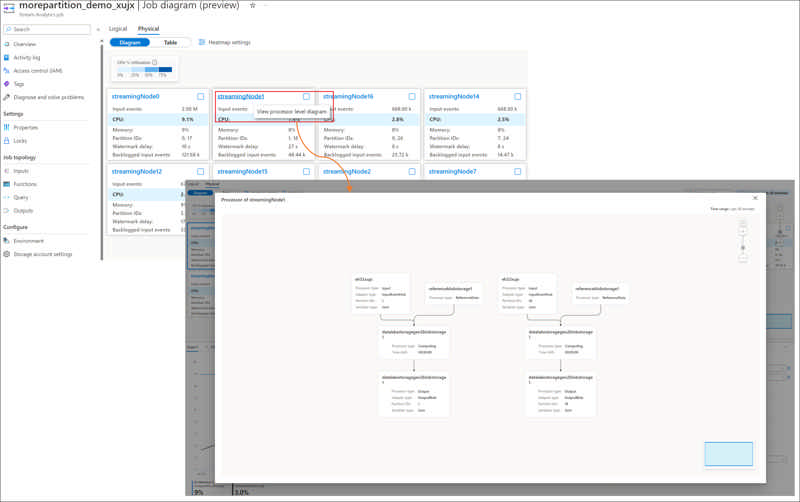
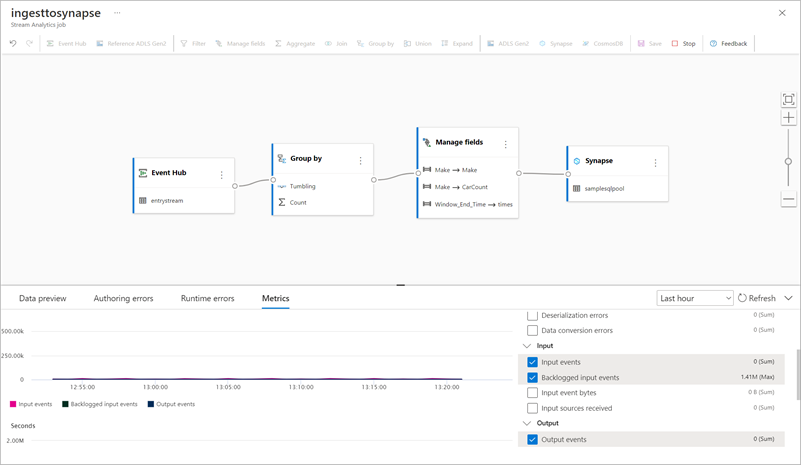
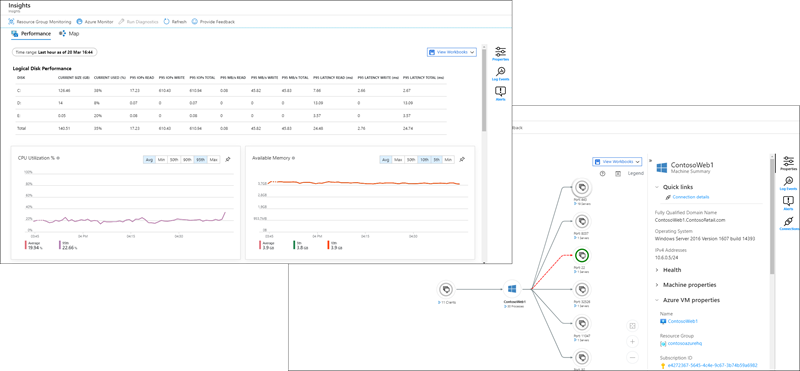
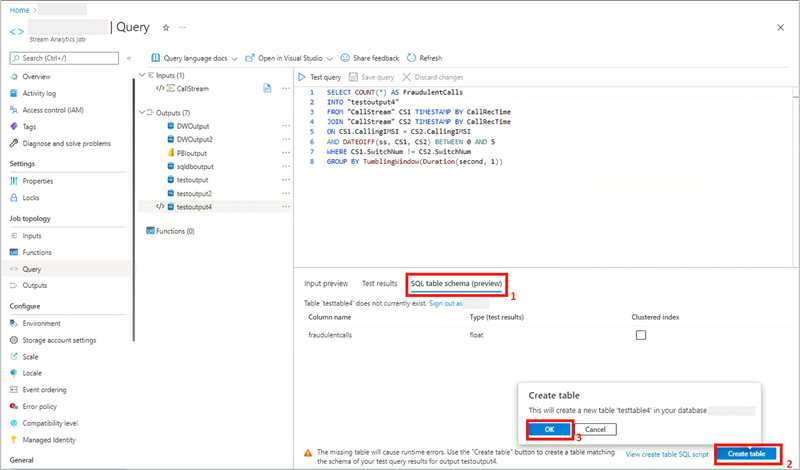
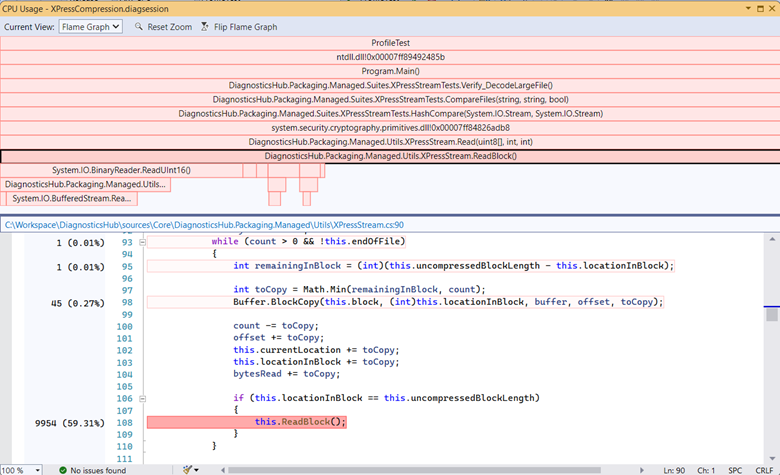
Inside each streaming node of an Azure Stream Analytics job, there are Stream Analytics processors available for processing the stream data. Each processor represents one or more steps in your query. The processor diagram in physical job diagram visualizes the processor topology inside the specific streaming node of your job. It helps you to identify if there is any bottleneck and where the bottleneck is in the streaming node of your job.
Source: Public preview: Processor diagram in Physical Job Diagram for Stream Analytics job troubleshooting
File storage is a critical part of any organization’s on-premises IT infrastructure. As organizations migrate more of their applications and user shares to the cloud, they often face challenges in migrating the associated file data. Having the right tools and services is essential to successful migrations.
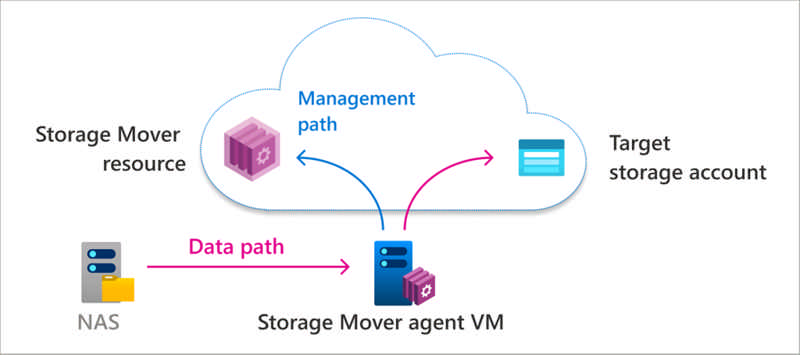
Across workloads, there can be a wide range of file sizes, counts, types, and access patterns. In addition to supporting a variety of file data, migration services must minimize downtime, especially on mission-critical file shares.
Source: Azure Storage Mover–A managed migration service for Azure Storage
We are pleased to announce the general availability of RDP Shortpath for public networks. RDP Shortpath improves the transport reliability of Azure Virtual Desktop connections by establishing a direct UDP data flow between the Remote Desktop client and session hosts. This feature is enabled by default for all customers. We started deploying RDP Shortpath in September and now the feature is 100% rolled out.
What is RDP Shortpath for public networks?
Read more at Azure Daily 2022
We’re announcing that Azure Virtual Desktop has public preview support for Azure Confidential Virtual Machines. Confidential Virtual Machines increase data privacy and security by protecting data in use. The Azure DCasv5 and ECasv5 confidential VM series provide a hardware-based Trusted Execution Environment (TEE) that features AMD SEV-SNP security capabilities, which harden guest protections to deny the hypervisor and other host management code access to VM memory and state, and that is designed to protect against operator access and encrypts data in use.
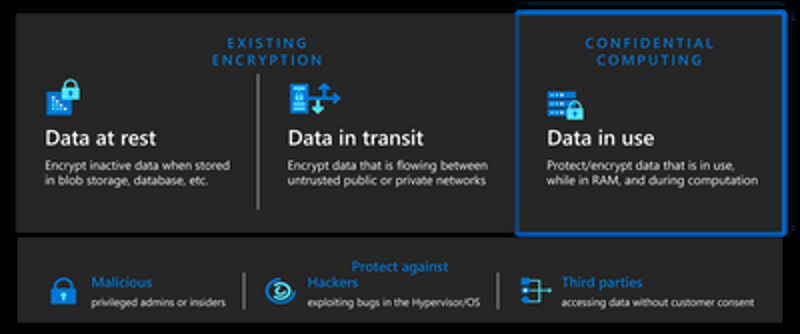
With this preview, support for Windows 11 22H2 has been added to Confidential Virtual Machines. Confidential OS Disk encryption and Integrity monitoring will be added to the preview at a later date. Confidential VM support for Windows 10 is planned.
Read more at Azure Daily 2022
Azure Monitor agent is the way to collect text and IIS files for Log Analytics.
Today Microsoft is happy to introduce the long-awaited Custom Log and IIS Log collection capability. This new capability is designed to enable customers to collect their text-based logs generated in their service or application. Likewise, Internet Information Service (IIS) logs for a customers’ service can be collected and transferred into a Log Analytics Workspace table for analysis. These new collection types will enable customers to migrate from other competing data collection services to Azure Monitor.
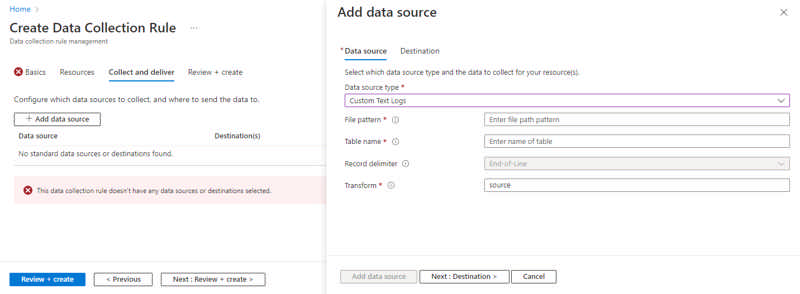
Source: General availability: Azure Monitor agent custom and IIS logs
In this blog, we will present a feature for moving Azure SQL Managed Instance from one to another subnet located in a different virtual network. This capability comes as an enhancement of the existing capability for moving the instance to another subnet.
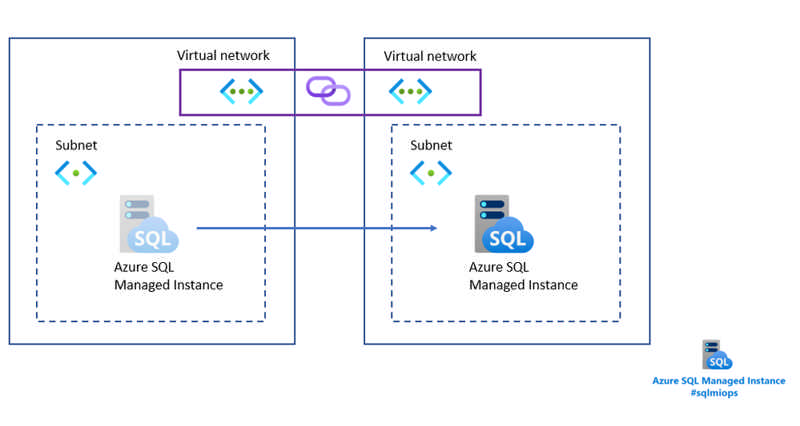
Read more at Azure Daily 2022
Microsoft is excited to announce the public preview of one of our most requested native monitoring features – Azure Virtual Desktop Insights at Scale. This update provides the ability to review performance and diagnostic information across multiple host pools in one view.
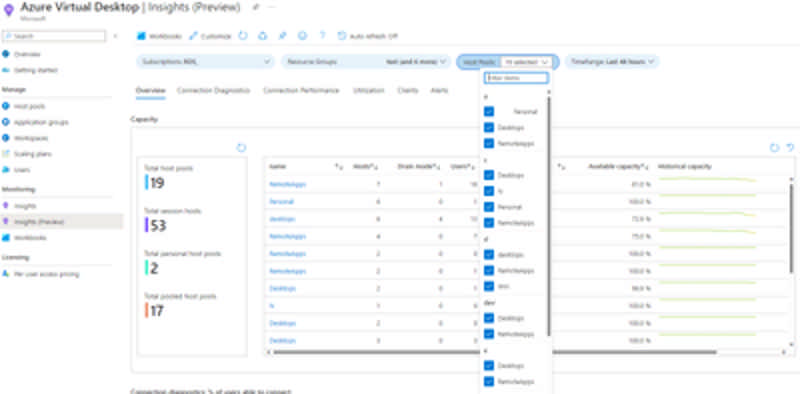
Previously, Azure Virtual Desktop Insights only supported the ability to review information related to a single host pool at a time. In many cases this limited visibility into issues that may have an impact across multiple host pools.
Read more at Azure Daily 2022
Azure App Service is regularly updated to provide new runtime versions to allow web app developers to take advantage of the latest runtime features and security fixes. We are now adding support for Python 3.10, PHP 8.1 and Node 18, giving them a choice of more versions of the latest and fastest growing web app development languages available.
Source: Generally Available: New versions supported for languages and frameworks in Azure App Service
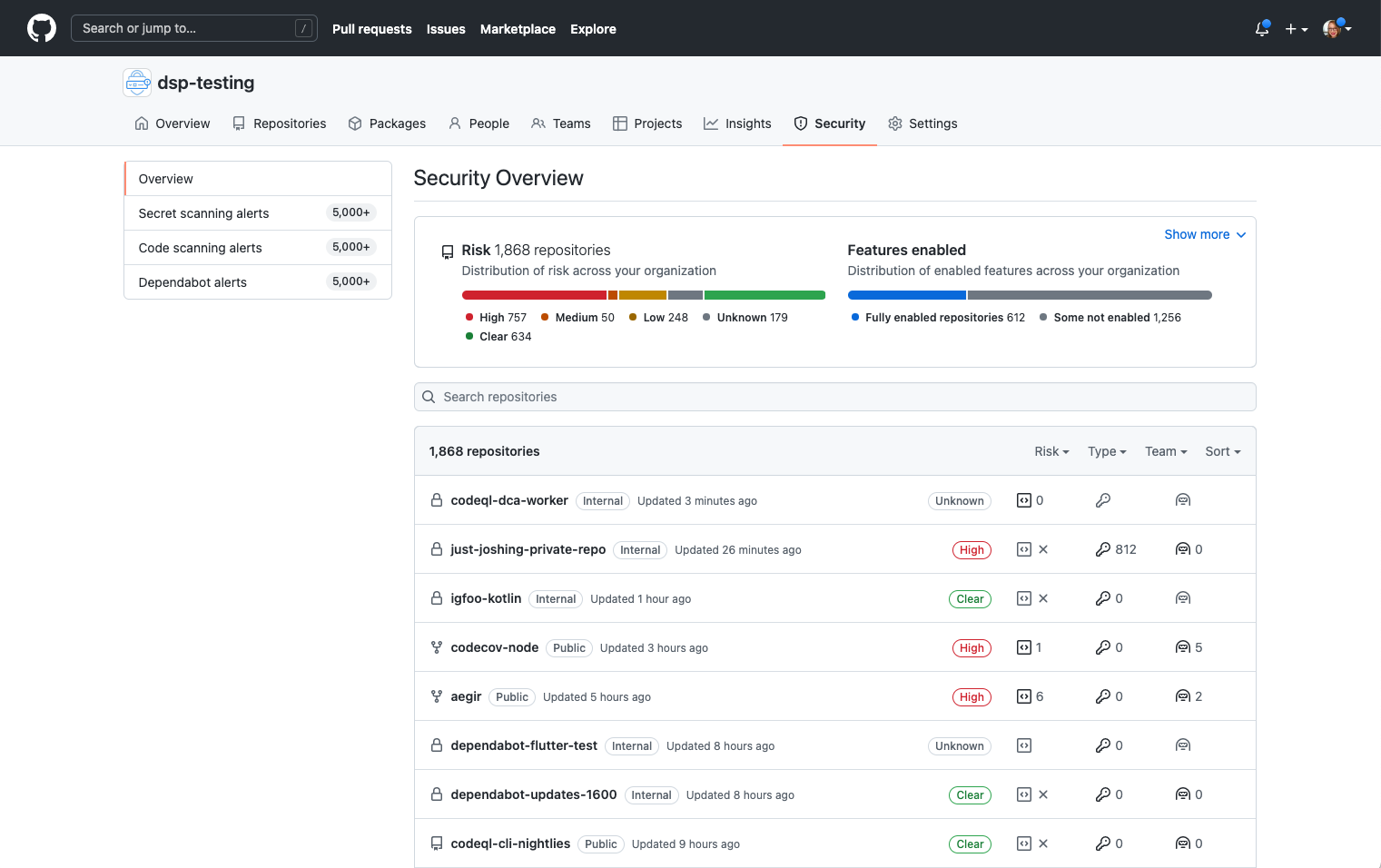
Starting today, GitHub code scanning includes beta support for analyzing code written in Kotlin, powered by the CodeQL engine.
Kotlin is a key programming language used in the creation of Android mobile applications, and is an increasingly popular choice for new projects, augmenting or even replacing Java. To help organisations and open source developers find potential vulnerabilities in their code, we’ve added Kotlin support (beta) to the CodeQL engine that powers GitHub code scanning. CodeQL now natively supports Kotlin, as well as mixed Java and Kotlin projects. Set up code scanning on your repositories today to receive actionable security alerts right on your pull-requests. To enable Kotlin analysis on a repository, configure the code scanning workflow languages to include java. If you have any feedback or questions, please use this discussion thread or open an issue if you encounter any problems.
Kotlin support is an extension of our existing Java support, and benefits from all of our existing CodeQL queries for Java, for both mobile and server-side applications. We’ve also improved and added a range of mobile-specific queries, covering issues such as handling of Intents, Webview validation problems, fragment injection and more.
CodeQL support for Kotlin has already been used to identify novel real-world vulnerabilities in popular apps, from task management to productivity platforms. You can watch the GitHub Universe talk on how CodeQL was used to identify vulnerabilities like these here.
Kotlin beta support is available by default in GitHub.com code scanning, the CodeQL CLI, and the CodeQL extension for VS Code. GitHub Enterprise Server (GHES) version 3.8 will include this beta release.
Source: CodeQL code scanning launches Kotlin analysis support (beta)
Day 0 support for .NET 7.0 on App Service means that developers are immediately unblocked to try, test, and deploy .NET apps targeting the version of .NET accelerating time-to-market on the platform they know and use today. It is expected to be available in Q2 FY23.
Please visit this QuickStart: Deploy an ASP.NET web app to try out .NET 7.0 on App Service.
Source: Generally available Day 0 support for .NET 7.0 on App Service
Public preview: Build and deploy to Azure Container Apps without a Dockerfile from the Azure CLI
Azure Container Apps is a serverless containers platform for microservices. It has a rich set of commands in the Azure CLI for managing and deploying container apps.
The “az containerapp up” command can build and deploy local source code to Azure Container Apps in a single command. Previously, “az containerapp up” required a Dockerfile to build a container image. "az containerapp up” now supports building container images from source code without a Dockerfile.
Popular languages and runtimes, including .NET, Python, and Node.js are supported.
This feature is currently in preview.
Source: Public preview: Build and deploy to Azure Container Apps without a Dockerfile from the Azure CLI
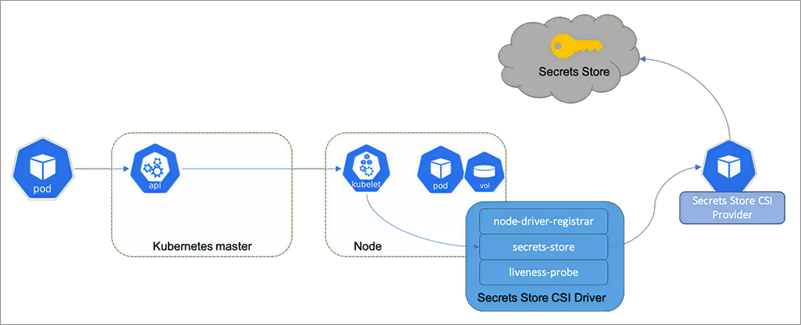
Azure offers a unique capability of mounting Blob Storage (or object storage) as a file system to a Kubernetes pod or application using BlobFuse or NFS 3.0 options. This allows you to use blob storage with a number of stateful Kubernetes applications including HPC, Analytics, image processing, and audio or video streaming. Not only that, if your application ingests data into Data Lake storage on Azure Blobs, you can now directly mount and use it with AKS. Previously, you had to manually install and manage the lifecycle of the open-source Azure Blob CSI driver including deployment, versioning, and upgrades.
You can now use the Azure Blob CSI driver as a managed addon in AKS with built in storage classes for NFS and BlobFuse, reducing the operational overhead and maximizing time to value.
Source: Generally available: Azure Blob CSI driver support in AKS
Azure Cosmos DB for PostgreSQL now supports cross-region asynchronous replication of data from one cluster to another cluster. This feature allows read-heavy workloads to scale out and load balance across independently configured read-only replicas which can also be promoted to independent read-write clusters. These features can provide you with increased read performance and more precise resource utilization for better cost efficiency and higher availability through support for cross-region disaster recovery.
Source: General availability: Cross-region read replicas for Azure Cosmos DB for PostgreSQL
For the first time ever, Go language (v1.18 and v1.19) is natively supported on Azure App Service, helping developers innovate faster using the best fully managed app platform for cloud-centric web apps. The language support is available as an experimental language release on Linux App Service in November 2022.
Source: Public preview: Go language support on Azure App Service
Generally available: Azure Blob Storage integration with Azure Cosmos DB for PostgreSQL
Using the pg_azure_storageextension, you can interact with Azure Blob Storage containers directly from Azure Cosmos DB for PostgreSQL. Container contents can be listed and fetched using the COPY command and a flexible API. Save time implementing custom data upload pipelines without requiring additional infrastructure and leverage efficient networking between Azure services using a flexible API to make complex data pipelines easier to automate. Currently supported formats include .tsv, .csv, binary, text, and transparent decompression of .gzip compressed file.
Source: Generally available: Azure Blob Storage integration with Azure Cosmos DB for PostgreSQL
Azure Daily 2022 - Nov 23, 2022
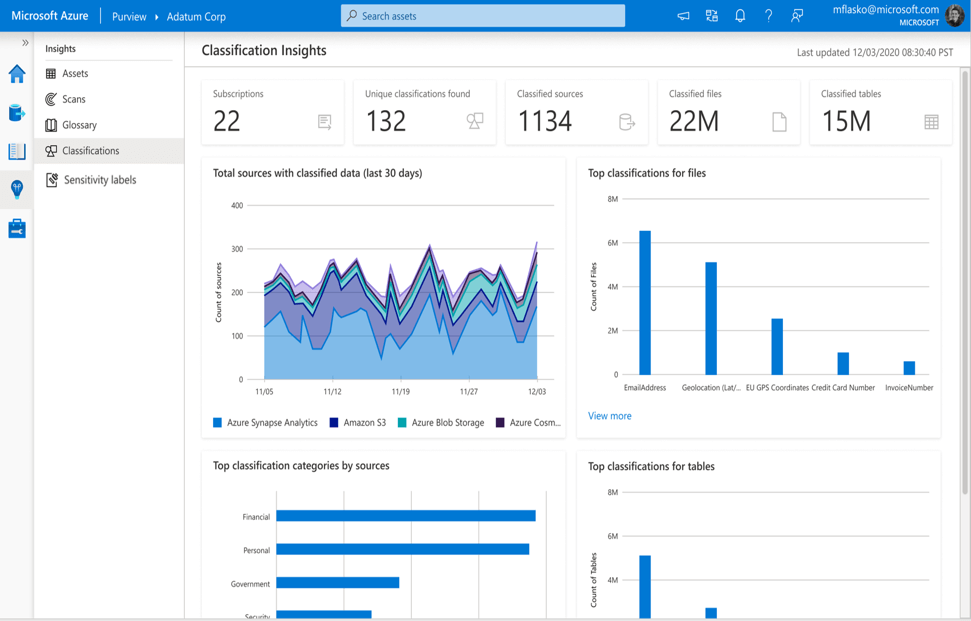
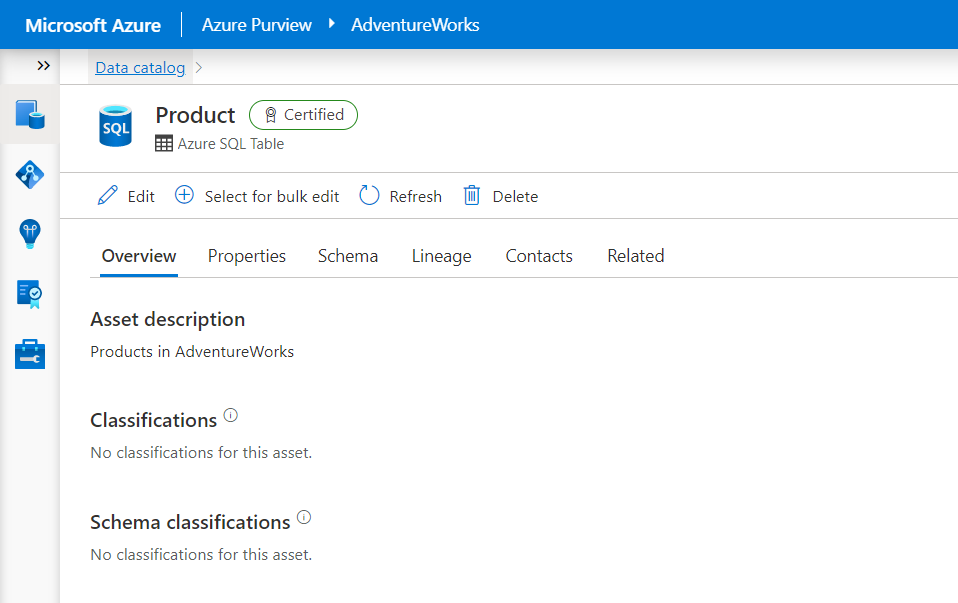
In this article you will find an overview of all the new metadata that was added to support customers using external data and access Policies from Microsoft Purview. You will find this interesting if you are in a technical role and have access to a SQL database, for example as a DBA or developer or need to create reports on who has access to your systems.
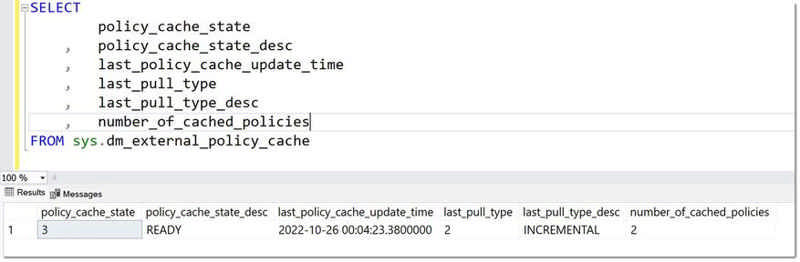
Read more at Azure Daily 2022
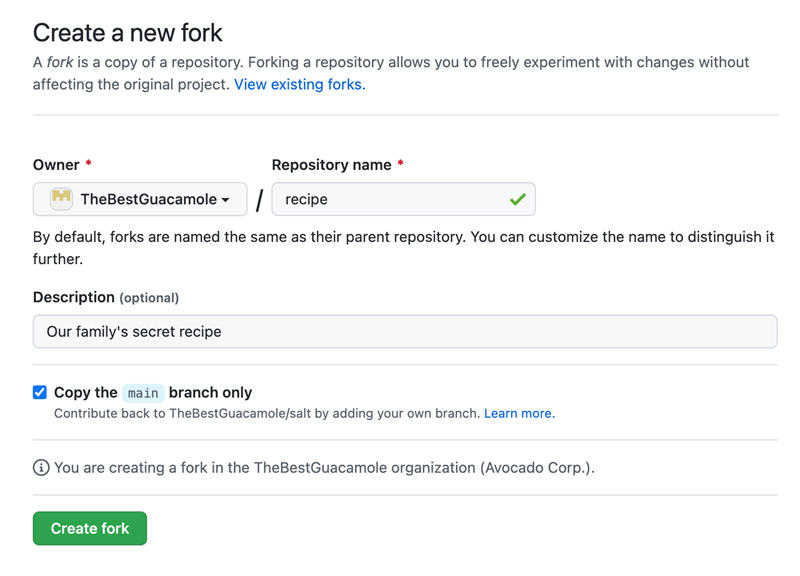
Today, GitHub is introducing calendar-based versioning for the REST API to give API integrators a smooth migration path and plenty of time to update their integrations when we need to make occasional breaking changes to the API.
You can learn more in today’s blog post and on the new “API Versions” page in our docs.
If you’re using the REST API, you don’t need to take any action right now. We’ll get in touch with plenty of notice before we drop support for any old versions.
A new version of Azure Quota REST API support for service limits (quotas) is now available in Public preview. Use this new feature to programmatically manage the service limits (quotas) of Azure Virtual Machines (cores/vCPU), Networking, Azure HPC Cache and Azure Purview services. Take advantage of this capability to query current usage and quotas for the supported resources and update these limits, when needed.
For the resources currently supported, the Quota API provides an easier way to quickly get current limits, current usage, and request quota increases.
Request quota increases and enumerate current quotas by subscription, provider, and location seamlessly.
Source: Public Preview: Use Azure Quota Rest APIs to manage service limits (quotas)
We are delighted to announce the preview of Cross Subscription Restore of Azure Virtual machines. Cross Subscription Restore allows you to restore Azure Virtual Machine, through create new or restore disks, to any subscription (honoring the RBAC capabilities) from the restore point created by Azure Backup. By default, Azure Backup restores to the same subscription where the restore points are available. With this new feature, you can gain the flexibility of restoring to any subscription under your tenant if restore permissions are available. You can trigger Cross Subscription Restore for managed Azure Virtual Machines only from vault and not from snapshots. Cross Subscription Restore is also supported for Restore with Managed System Identities (MSI). It is unsupported for Encrypted Azure VMs and Trusted Launch VMs.
Learn more about Cross Subscription Restore.
Source: Public preview: Cross Subscription Restore for Azure Virtual Machines
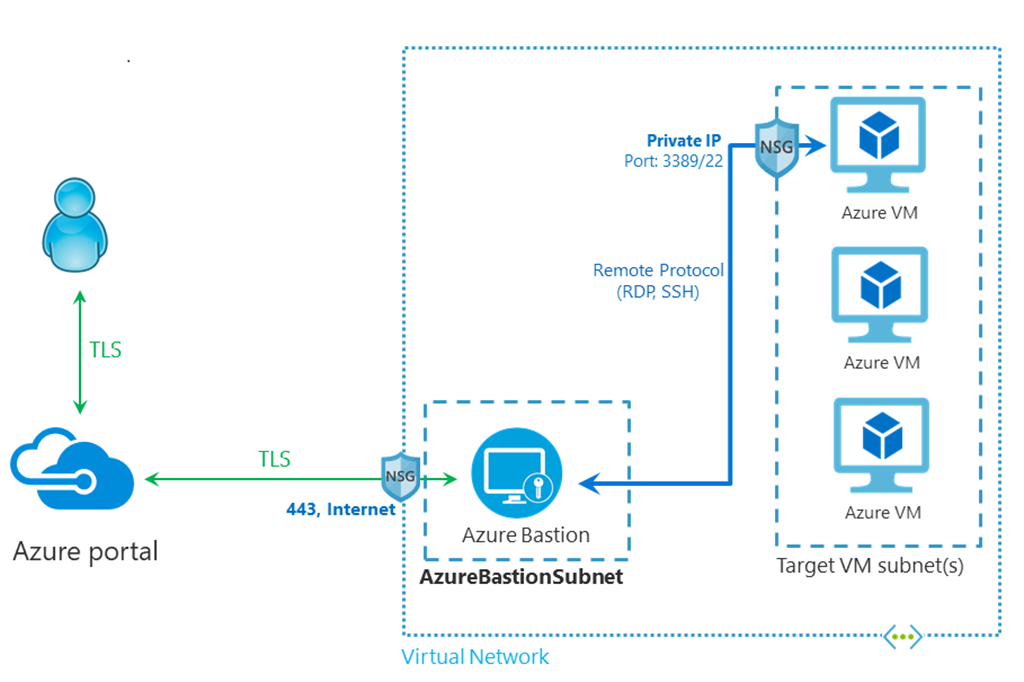
With the new Azure Bastion shareable links feature in public preview and included in Standard SKU, you can now connect to a target resource (virtual machine or virtual machine scale set) using Azure Bastion without accessing the Azure portal.
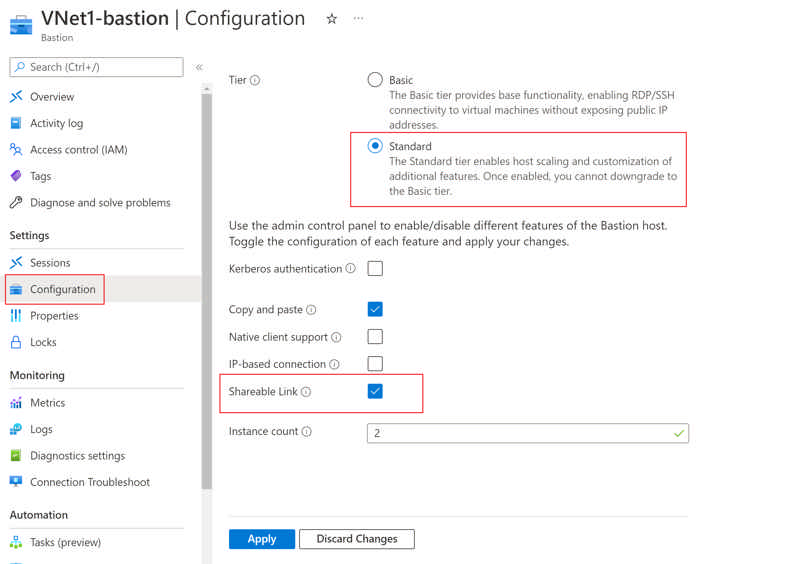
This feature will solve two key pain points:
- Administrators will no longer have to provide full access to their Azure accounts to one-time VM users—helping to maintain their privacy and security.
- Users without Azure subscriptions can seamlessly connect to VMs without exposing RDP/SSH ports to the public internet.
Source: Public preview: Azure Bastion now support shareable links
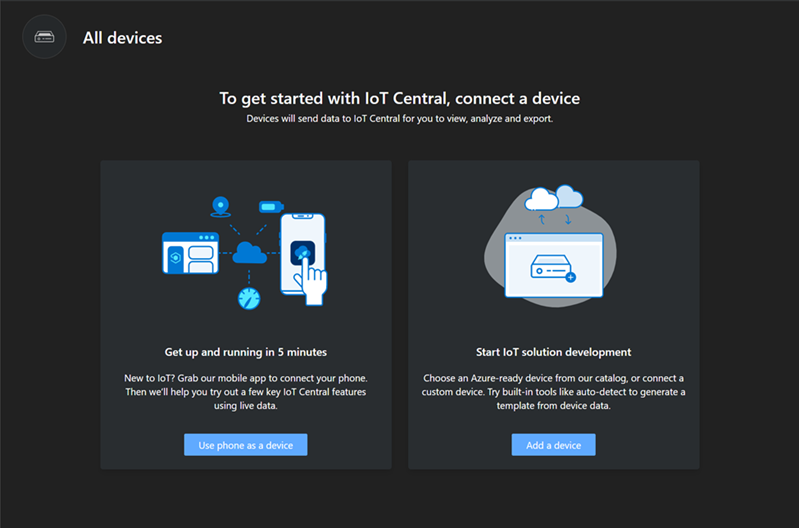
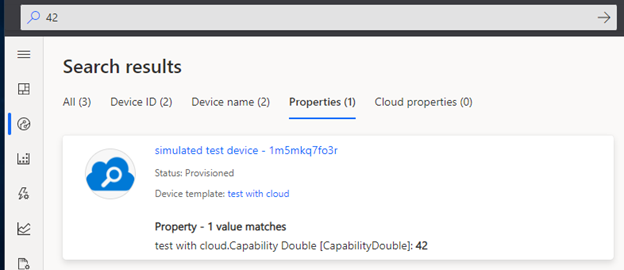
Azure IoT Hub now supports the ability to setup an Azure Cosmos DB account as a custom routing endpoint. This will help route device data from IoT Hub to Azure Cosmos DB directly. The feature also allows the configuration of Synthetic Partition Keys for writing data into Azure Cosmos DB which helps in optimized querying when working with large-scale data.
Many IoT solutions require extensive downstream data analysis and pushing data into hyperscale databases. For example, IoT implementations in manufacturing and intelligent transport systems require hyperscale databases with extremely high throughput to process the continuous stream of data. Traditional SQL based relational databases cannot scale optimally and also become expensive once data scale increases. Azure Cosmos DB is best suited for such cases where the data needs to be analyzed while it is being written.
Source: Public preview: Add an Azure Cosmos DB custom endpoint in IoT Hub
Earlier this year, we announced our vision to empower any developer to become a space developer through Azure. With over 90 million developers on GitHub, we have created a powerful ecosystem and we are focused on empowering the next generation of developers for space. Today, we are announcing a crucial step towards democratizing access to space development, with the preview release of Azure Orbital Space SDK (software development kit)—a secure hosting platform and application toolkit designed to enable developers to create, deploy, and operate applications on-orbit.
By bringing modern cloud-based applications to spacecrafts we not only increase the efficiency, value, and speed of insights from space data but also increase the value of that data through the optimization of ground communication.
Source: Any developer can be a space developer with the new Azure Orbital Space SDK
By using .NET 7 for your entire stack, you can leverage the latest language and runtime improvements in .NET, and you can seamlessly share code between your Blazor WebAssembly app, Azure Functions, and other .NET applications.
For your app’s frontend, Static Web Apps can now automatically build and deploy .NET 7.0 Blazor WebAssembly apps. For backend APIs, you can build and deploy .NET 7.0 Azure Functions with your static web apps.
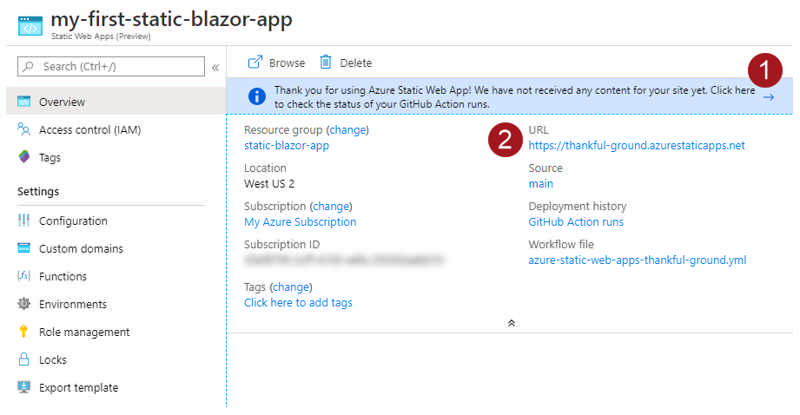
Azure Static Web Apps support for .NET 7.0 follows the .NET 7.0 lifecycle. To learn more, please refer to the .NET support policy.
Source: Generally available: Azure Static Web Apps now fully supports .NET 7
Azure Quota REST API support for service limits (quota) is now available in preview for you to manage your quota programatically. Use Azure REST Quota APIs to manage service limits (quotas) for Azure Virtual Machines (cores/vCPU), Networking, Azure HPC Cache, and Azure Purview services.
For the resources currently supported, the Quota API provides an easier way to quickly get current limits, current usage, and request quota increases.
Request quota increases and enumerate current quotas by subscription, provider, and location seamlessly.
Source: Public preview: Use Azure Quota REST APIs to manage service limits (quotas)
With Static Web Apps, you can now configure Azure Pipelines to deploy your application to preview environments. The Azure DevOps task for Azure Static Web Apps intelligently detects and builds your app’s frontend and API and deploys the entire application to Azure. You can fully automate the testing and delivery of your software in multiple stages all the way to production.
Azure Static Web Apps provides globally distributed content hosting and serverless APIs powered by Azure Functions. It also includes everything you need to run a full-stack web app, including support for custom domains, free SSL certificates, authentication/authorization, and preview environments.
This feature is now generally available.
Source: Generally available: Static Web Apps support for preview environments in Azure DevOps
Azure Front Door supports upgrading from Standard to Premium tier without downtime. Azure Front Door Premium supports advanced security capabilities and has increased quota limit, such as managed Web Application Firewall rules and private connectivity to your origin using Private Link.
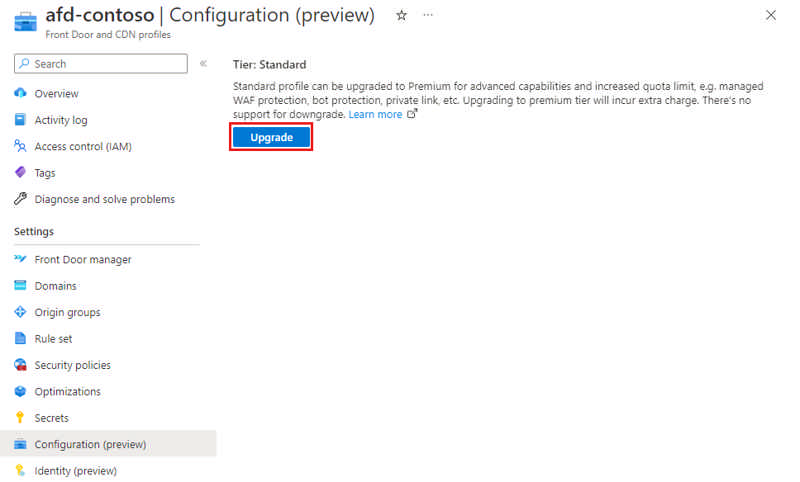
Source: Public preview: Upgrade from Azure Front Door Standard to Premium tier
Azure Front Door now supports managed identities generated by Azure Active Directory to allow Front Door to easily and securely access other Azure AD-protected resources such as Azure Key Vault. This feature is in addition to the AAD Application access to Key Vault that is currently supported.
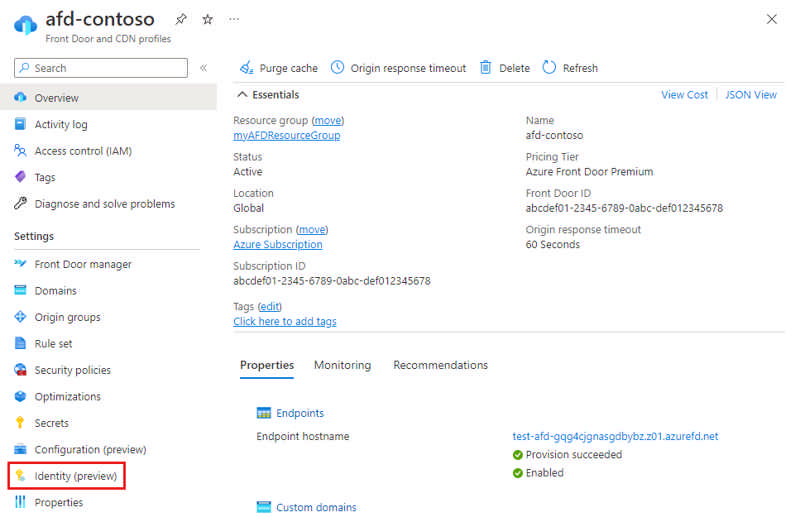
Source: Public preview: Azure Front Door integration with managed identities
In March of this year, Microsoft announced the general availability of two new Azure Front Door tiers. Azure Front Door Standard and Premium are our native, modern cloud content delivery network (CDN) catering to both dynamic and static content delivery acceleration with built-in turnkey security and a simple and predictable pricing model.
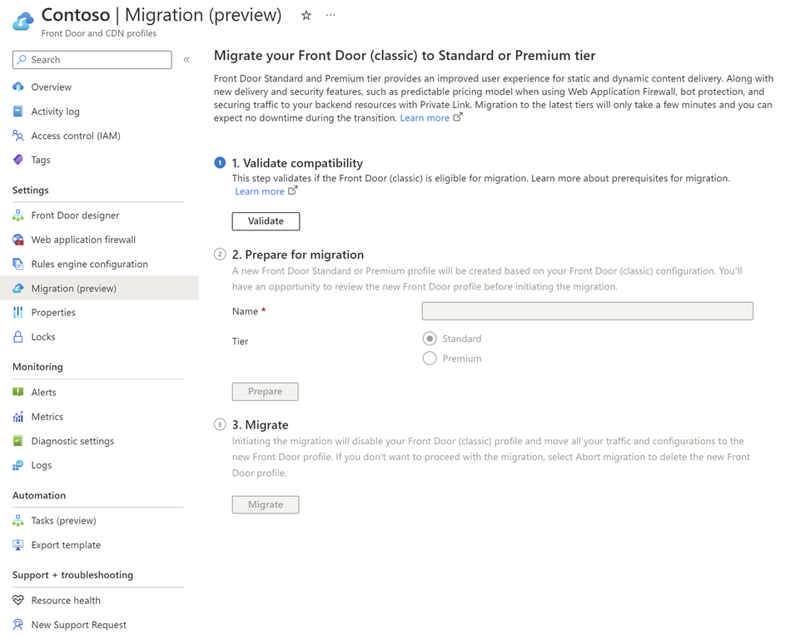
The migration capability enables you to perform a zero-downtime migration from Azure Front Door (classic) to Azure Front Door Standard or Premium in just three simple steps or five simple steps if your Azure Front Door (classic) instance has custom domains with your own certificates. The migration will take a few minutes to complete depending on the complexity of your Azure Front Door (classic) instance, such as number of domains, backend pools, routes, and other configurations.
Source: Public preview: Azure Front Door zero downtime migration
You will be able to usedependencies and inter-correlations between up to 300 different signals and now easily integrate the multivariate time series anomaly detection capabilities into predictive maintenance solutions, artificial intelligence for IT operation monitoring solutions for complex enterprise software, or business intelligence tools. Through the anomaly results that are detected by this feature, you will not only know when there is an anomaly before a disaster happens, but also get the contribution rank of anomalous variables, which will help save time and effort to analyze root cause.
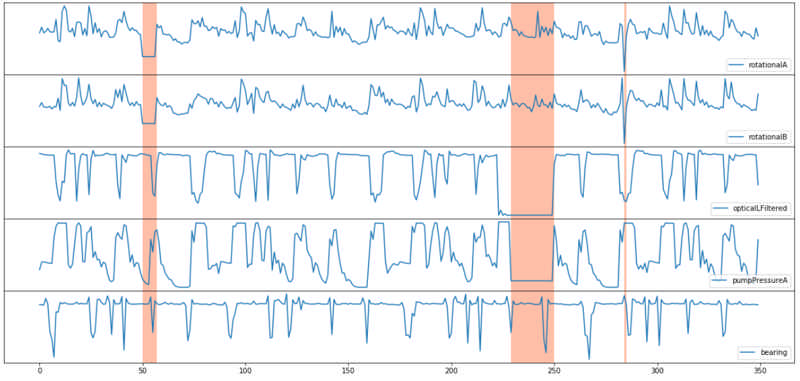
Source: General availability: Multivariate Anomaly Detection
When you deploy a site to Azure Static Web Apps, each pull request against your production branch will generate a preview deployment available at a temporary URL. This can be configured in the GitHub Actions workflow by enabling deployment from branches or by specifying a deployment environment name.
To deploy non-production branches to a preview environment, you are required to update the GitHub workflow to run when a push is made to the specific branches and define the production_branch property in the build_and_deploy_job configuration.
Alternatively, you can push changes to a named preview environment by configuring a deployment_environment property in the workflow.
Source: Generally available: Static Web Apps support for stable URLs for preview environments
The new Virtual Machine software reservations enable savings on your Virtual Machine software costs when you make a one- to three-year commitment for plans offered by third-party publishers such as Canonical, Citrix, and Red Hat.
- You can choose to pay monthly or up-front
- You can change the size of the deployed Virtual Machine, and Microsoft handles the application of reservation benefits and overage charges
- You do not have to redeploy your workloads to use the reservation benefits
Source: General availability: Virtual Machine software reservations
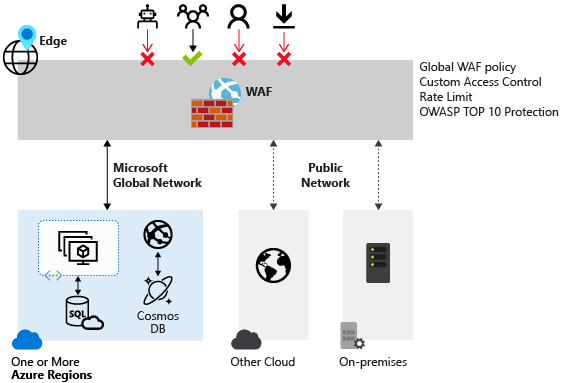
We are announcing the general availability of the Default Rule Set 2.1 (DRS 2.1) on Azure's global Web Application Firewall (WAF) running on Azure Front Door. This rule set is available on the Azure Front Door Premium tier.
DRS 2.1 is baselined off the Open Web Application Security Project (OWASP) Core Rule Set (CRS) 3.3.2 and includes additional proprietary protections rules developed by Microsoft Threat Intelligence team. As with previous DRS releases, DRS 2.1 rules are also tailored by Microsoft Threat Intelligence Center (MSTIC). The MSTIC team analyzes Common Vulnerabilities and Exposures (CVEs) and adapts the CRS ruleset to address those issues while also reducing false positives to our customers.
Source: General availability: Default Rule Set 2.1 for Azure Web Application Firewall
Logic Apps Standard VS Code Extension now allows you to export groups of logic apps workflows deployed to Azure, either in Consumption SKU or under an Integration Service Environment (ISE) as a local Logic Apps Standard project, allowing you to locally test the exported logic apps and either deploy directly to Azure or push the project to your preferred source control repository.
The tool will also generate ARM templates to support the deployment of a Logic App Standard application and any associated Azure connectors via script, parameterize your connections configuration – simplifying the move between environments, and deploy new instances to your Azure connections, so local testing don’t impact existing applications.
To learn more about the tool, including how to install and a walkthrough of the export process, follow one of the paths below:
- Exporting Consumption Workflows to Logic Apps Standard
- Exporting ISE workflows to Logic Apps Standard
Source: Public preview: Exporting ISE and Consumption Logic Apps to Standard SKU
As part of our commitment to delivering the best possible value for Azure confidential computing, we're announcing the support to create confidential VMs using Ephemeral OS disks. This enables customers using stateless workloads to benefit from the trusted execution environments (TEEs). Trusted execution environments protect data being processed from access outside the trusted execution environments.
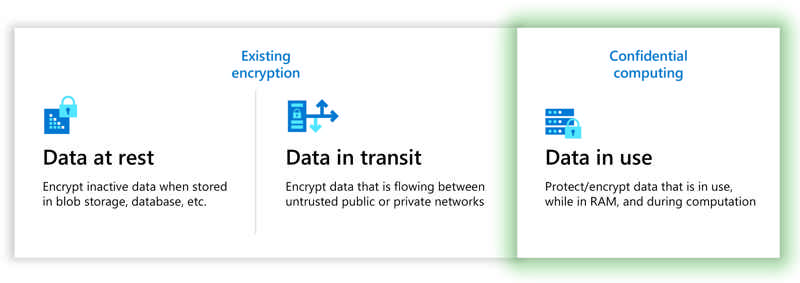
Source: General availability: Ephemeral OS disk support for confidential virtual machines
Several enhancements have been made to the passive geo-replication functionality offered on the Premium tier of Azure Cache for Redis. New metrics are available for you to better track the health and status of your geo-replication link, including statistics around the amount of data that is waiting to be replicated. With this feature, you can now initiate a failover between geo-primary and geo-replica caches with a single click or CLI command, eliminating the hassle of manually unlinking and relinking caches. A global cache URL is also now offered that will automatically update your DNS records after geo-failovers are triggered, allowing your application to only manage one cache address.
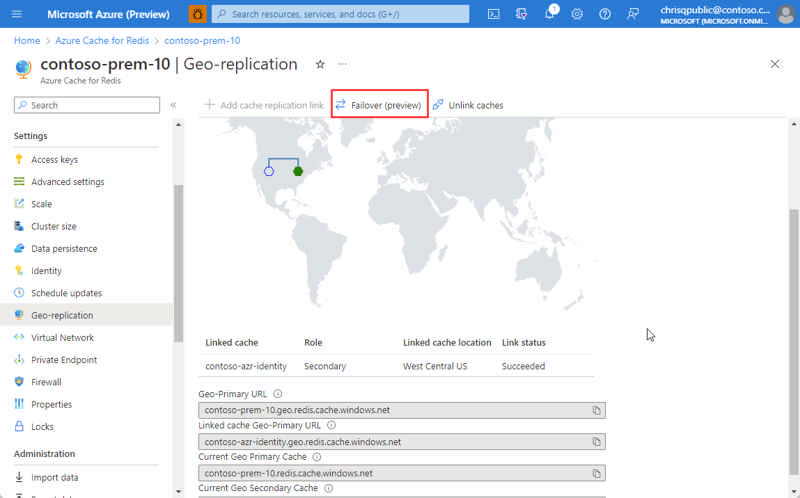
Source: Public preview: Improved passive geo-replication for Azure Cache for Redis
Customers can now deterministically restrict their workflows to run on a specific set of runners using the names of their runner groups in the runs-on key of their workflow YAML. This prevents the unintended case where your job runs on a runner outside your intended group because the unintended runner shared the same labels as the runners in your intended runner group.
Example of the new syntax to ensure a runner is targeted from your intended runner group:
runs-on:
group: my-group
labels: [ self-hosted, label-1 ]In addition to the workflow file syntax changes, there are also new validation checks for runner groups at the organization level. Organizations will no longer be able to create runner groups using a name that already exists at the enterprise level. A warning banner will display for any existing duplicate runner groups at the organization level. There's no restriction on the creation of runner groups at the enterprise level.
This feature change applies to enterprise plan customers as only enterprise plan customers are able to create runner groups.
Source: GitHub Actions: Restrict workflows to specific runners using runner group names
Beginning in November, Databricks is rolling out a new compute option called Databricks SQL Pro, joining the SQL product family of Classic and Serverless. Like Serverless SQL, SQL Pro includes performance and integration features that expand the SQL experience on the Lakehouse Platform. The primary difference is that SQL Pro keeps compute in the customer's account.
Azure Databricks SQL Pro’s features include:
- Predictive I/O - Predictive I/O boosts query performance by leveraging the years of experience Databricks has in building large AI/ML systems to make the lakehouse a more intelligent data warehouse
- Applying deep learning techniques to our data lakehouse
- Determining the most efficient access pattern to read data
- For select queries, Predictive I/O calculates probabilities to anticipate where the next row match will occur, only reading that data from cloud storage
- Native Geospatial Features - 30+ built-in H3 expressions for geospatial processing and analysis in Photon-enabled clusters, available in SQL, Scala, and Python
- Query federation - Databricks Warehouse now supports the ability to query live data from various databases through federation capability. Query federation allows BI applications to integrate data in the lakehouse and external data sources, providing a rich query experience
- Workflows integrations - Invoke DBSQL tasks like queries, alerts, and running dashboards from within Databricks Workflows
Many more feature and performance improvements are on the way, such as Materialized Views, and Python UDFs. SQL Pro is generally available everywhere Databricks SQL Classic is available.
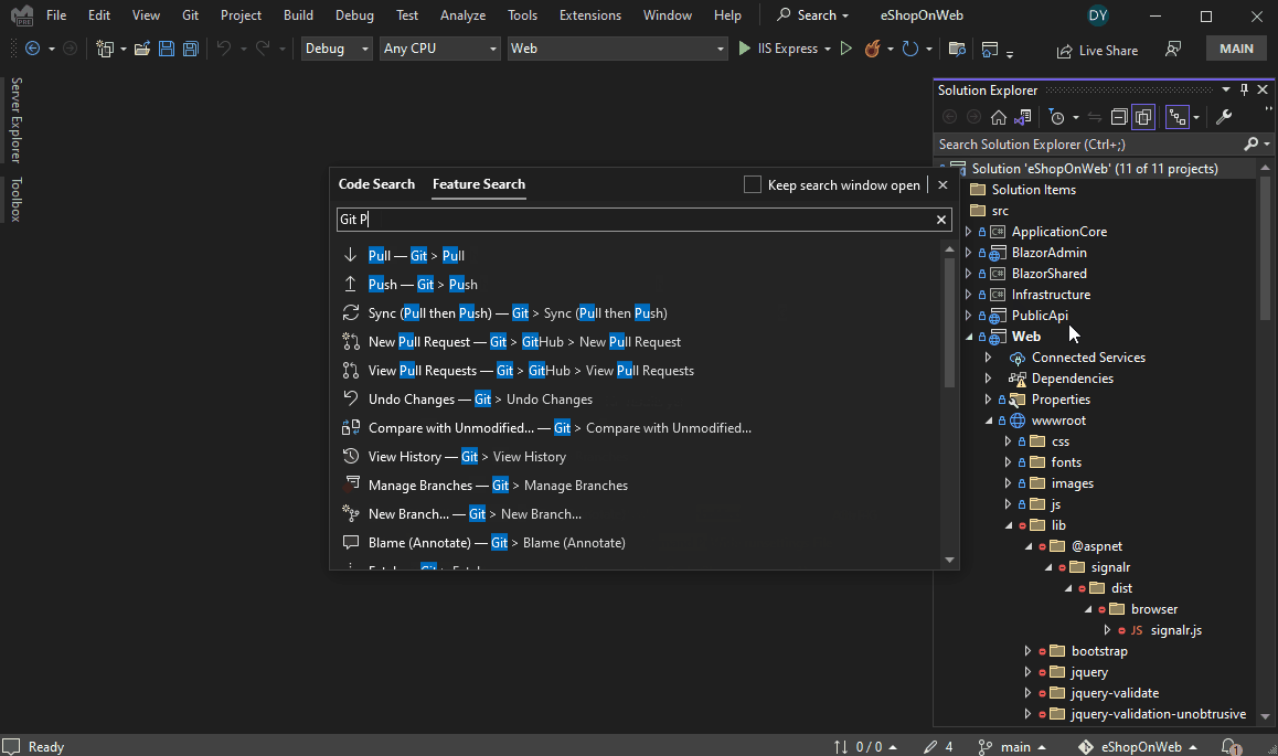
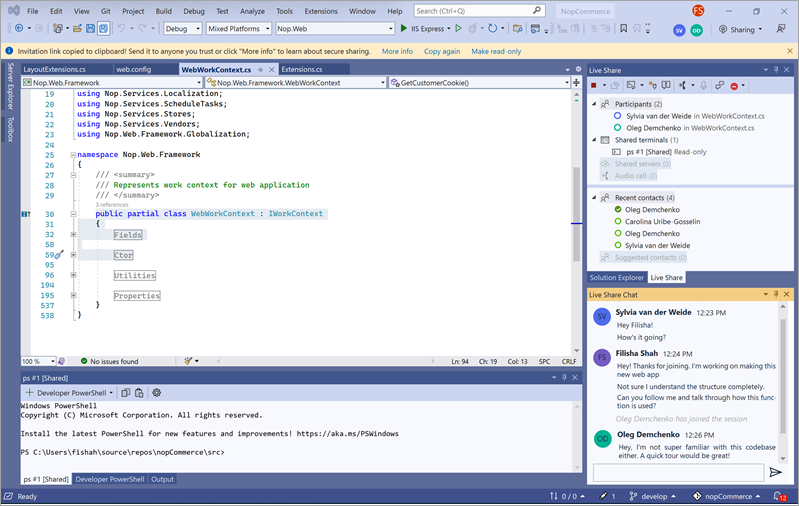
We’re introducing a new way to learn about Git, GitHub, and version control in Visual Studio – an email learning series with actionable challenges and a repository to practice your skills! We found from our Happiness Tracking Survey that 34% of our VS developers aren’t using any form of version control. While GitHub makes collaboration easy, even smaller teams or solo developers can boost their productivity and code management with version control. We’ll teach you how to back up your code, sync across devices, rollback breaking changes, and more within the IDE. Sign up for the new and improved Getting Started with GitHub in Visual Studio series and master GitHub in short lessons over the next four weeks.
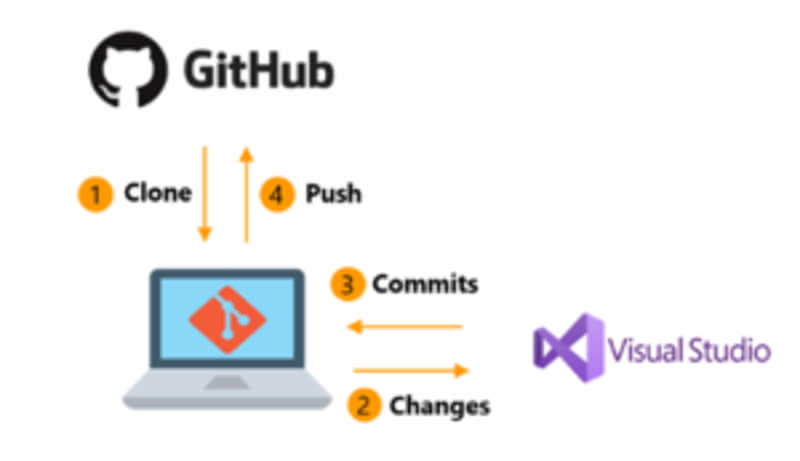
Source: Learning Series: Get started with GitHub in Visual Studio -
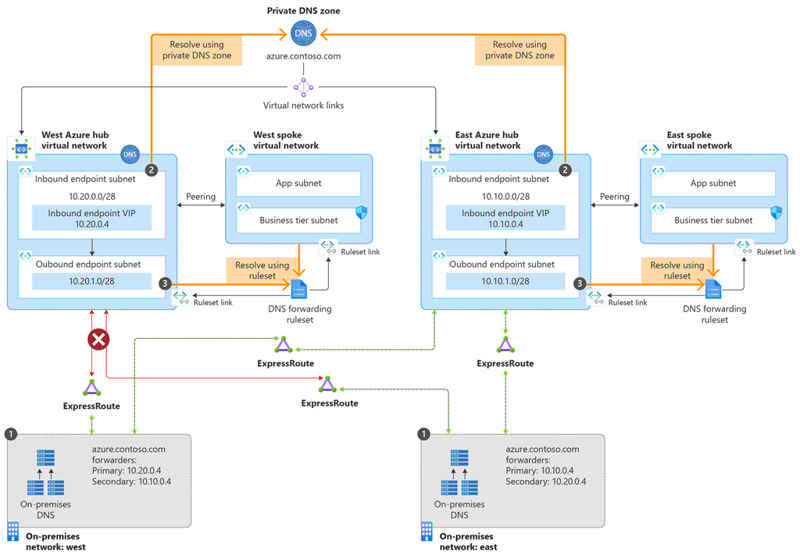
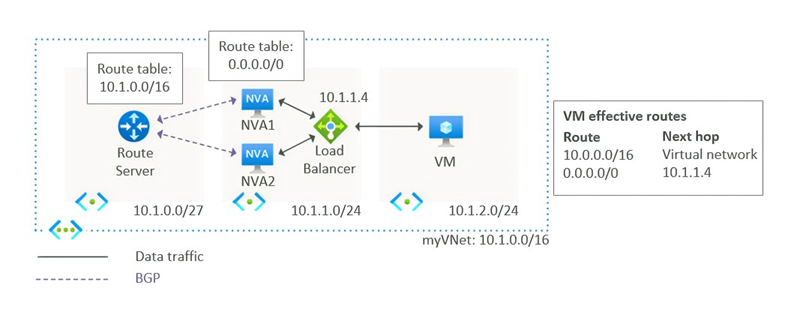
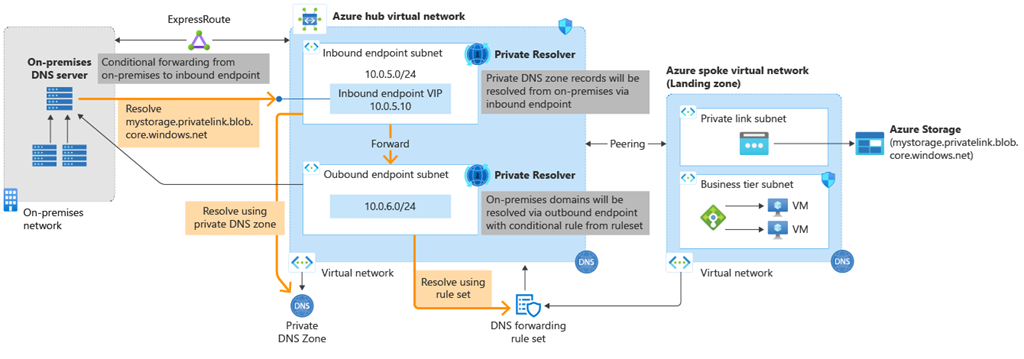
A successful hybrid networking strategy demands DNS services that work seamlessly across on-premises and cloud networks. Azure DNS Private Resolver now provides a fully managed recursive resolution and conditional forwarding service for Azure virtual networks. Using this service, you will be able to resolve DNS names hosted in Azure DNS private zones from on-premises networks as well as DNS queries originating from Azure virtual networks that can be forwarded to a specified destination server to resolve them.
This service will provide a highly available and resilient DNS infrastructure on Azure for a fraction of the price of running traditional IaaS VMs running DNS servers in virtual networks. You will be able to seamlessly integrate with Private DNS Zones and unlock key scenarios with minimal operational overhead.
We are excited to share that Azure DNS Private Resolver is now in general availability.
A quick overview of Azure DNS
We offer two types of Azure DNS Zones—private and public—for hosting your private DNS and public DNS records. In the preceding illustration, multi-region workloads running on Azure with Azure DNS Private Resolver are provisioned in two regional, centralized virtual networks with one or more spokes peered to each centralized virtual network. These virtual networks have inbound and outbound endpoints provisioned. From on-premises, there are two distinct locations (East and West) and each location connects via Express Route to the centralized virtual network where Private Resolver is provisioned. These on-premises locations have one or more local DNS servers configured to do conditional forwarding to the inbound endpoint of Private Resolver. The local DNS servers in East have the IP address of the East inbound endpoint as the primary DNS target, and the West inbound endpoint as secondary. Alternatively, the local DNS servers in West have the IP address of the West inbound endpoint as the primary DNS target, and the East inbound endpoint as secondary. There is a single private DNS zone linked to both regions and both on-premises locations can resolve names from this zone even in the event of a regional failure.
- Azure Private DNS: Azure Private DNS provides a reliable and secure DNS service for your virtual network. Azure Private DNS manages and resolves domain names in the virtual network without the need to configure a custom DNS solution. By using private DNS zones, you can use your own custom domain name instead of the Azure-provided names during deployment.
- Azure Public DNS: DNS domains in Azure DNS are hosted on Azure's global network of DNS name servers. Azure DNS uses anycast networking. Each DNS query is answered by the closest available DNS server to provide fast performance and high availability for your domain.
Source: Announcing Azure DNS Private Resolver general availability
It's common to use pipelines to build and deploy images on Azure Kubernetes Service (AKS) clusters. This process often doesn't account for the stale images left behind and can lead to image bloat on cluster nodes. These images can present security issues as they may contain vulnerabilities.
With image cleaner, we can detect and automatically remove all unused and vulnerable images cached on AKS nodes keeping the nodes cleaner and safer.
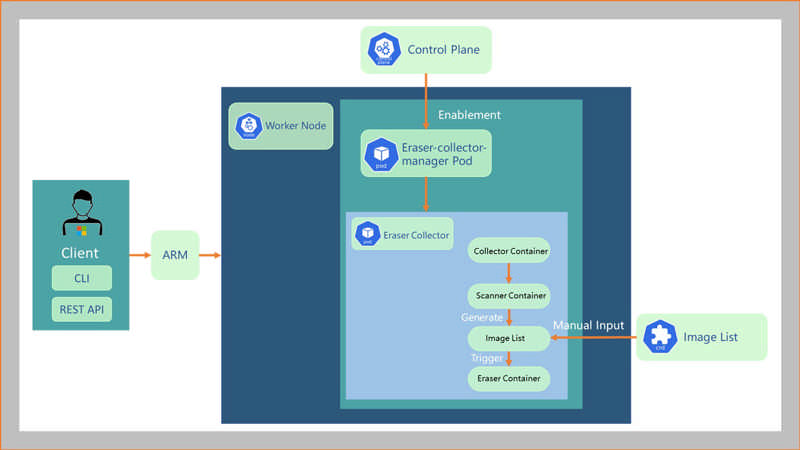
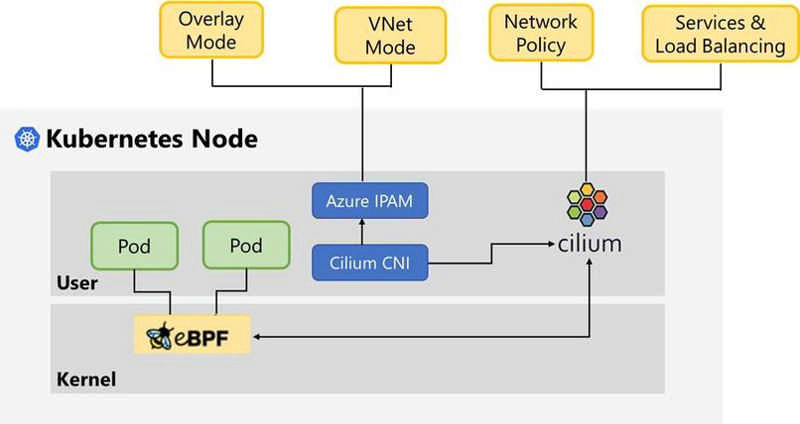
Public preview: Azure CNI Powered by Cilium
Azure CNI powered by Cilium provides native support for the next-generation Cilium eBPF data plane in AKS clusters running Azure CNI. It offers Pod networking, basic Kubernetes Network Policies, and high-performance service load balancing. The eBPF data plane is available in both VNet mode and Overlay mode of Azure CNI.
Mariner is an open-source Linux distribution created by Microsoft and is now available for preview as a container host on Azure Kubernetes Service (AKS).
Optimized for AKS, the Mariner container host provides reliability and consistency from cloud to edge across the AKS, AKS-HCI, and Arc products. You can deploy Mariner node pools in a new cluster, add Mariner node pools to your existing Ubuntu clusters, or migrate your Ubuntu nodes to Mariner nodes. To learn more about Mariner, see the Mariner documentation.
Why use Mariner
The Mariner container host on AKS uses a native AKS image that provides one place to do all Linux development. Every package is built from source and is validated, ensuring your services run on proven components. Mariner is lightweight, only including the necessary set of packages needed to run container workloads. It provides a reduced attack surface and eliminates patching and maintenance of unnecessary packages. At Mariner's base layer, it has a Microsoft hardened kernel tuned for Azure.
The ability to bring your own public IP ranges is now available in all US Government regions.
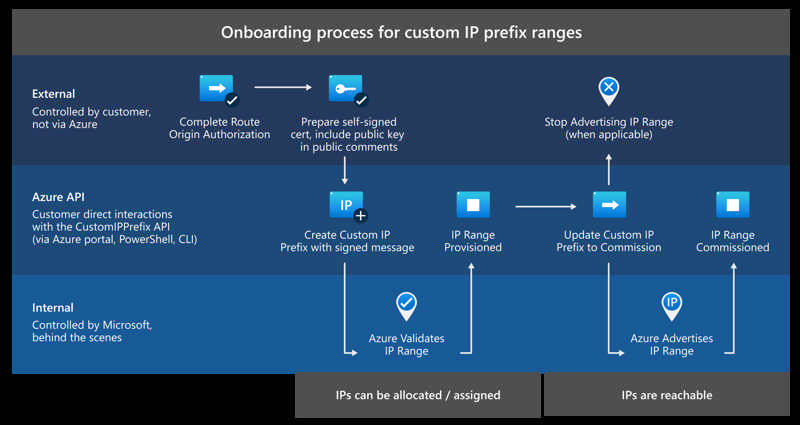
Additionally:
- You can now bring your own IPv6 ranges to Azure. These ranges must be a /48 size and can be split into multiple regional /64 ranges, of which a subset of IPs can be used as Public IP Prefixes.
- A regional commissioning feature now allows you to advertise a range internally within an Azure region prior to full global advertisement to the Internet, easing the migration process for a range that is already live outside of Azure.
Source: Generally available: Custom IP Prefixes (BYOIP) now available in US Government regions
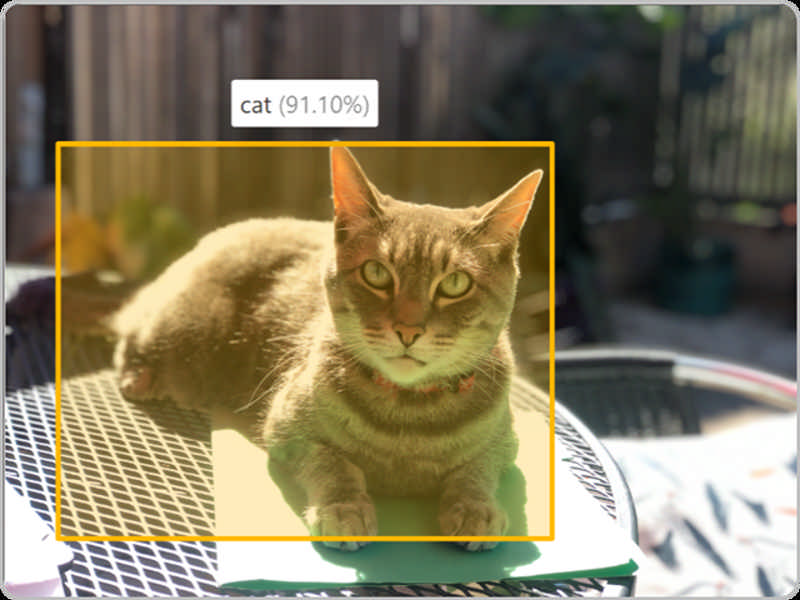
Enterprises and hobbyists alike have been using Azure Computer Vision’s Image Analysis API to garner various insights from their images. These insights help power scenarios such as digital asset management, search engine optimization (SEO), image content moderation, and alt text for accessibility among others.
Newly improved features including read (OCR)
We are thrilled to announce the preview release of Computer Vision Image Analysis 4.0 which combines existing and new visual features such as read optical character recognition (OCR), captioning, image classification and tagging, object detection, people detection, and smart cropping into one API. One call is all it takes to run all these features on an image.
The OCR feature integrates more deeply with the Computer Vision service and includes performance improvements that are optimized for image scenarios that make OCR easy to use for user interfaces and near real-time experiences. Read now supports 164 languages including Cyrillic, Arabic, and Hindi.
Tested at scale and ready for deployment
Microsoft’s own products from PowerPoint, Designer, Word, Outlook, Edge, and LinkedIn are using Vision APIs to power design suggestions, alt text for accessibility, SEO, document processing, and content moderation.
You can get started with the preview by trying out the visual features with your images on Vision Studio. Upgrading from a previous version of the Computer Vision Image Analysis API to V4.0 is simple with these instructions.
We will continue to release breakthrough vision AI through this new API over the coming months, including capabilities powered by the Florence foundation model featured in this year’s premiere computer vision conference keynote at CVPR.
Additional Computer Vision services
Spatial Analysis is also in preview. You can use the spatial analysis feature to create apps that can count people in a room, understand dwell times in front of a retail display, and determine wait times in lines. Build solutions that enable occupancy management and social distancing, optimize in-store and office layouts, and accelerate the checkout process. By processing video streams from physical spaces, you're able to learn how people use them and maximize the space's value to your organization.
The Azure Face service provides AI algorithms that detect, recognize, and analyze human faces in images. Facial recognition software is important in many different scenarios, such as identity verification, touchless access control, and face blurring for privacy. Face service access is limited based on eligibility and usage criteria in order to support our Responsible AI principles. Face service is only available to Microsoft managed customers and partners. Use the Face Recognition intake form to apply for access. For more information, see the Face limited access page.
Computer Vision and Responsible AI
We are excited to see how our customers use Computer Vision’s Image Analysis API with these new and updated features. Our technology advancements are also guided by Microsoft’s Responsible AI process, and our principles of fairness, inclusiveness, reliability and safety, transparency, privacy and security, and accountability. We put these ethical standards into practice through the Office of Responsible AI (ORA)—which sets our rules and governance processes, the AI Ethics and Effects in Engineering and Research (Aether) Committee—which advises our leadership on the challenges and opportunities presented by AI innovations, and Responsible AI Strategy in Engineering (RAISE)—a team that enables the implementation of Microsoft Responsible AI rules across engineering groups.
Get started
Start improving how you analyze images with Image Analysis 4.0 with a unified API endpoint and a new OCR Model.
- Computer Vision documentation.
- Image Analysis documentation.
- Quick Start for Image Analysis.
- Vision Studio for demoing product solutions.
Source: Image Analysis 4.0 with new API endpoint and OCR model in preview
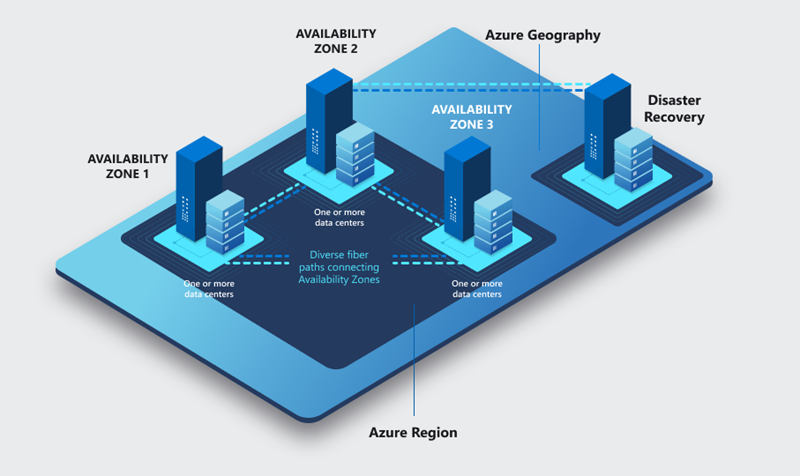
Azure regions and availability zones (AZ) are designed to help you achieve resiliency and reliability for your business-critical workloads.This Azure NetApp Files availability zone volume placement feature lets you deploy new volumes in the logical availability zone of your choice to support enterprise, mission-critical high availability (HA) deployments across multiple availability zones.This public preview of the feature is available in all availability zone-enabled regions with Azure NetApp Files presence.
Source: Public preview: Availability zone volume placement for Azure NetApp Files
Azure Data Explorer now supports the ingestion of data from many receivers via the OpenTelemetry exporter.
OpenTelemetry (OTel) is a vendor-neutral open-source observability framework for instrumenting, generating, collecting, and exporting telemetry data such as traces, metrics, logs.
We are releasing Azure Data Explorer OpenTelemetry exporter, which supports ingestion of data from many receivers into Azure Data Explorer, allowing you to instrument, generate, collect, and store data using a vendor-neutral open-source framework.
Source: General availability: OpenTelemetry exporter for Azure Data Explorer
SSH File Transfer Protocol (SFTP) support for Azure Blob Storage is now generally available.
Azure Blob Storage now supports SFTP, enabling you to leverage object storage economics and features for your SFTP workloads. With just one click, you can provision a fully managed, highly scalable SFTP endpoint for your storage account. This expands Blob Storage’s multi-protocol access capabilities and eliminates data silos – meaning you can run different applications, requiring different protocols, on a single storage platform with no code changes.
Source: Generally available: SFTP support for Azure Blob Storage
The option to store the backup of the workloads protected by Azure Backup in zone redundant vaults is generally available. When you configure the protection of a resource with the zone-redundant storage (ZRS) vault, the backups replicate synchronously across three availability zones in a region. It enables you to perform successful restores and recover your data even if a zone goes down. For organizations governed by the compliance requirement of data not crossing the regional boundary, zone-redundant storage is the right and preferred choice for backups.
With the general availability of this feature, you have a broader set of redundancy or storage replication options to choose from for your backup data. Based on your data residency, data resiliency, and total cost of ownership (TCO) requirements, you can select either locally redundant storage (LRS), zone-redundant storage (ZRS), or geo-redundant storage (GRS).
Azure Backup currently supports ZRS in these regions.
Source: General availability: Zone-redundant storage support by Azure Backup
Azure Kubernetes Service is increasing the maximum node limit per cluster from 1,000 nodes to 5,000 nodes for customers using the uptime-SLA feature. The default limit for all AKS clusters will continue to be 1,000 nodes. However, AKS clusters using the uptime SLA feature can now request an increase in the AKS service quota up to a maximum of 5,000 nodes across all node pools in a cluster by creating a support request.
Workloads that need large amount of compute resources can now scale beyond 1,000 virtual machines (nodes) within the same cluster removing the operational overhead of managing cross-cluster deployments and workloads. You can scale your clusters up to 5,000 nodes using both manual and cluster autoscaler.
This feature is available for clusters using uptime-SLA and Azure CNI Network plugin only.
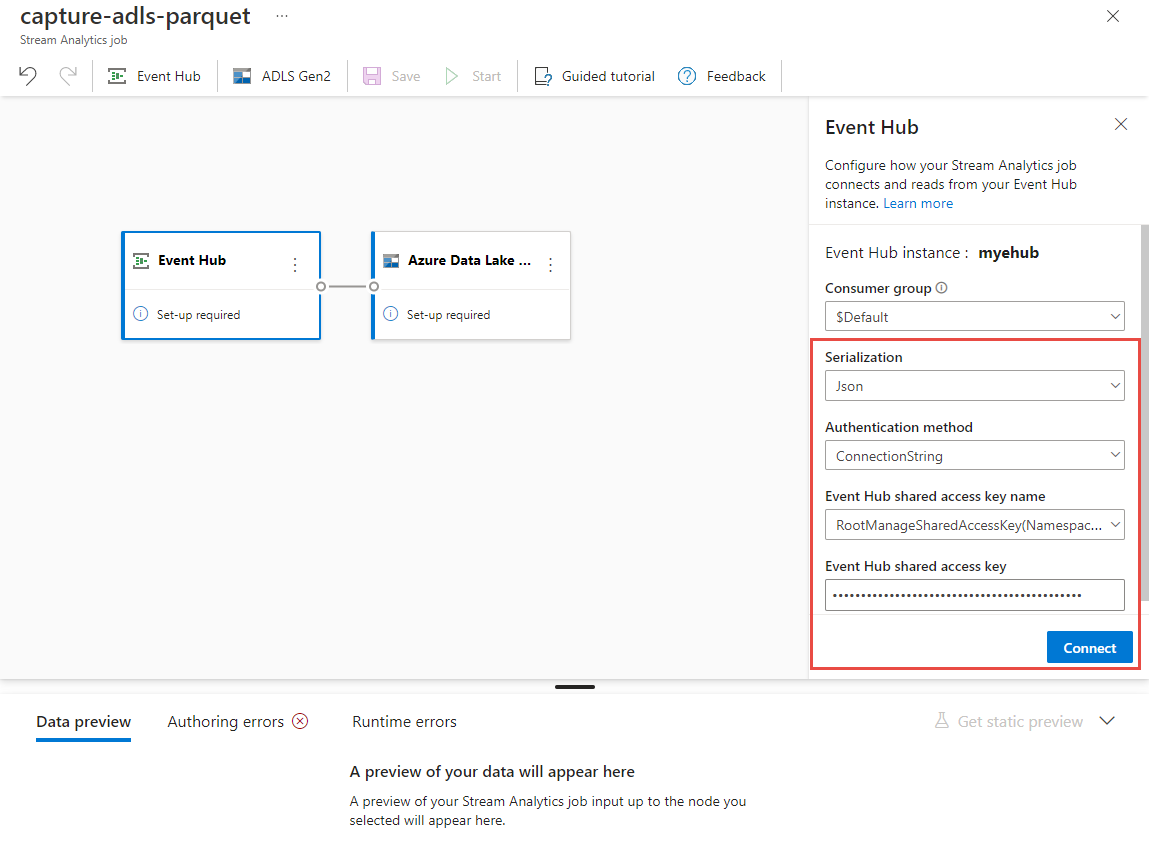
Stream Analytics now supports end-to-end exactly once semantics when writing to Azure Data Lake Storage Gen2. Your jobs now guarantee no data loss and no duplicates being produced as output. This simplifies your streaming pipeline by not having to monitor, implement, and troubleshoot deduplication logic.
Source: Public preview: Exactly once delivery for Azure Data Lake Storage Gen2
Azure savings plan for compute is an easy and flexible way to save significantly on compute services, compared to pay-as-you-go prices. The savings plan unlocks lower prices on select compute services when customers commit to spend a fixed hourly amount for one or three years. Choose whether to pay all upfront or monthly at no extra cost. As you use select compute services across the world, your usage is covered by the plan at reduced prices, helping you get more value from your cloud budget. During the times when your usage is above your hourly commitment, you'll be billed at your regular pay-as-you-go prices. With savings automatically applying across compute usage globally, you'll continue saving even as your usage needs change over time.
Source: General availability: Azure savings plan for compute
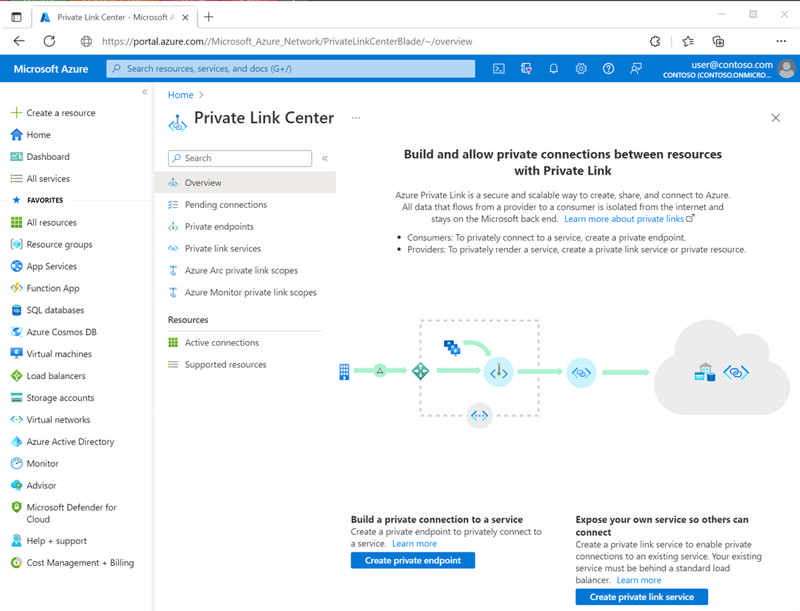
Private endpoint support for statically defined IP addresses is generally available. This feature allows you to add customizations to your deployments. Leverage already reserved IP addresses and allocate them to your private endpoint without relying on the randomness of Azure's dynamic IP allocation. In doing so, you can account for a consistent IP address to the private endpoint to use alongside IP based security rules and scripts.
Source: General availability: Static IP configurations of private endpoints
Thanks to your support during the preview of the completely revamped Service Bus Explorer tool on the Azure portal, this tool is now generally available. Azure Service Bus has two types of operations which can be performed against it:
- Management operations: Create, update, delete of Service Bus namespace, queues, topics, and subscriptions.
- Data operations: Send to and receive messages from queues, topics, and subscriptions.
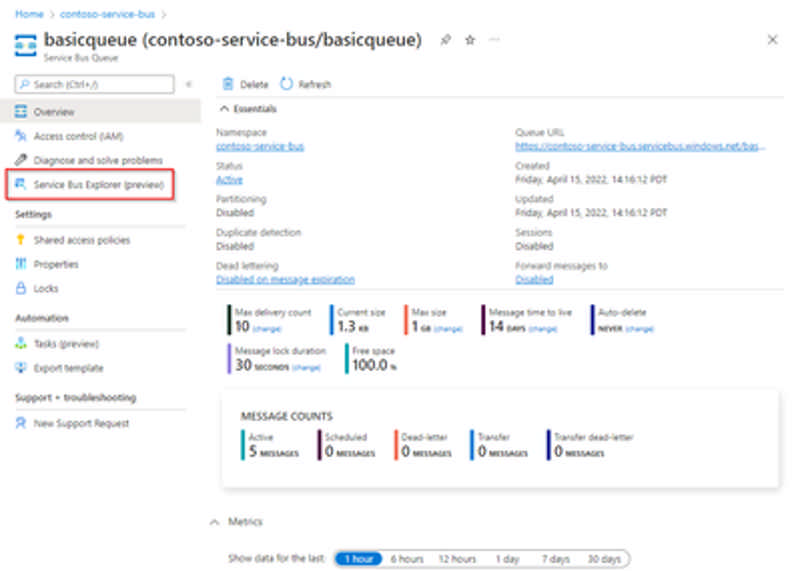
While we have offered a portal-based Service Bus Explorer for data operations for a while now, you have provided us with feedback that the experience was still lacking compared to the community managed Service Bus Explorer OSS tool.
We have released a new version of Service Bus Explorer, which brings many new capabilities to the portal for working with your messages, right from the portal. For example, it is now possible to send, receive, and peek messages on queues, topics, and subscriptions, including dead-letter sub-queues. The tool allows you to perform operations such as complete, re-sending, and deferral. This can be done on a single message or for multiple messages at once.
To access the tool:
- Navigate to the namespace.
- Select the specific queue or topic that you want to perform your data operations on.
- Open "Service Bus Explorer (preview)" from the left menu navigation pane. When working with a topic, it's also possible to select a specific subscription within.
For all information about the tool and step-by-step guidance for the different operations, check the documentation.
Source: Generally available: Service Bus Explorer for the Azure portal
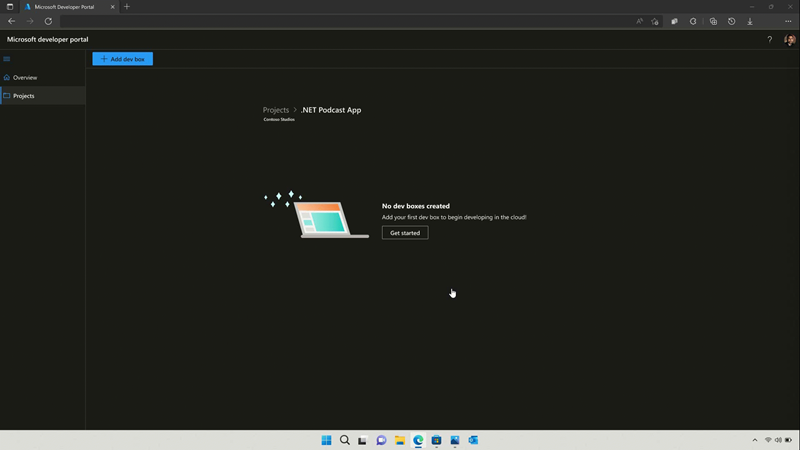
Azure Deployment Environments has entered public preview.
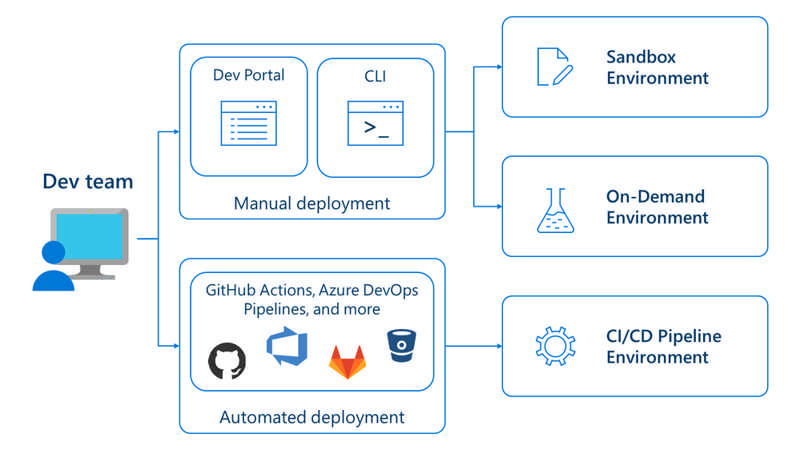
Azure Deployment Environments help dev teams create and manage all types of environments throughout the application lifecycle with features like:
On-demand environments enable developer to spin up environments with each feature branch to enable higher quality code reviews and ensure devs can view and test their changes in a prod-like environment.
Sandbox environments can be used as greenfield environments for experimentation and research.
CI/CD pipeline environments integrate with your CI/CD deployment pipeline to automatically create dev, test (regression, load, integration), staging, and production environments at specified points in the development lifecycle.
Environment types enable dev infra and IT teams to create preconfigured mappings that automatically apply the right subscriptions, permissions, and identities to environments deployed by developers based on their current stage of development.
Template catalogues housed in a code repo that can be accessed and edited by developers and IT admins to propagate best practices while maintaining security and governance.
For more information about Azure Deployment Environments, visit the announcement blog.
Source: Public preview: Microsoft Azure Deployment Environments
We’re announcing the general availability of the intent feature in Azure proximity placement groups. Proximity placement groups are a popular logical construct among customers running very latency sensitive workloads such as SAP and HPC. Proximity placement groups are used to physically locate Azure compute resources close to each other to provide best possible latencies.
With the addition of the new optional parameter, intent, you can now specify the VM sizes intended to be part of a proximity placement group when it is created. An optional zone parameter can be used to specify where you want to create the proximity placement group. This capability allows the proximity placement group allocation scope (datacenter) to be optimally defined for the intended VM sizes, reducing deployment failures of compute resources due to capacity unavailability. The new intent feature can now be used across all regions and it is supported through CLI and PowerShell interfaces.
To learn more about the new proximity placement groups' intent feature, refer to the documentation proximity placement groups - Azure Virtual Machines | Microsoft Learn.
Source: General availability: New Azure proximity placement groups feature
Public preview: Azure Resource Topology
Azure Resource Topology (ART) allows visualizing the resources in a network, acquire system context, understand state and debug issues faster. It provides a visualized connected experience for inventory management and monitoring.
This unified topology leads to upgrading the network monitoring and management experience in Azure. Replacing the Network Watcher topology, this topology will allow the users to draw a unified and dynamic topology across multiple subscription, regions, and resource groups (RGs) comprising of multiple resources.
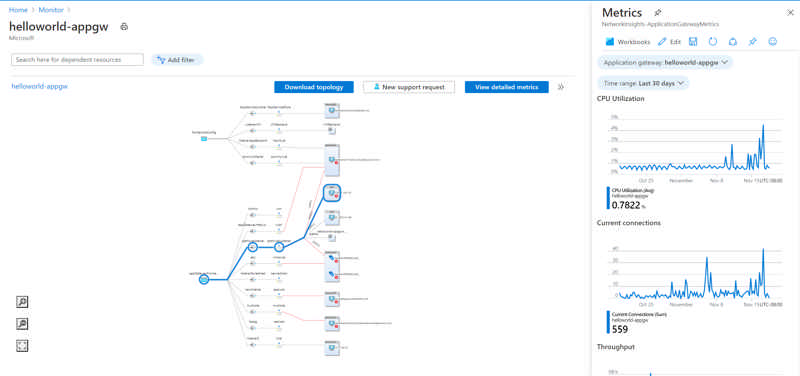
Allowing deep dive into your environment, ART provides the capability for users to drill down from regions, VNETs to subnets, and resource view diagram of resources supported in Azure. It also stitches the end-to-end monitoring and diagnostics story with the capability to run next hop directly from a VM selected in the topology after specifying the destination IP address.
Selecting a resource in the topology highlights the node and all other nodes/resources connected to it via edges. These edges define the connections among regions which can be done through VNET peering, VNET Gateways, etc. The side pane shows extensive resource details and properties for selected node/resource.
Features available in public preview:
- Multi-region and multi-subscription visualization
- Drilldown from Azure region to resources inside subnet
- Side-panel showing resource properties and metrics
- Highlighting of nodes connected to a selected resource
- Automatic grouping of resources of the same type
- Side-by-side visualization of two regions/VNETs/Subnets
- Search based on resource name
- Scope selector based on subscription and resource-type filtering
- Health status of resources using resource health (RHC) status
- Diagnostics tool next hop integration.
- Resource view diagram for all supported resources
IP Protection is designed with SMBs in mind and delivers enterprise-grade, cost-effective DDoS protection.
Instead of enabling DDoS protection on a per virtual network basis, including all public IP resources associated with resources in those virtual networks, you now have the flexibility to enable DDoS protection on an individual public IP.
The existing standard SKU of Azure DDoS Protection will now be known as Network Protection.
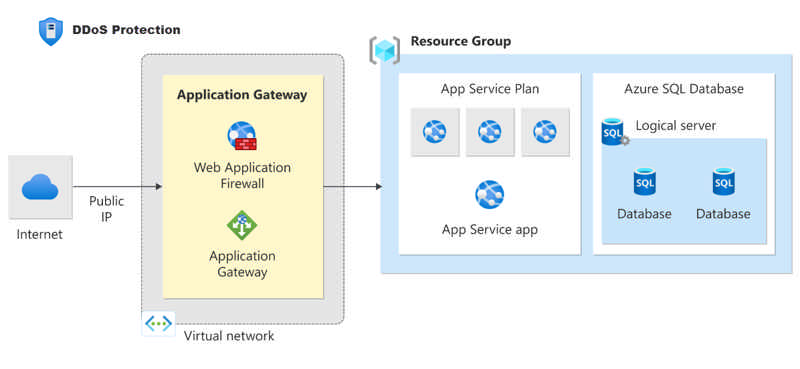
IP Protection includes the same features as Network Protection, but Network Protection will have in the following value-added services: DDoS Rapid Response support, cost protection, integration with Azure Firewall Manager, and discounts on Azure Web Application Firewall.
Billing for IP Protection will be effective starting February 1, 2023.
Source: Public preview: IP Protection SKU for Azure DDoS Protection
Classic resource providers that use Azure Service Manager (classic deployment model) will be retired on 31 August 2024.
Required action
Your access to the classic resource provider’s endpoint will be revoked and the resource provider will be disabled on 31 August 2024.
-
To take advantage of advanced capabilities offered by Azure Resource Manager and avoid service disruptions, migrate your resources that use Classic (ASM) to Azure Resource Manager by 31 August 2024.
-
Additionally, to manage service expectations of your classic resource provider, notify your end customers and coordinate with them for completing migration before the retirement date of 31 August 2024.
Source: Azure classic resource providers will be retired on 31 August 2024
Azure Daily 2022 - Oct 10, 2022
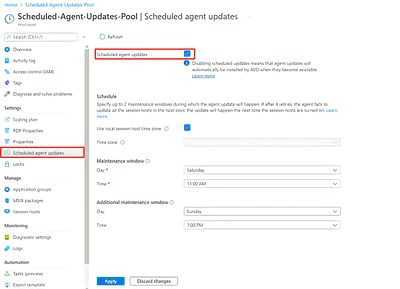
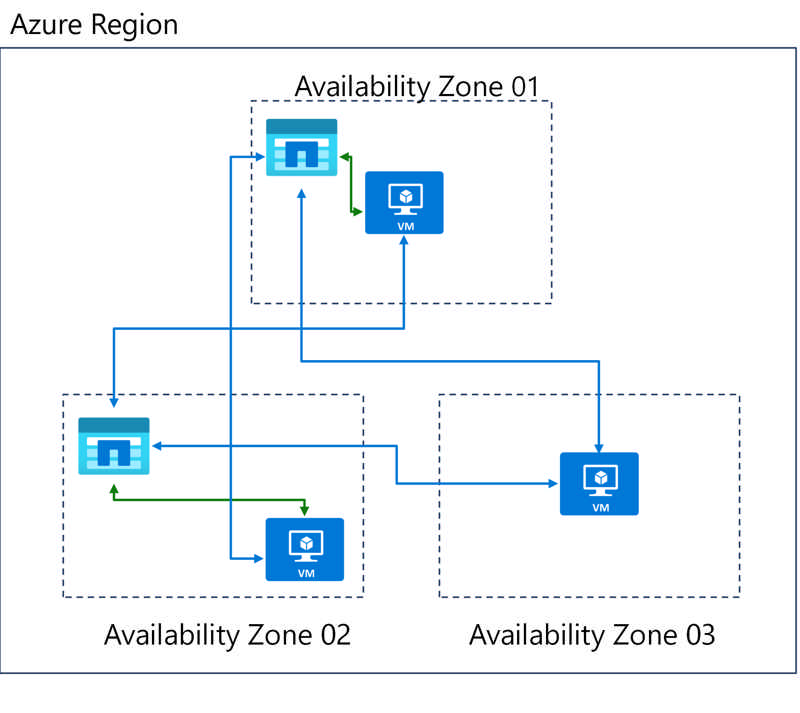
Microsoft is pleased to announce that you can now automatically distribute your session hosts across any number of availability zones. This enables you to take full advantage of the built-in Azure resiliency options from within the same deployment process.
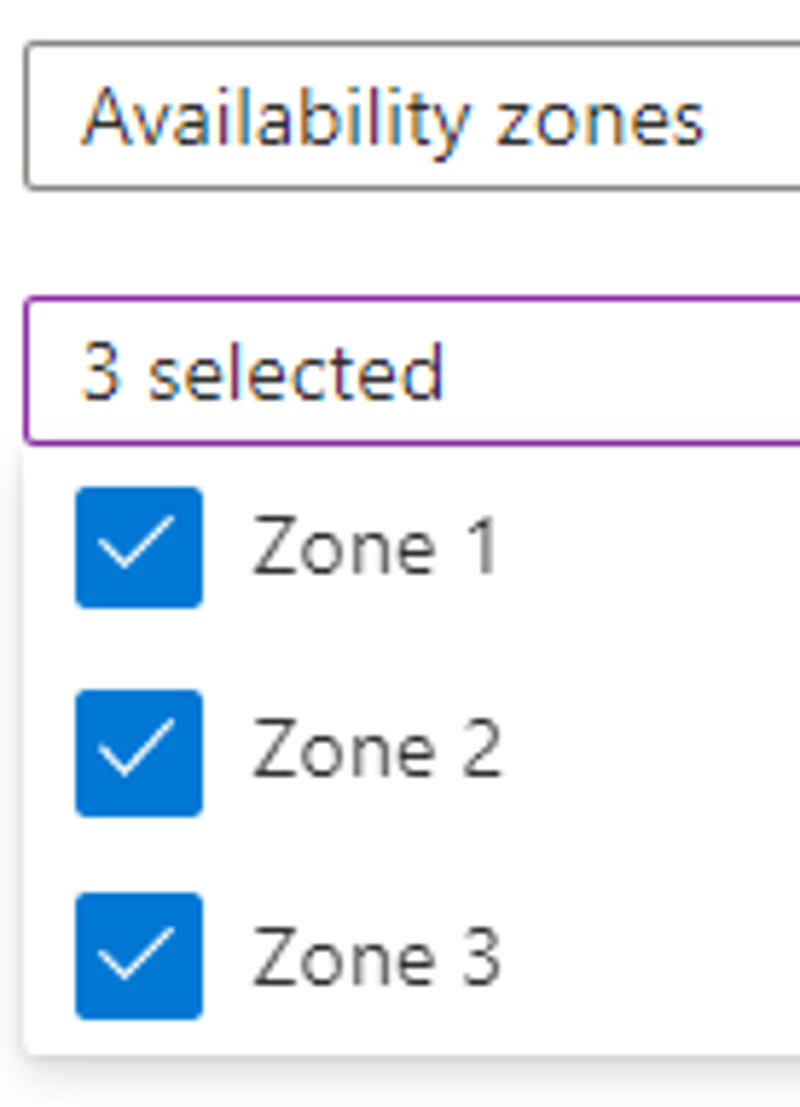
This has been a feature request from many of our customers, and I'm pleased to announce the host pool deployment process has been improved so it now supports deploying into up to three availability zones in Azure regions that support them.
Read more at Azure Daily 2022
Today Microsoft officially announced the general availability of a simpler, more reliable, and modernized way to protect your VMware virtual machines using Azure Site Recovery, for recovering quickly from disasters. We are now offering these enhancements:
- Stateless ASR replication appliance
- Automatic upgrades for ASR replication appliance and mobility agent
- Easier scale management
- High availability for appliances
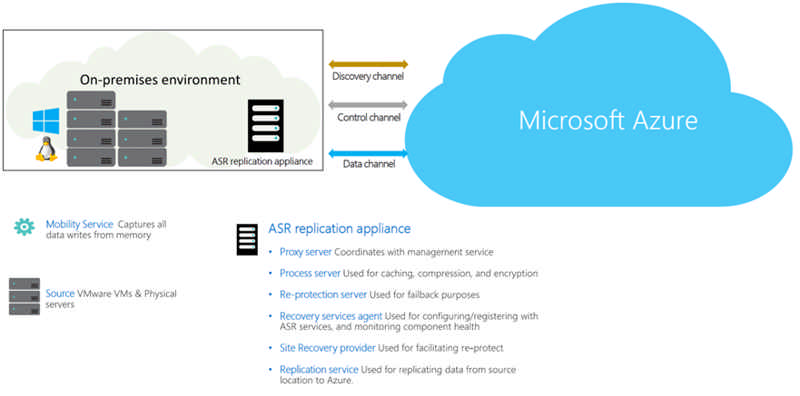
Learn more about the modernized architecture and move to the modernized experience now.
Source: General availability: Simplified disaster recovery for VMware machines using Azure Site Recovery
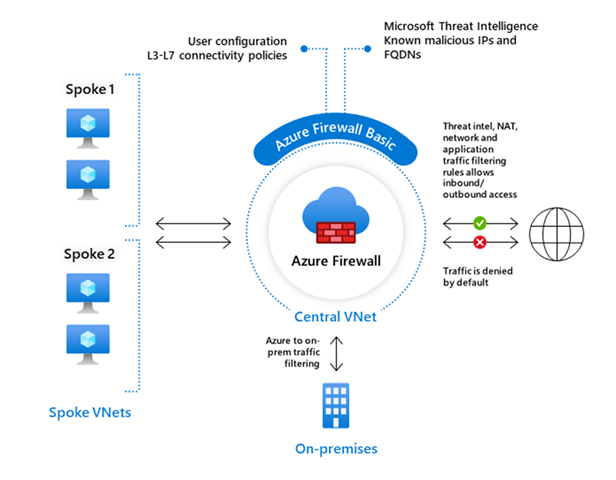
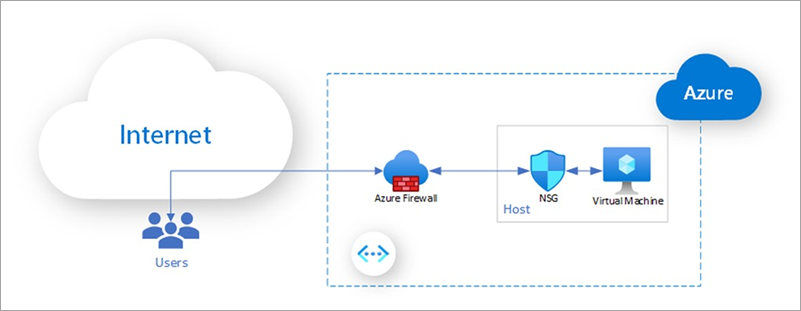
Azure Firewall Basic is a new SKU for Azure Firewall designed for small and medium-sized businesses.
The main benefits are:
Comprehensive, cloud-native network firewall security:
- Network and application traffic filtering
- Threat intelligence to alert on malicious traffic
- Built-in high availability
- Seamless integration with other Azure security services
Simple setup and easy-to-use:
- Setup in just a few minutes
- Automate deployment (deploy as code)
- Zero maintenance with automatic updates
- Central management via Azure Firewall Manager
Cost-effective:
- Designed to deliver essential, cost-effective protection of your resources within your virtual network
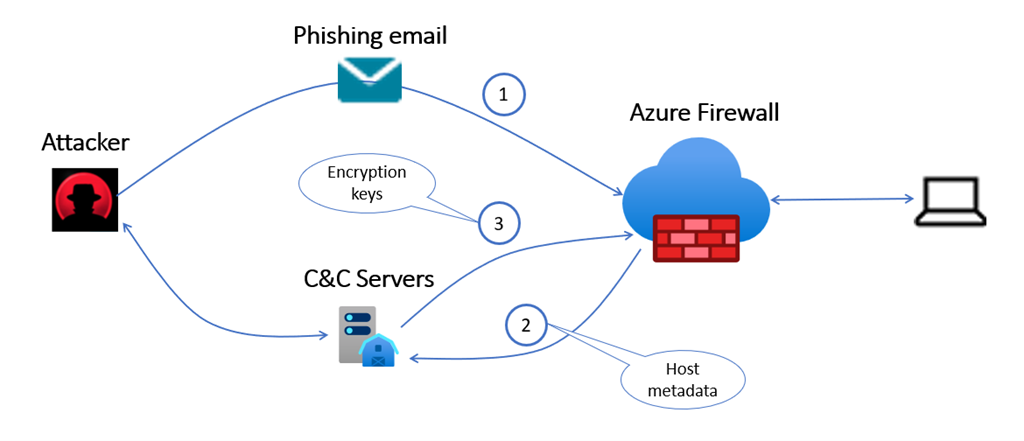
Policy analytics for Azure Firewall, now in public preview, provides enhanced visibility into traffic flowing through Azure Firewall, enabling the optimization of your firewall configuration without impacting your application performance.
As application migration to the cloud accelerates, it’s common to update Azure Firewall configuration daily (sometimes hourly) to meet the growing application needs and respond to a changing threat landscape. Frequently, changes are managed by multiple administrators spread across geographies.
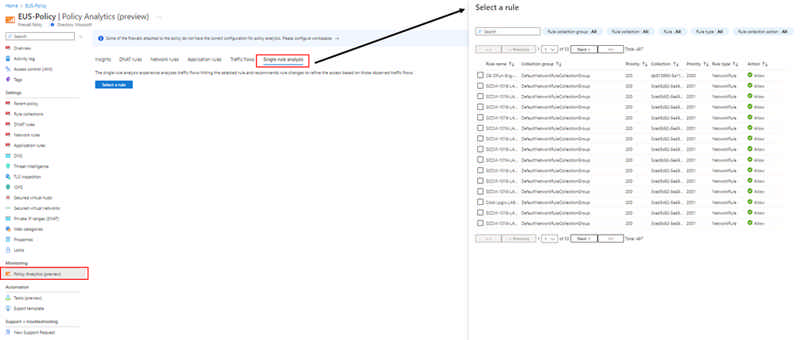
Over time, the firewall configuration can grow sub optimally impacting firewall performance and security. It’s a challenging task for any IT team to optimize firewall rules without impacting applications and causing serious downtime. Policy analytics help address these challenges faced by IT teams by providing visibility into traffic flowing through the firewall with features such as firewall flow logs, rule to flow match, rule hit rate, and single rule analysis. IT admins can refine Azure Firewall rules in a few simple steps through the Azure portal.
Read the blog and Azure Firewall documentation to learn more.
Follow these instructions to enable policy analytics on your subscriptions.
In Azure App Service, you can easily create on-demand custom backups and automatic backups. You can easily restore these backups by overwriting an existing app or by restoring it to a new app or slot.
Automatic backup and restore is now in preview for isolated pricing tier for App Service Environment V2 and V3.
For more information about Azure App Services backups and restore, visit: Back up an app - Azure App Service | Microsoft Docs
Source: Public preview: Automatic backup for App Service Environment V2 and V3
Generally available: Azure Functions .NET Framework support in the isolated worker model
You can now build production Serverless Apps with Azure Functions v4 in isolated worker model with .NET Framework 4.8. This allows apps with .NET Framework dependencies to explore taking advantage of the latest versions of Azure Functions host.
If you are on .NET Framework on v1, it is recommended to migrate to .NET 6 or .NET 7 on v4 host. If your apps have .NET Framework dependencies, please migrate to .NET framework on v4 and provide feedback on our Azure Functions .NET Worker GitHub repository.
Apps built using this capability will follow the same patterns as any isolated .NET worker project in Functions, but they will specify .NET Framework 4.8 as the target framework. Please provide feedback through the Azure Functions .NET Worker GitHub repository.
Source: Generally available: Azure Functions .NET Framework support in the isolated worker model
Today we’re announcing the public preview for enabling an Azure AD-based single sign-on experience and support for passwordless authentication, using Windows Hello and security devices (like FIDO2 keys). With this preview, you can now:
- Enable a single sign-on experience to Azure AD-joined and Hybrid Azure AD-joined session hosts when using the Windows and the web clients
- Use passwordless authentication to sign in to the host using Azure AD
- Use passwordless authentication inside the session when using the Windows client
- Use third-party Identity Providers (IdP) that integrate with Azure AD to sign in to the host
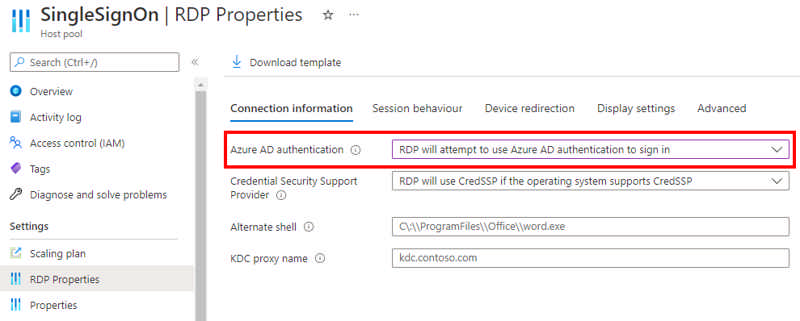
Read more at Azure Daily 2022
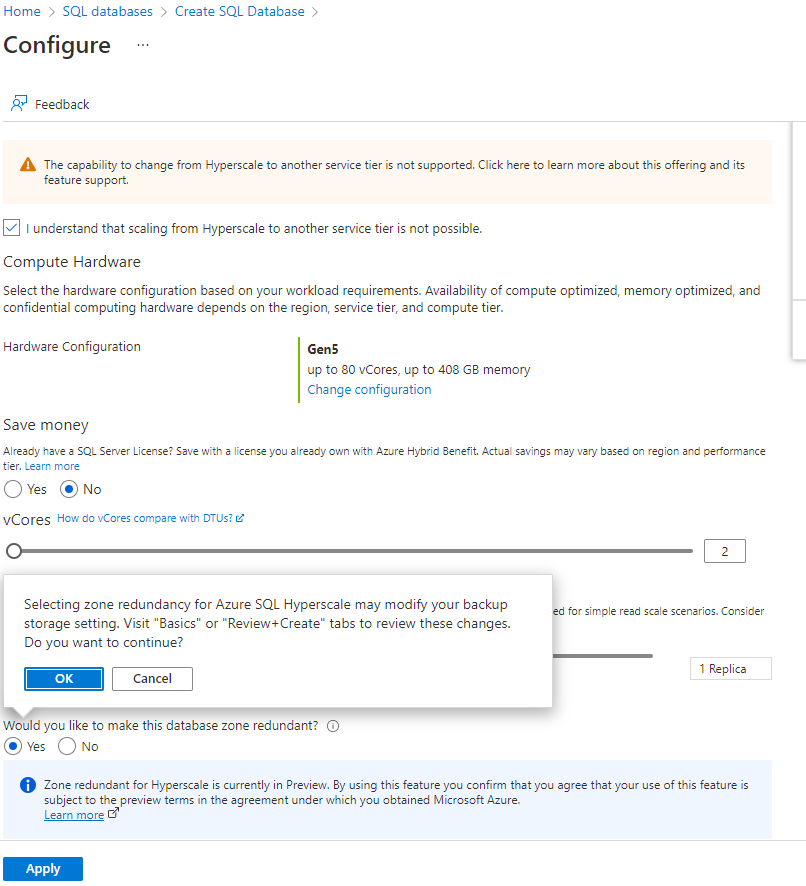
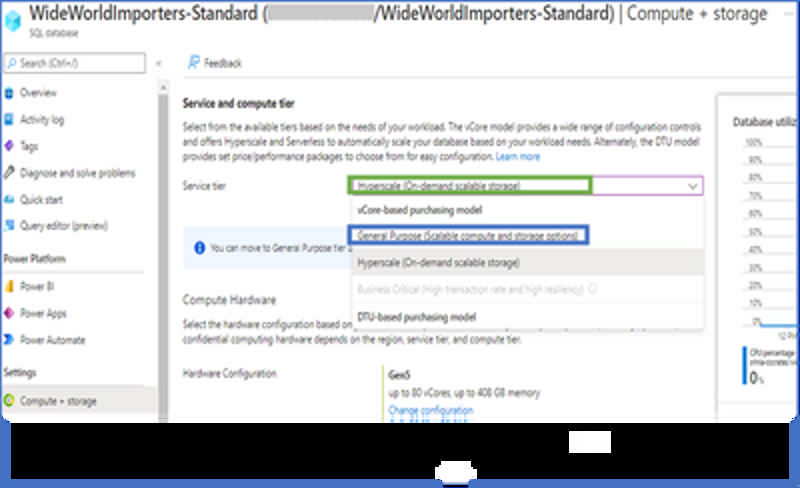
We are happy to announce General Availability(GA) of the ability to reverse migrate an Azure SQL Database from Hyperscale tier to General Purpose tier. Previously, migration into the Hyperscale tier was a one-way migration with no easy way to move back to any non-Hyperscale tier. Reverse Migration to the General Purpose service tier now allows customers who have recently migrated an existing Azure SQL DB database to the Hyperscale service tier to move back, should Hyperscale not meet their needs. This provides additional mobility for their SQL Database data. Once in the General Purpose tier, they have the flexibility to remain on that tier or move their database to other SQL Database tiers including coming back to Hyperscale tier.
Read more at Azure Daily 2022
Public preview: Customer initiated storage account conversion
Today Azure Storage is announcing the public preview of a self-service option to convert storage accounts from non-zonal redundancy (LRS/GRS) to zonal redundancy (ZRS/GZRS). This allows you to initiate the conversion of storage accounts via the Azure portal without the necessity of creating a support ticket.
Source: Public preview: Customer initiated storage account conversion
Encryption scopes introduce the option to provision multiple encryption keys in a storage account with hierarchical namespace. Using encryption scopes, you now can provision multiple encryption keys and choose to apply the encryption scope either at the container level (as the default scope for blobs in that container) or at the blob level. The preview is available for REST, HDFS, NFSv3, and SFTP protocols in an Azure Blob / Data Lake Gen2 storage account.
The key that protects an encryption scope may be either a Microsoft-managed key or a customer-managed key in Azure Key Vault. You can choose to enable automatic rotation of a customer-managed key that protects an encryption scope. When you generate a new version of the key in your Key Vault, Azure Storage will automatically update the version of the key that is protecting the encryption scope, within a day.
Source: Public preview: Encryption scopes on hierarchical namespace enabled storage accounts
Immutable storage for Azure Data Lake Storage is now generally available. Immutable storage provides the capability to store data in a write once, read many (WORM) state. Once data is written, the data becomes non-erasable and non-modifiable and you can set a retention period so that files can't be deleted until after that period has elapsed. Additionally, legal holds can be placed on data to make that data non-erasable and non-modifiable until the hold is removed.
This release includes the new “allow append writes for block and append blobs” flag, which allows users to set up immutable policies for block and append blobs to keep already written data in a WORM state and continue to add new data.
If you are using NFS 3.0 protocol or SFTP support on an account, immutable storage is not supported.
Source: Generally available: Immutable storage for Azure Data Lake Storage
Immutable storage for Blob Storage on containers (which has been generally available since September 2018) now includes a new append capability. This capability, titled “Allow Protected Appends for Block and Append Blobs,” allows you to set up immutable policies for block and append blobs to keep already written data in a WORM state and continue to add new data. This capability is available for both legal holds and time-based retention policies.
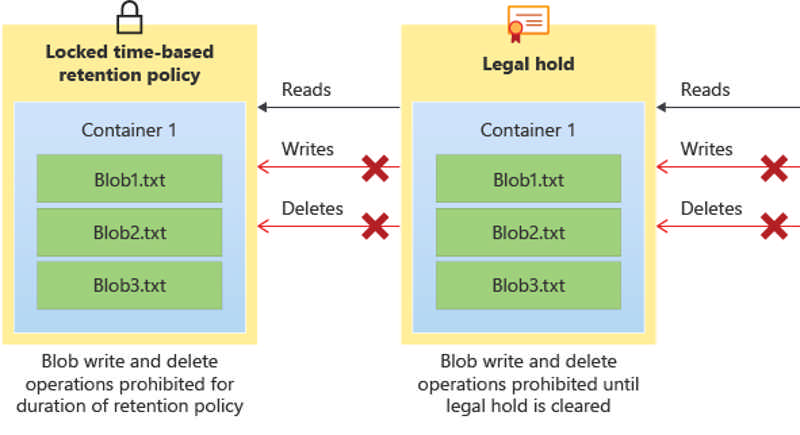
This capability is supported in all public regions and it is available to new and existing accounts. To learn more, read the documentation on immutable storage.
Source: General availability (update): Improved Append Capability on Immutable Storage for Blob Storage
Azure Database for PostgreSQL – Flexible Server performs automatic snapshot backups and allows you to restore to any point in time within the retention period. The overall time to restore and recover may take several minutes depending on the amount of recovery to perform from the previous backup.
In use cases like testing, development, and data verifications at backup that don’t require the latest data but need to spin up a server quickly, Azure Database for PostgreSQL – Flexible Server now supports the fastest restore feature to address these use cases. This feature lists all the available automatic backups and you can choose a specific backup to restore. This feature then provisions a new server and restores the backup from the snapshot. Since no recovery is involved, this feature provides a fast and predictable restore experience.
Source: Generally available: Fast restore for Azure Database for PostgreSQL – Flexible Server
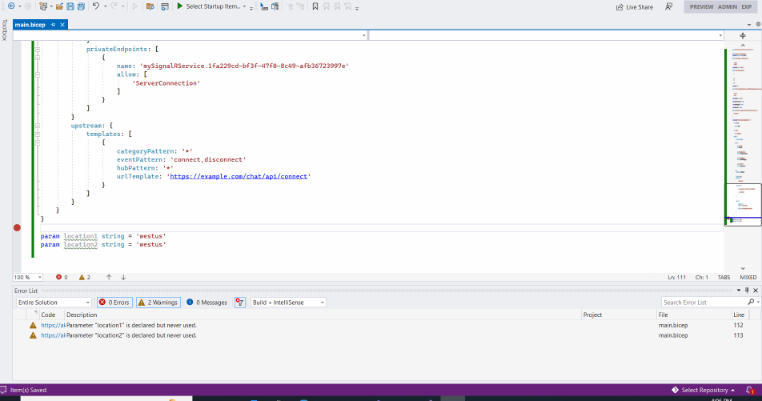
In less than two years, Bicep’s VS Code extension has grown from zero users to more than 15 thousand a month. In addition to the Bicep extension’s success, millions of resources are now deployed with Bicep files via Azure CLI and Azure PowerShell. Our incredible community has not only shaped the suite of Bicep features we know and love today, but they also made it abundantly clear how important Visual Studio was to their daily workflow. We heard you, no more switching back and forth between editors!
New operators on regional WAF custom rules:
Azure regional Web Application Firewall (WAF) with Application Gateway now supports creating custom rules using the operators "Any" and "GreaterThanOrEqual". Custom rules allow you to create your own rules to customize how each request is evaluatedas it passes through the WAF engine.
To learn more about creating custom rules, please visit the regional WAF documentation.
Geo filtering using socket address on global WAF:
Azure global Web Application Firewall (WAF) with Azure Front Door now supports custom geo-match filtering rules using socket addresses. Filtering by socket address allows you to restrict access to your web application by country/region using the source IP that the WAF sees. If your user is behind a proxy, socket address is often the proxy server address.
To learn more about geo filtering, please visit the global WAF documentation..
Source: General availability: Improvements to Azure Web Application Firewall (WAF) custom rules
Azure Media Services is announcing the general availability of low-latency live streaming (LL-HLS). This offers glass-to-glass latency as low as 4 seconds with any player capable of supporting Apple's low-latency HLS (LL-HLS) specification. With low-latency in the 4-7 second range, you can build a variety of interactive applications that allow you to engage seamlessly with your audiences at scale.
What kinds of applications can you build with low-latency live streaming?
Low-latency support can enable you to stream a variety of interactive scenarios including:
- Retail live shopping.
- Fitness and educational instruction classes.
- Social streaming and user generated live where audiences can chat and react with emojis.
What are the key features of low-latency live streaming in Media Services?
- Latencies in the 4-7 second range (upper end latency can vary by network conditions and geography).
- Automatic live transcription in over 50 languages.
- Dynamic encryption and digital rights management (DRM) support for PlayReady, Widevine, and FairPlay.
- Player friendly - Works natively with Apple devices (MacOS 12 and iOS15 and above) with no additional player work needed. Playback has been evaluated with the latest version of HLS.js, Video.js, Shaka, and more.
- No additional costs over existing encoding live events.
- Major improvements in latency for DASH delivery when not using LL-HLS playback (LL-DASH support is not available at this time).
Source: General availability: Azure Media Services low-latency live streaming
The new read replica feature allows you to replicate your data from an instance of Azure Database for MySQL Flexible Server to a read-only server. You can use this feature to replicate the source server to up to a total of 10 replicas. This functionality is now extended to support high availability (HA) enabled servers within the same region.
Source: General availability: Read replica for Azure Database for MySQL - Flexible Server
Restore artifacts you may have deleted by mistake using the Azure Container Registry (ACR) soft delete feature.
After the feature is enabled and an artifact is deleted, the deleted artifact is stored in a recycle bin for a number of days (user configurable setting). You can restore the artifact while it is still available in the recycle bin and build containers from it right away. Once an artifact hits the configured recycle days limit, it is purged from the Azure Container Registry permanently.
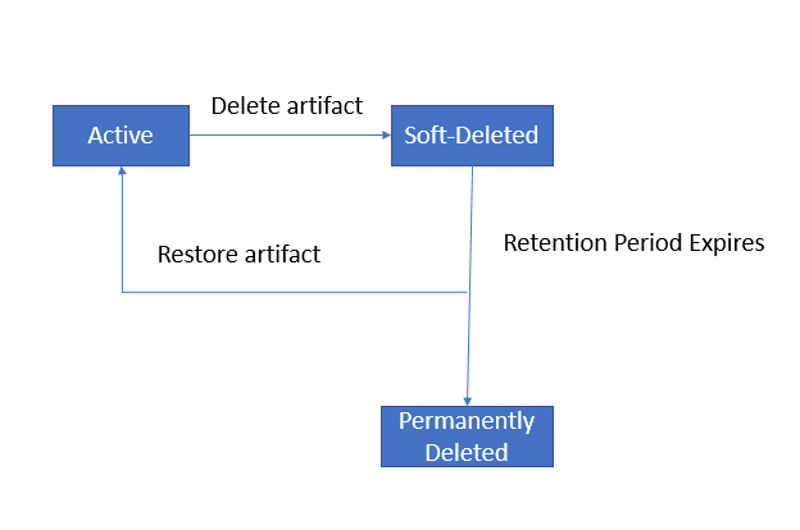
Source: Public preview: Soft delete in Azure Container Registry
Updating the address space for peered virtual networks now is now generally available. This feature allows you to update the address space or resize for a peered virtual network without removing the peering.
Users often want to resize or update the IP address of their virtual networks as they grow their footprint in Azure. Users can now resize their virtual networks to meet their needs without downtime. This feature allows you to easily resize your virtual networks without the need to remove the peering in advance.
Source: Generally available: Resizing of peered virtual networks
An Azure Kubernetes Service (AKS) cluster with API Server VNet Integration configured projects the API server endpoint directly into a delegated subnet in the VNet where AKS is deployed. This enables network communication between the API server and the cluster nodes without any required private link or tunnel. The API server will be available behind an Internal Load Balancer VIP in the delegated subnet, which the nodes will be configured to utilize.
Source: Public preview: API Server VNET Integration for AKS private cluster
Generally available: Multi-instance GPU support in AKS
Multi-instance GPU (MIG) for the A100 GPU is now generally available in AKS. Multi-instance GPU provides a mechanism for you to partition up the GPU for Kubernetes workloads on the same VM. You can now run your production workloads using the A100 GPU SKU and benefit from its higher performance.
Source: Generally available: Multi-instance GPU support in AKS
You can easily configure an Azure Database for PostgreSQL instance as output to your Stream Analytics job with zero code. This functionality is now generally available.
Source: General availability: Azure Database for PostgreSQL output in Stream Analytics
Currently, virtual machines (VMs) running on Azure Dedicated Host support the use of standard and premium disks as data disks. We are introducing support for ultra disks on dedicated host.
Ultra disks are highly performant disks on Azure that offer high throughput (maximum of 4000 MBps per disk) and high IOPS (maximum of 160,00 IOPS per disk) depending on the disk size. If you are running IaaS workloads that are data intensive and latency sensitive, such as Oracle DB, MySQL DB, other critical databases, and gaming applications, you will benefit from using ultra disks as data disks on VMs hosted on dedicated host.
Source: Generally available: Azure Dedicated Host support for Ultra Disk Storage
Save up to 24 percent on your usage of Azure Backup Storage by purchasing reserved capacity storage. The reservation discount will automatically apply to your matching Backup Storage and the process of purchasing a reservation is streamlined. Reservations are available on a one-year basis for up to a 16 percent discount or on a three-year basis for a 24 percent discount.
Source: Generally available: Reserved capacity for Azure Backup Storage
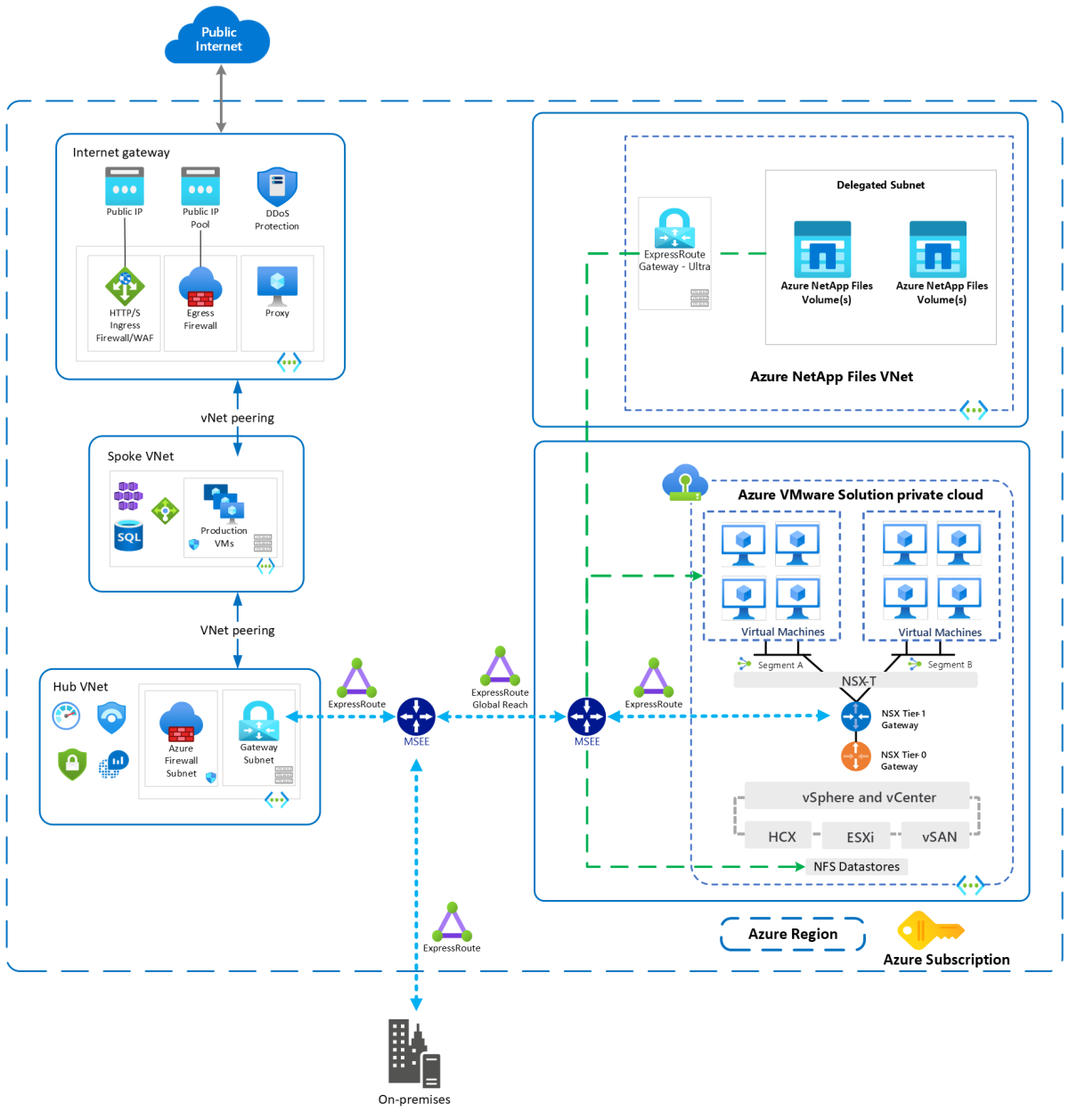
We are announcing the general availability of standard network features for Azure NetApp Files volumes. Standard network features provide you with an enhanced, and consistent virtual networking experience along with security posture for Azure NetApp Files.
You are now able to choose between standard or basic network features while creating a new Azure NetApp Files volume:
- Basic provide the current functionality, limited scale, and features.
- Standard provides the following new features for Azure NetApp Files volumes or delegated subnets:
- Increased IP limits for Vnets with Azure NetApp Files volumes. This is at par with VMs to enable you to provision Azure NetApp File volumes in your existing topologies or architectures. This eliminates the need to rearchitect network topologies to use Azure NetApp Files for workloads like VDI, AVD, or AKS.
- Enhanced network security with support for network security groups (NSG) on the Azure NetApp Files delegated subnet.
- Enhanced network control with support for user-defined routes (UDR) to and from Azure NetApp Files delegated subnets. You can now direct traffic to and from Azure NetApp Files via your choice of network virtual appliances for traffic inspection.
- Connectivity over active or active VPN gateway setup for highly available connectivity to Azure NetApp Files from on-premises network.
- ExpressRoute FastPath connectivity to Azure NetApp Files. FastPath improves the data path performance between on-premises network and Azure Virtual Network.
This general availability for standard network features is currently in20 regions and will rollout to other regions.
Source: General availability: Standard network features for Azure NetApp Files
Azure Daily 2022 - Sep 08, 2022
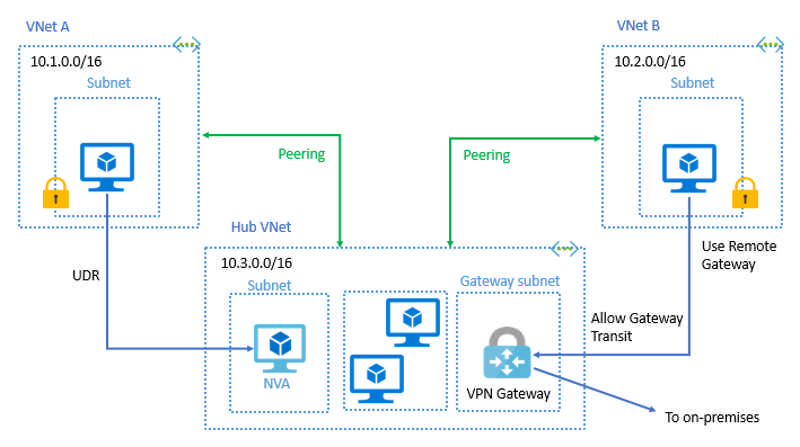
Auditing for Azure SQL database has started supporting User Managed Identity. Auditing can be configured to Storage account using two authentication methods, managed identity and storage access keys. For managed identity you can use system managed identity or user managed identity. To know more about UMI in azure refer here
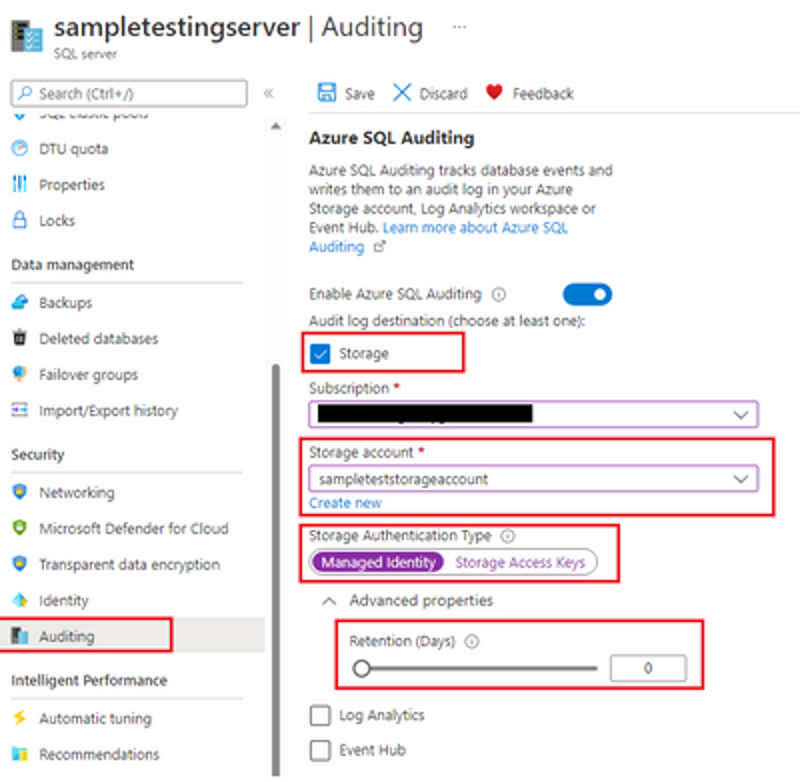
To configure writing audit logs to a storage account, select Storage when you get to the Auditing section. Select the Azure storage account where logs will be saved, you can use two storage authentication types i.e., managed identity and storage access keys.
Read more at Azure Daily 2022
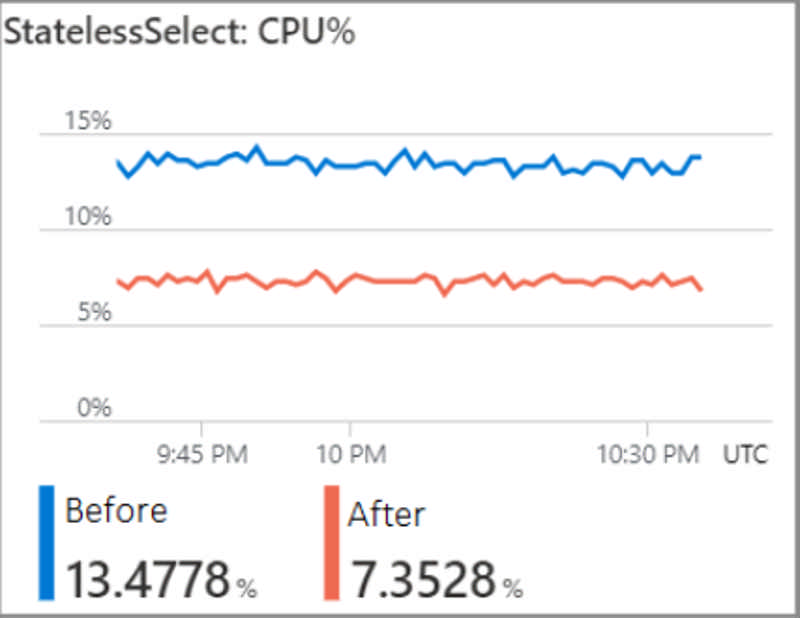
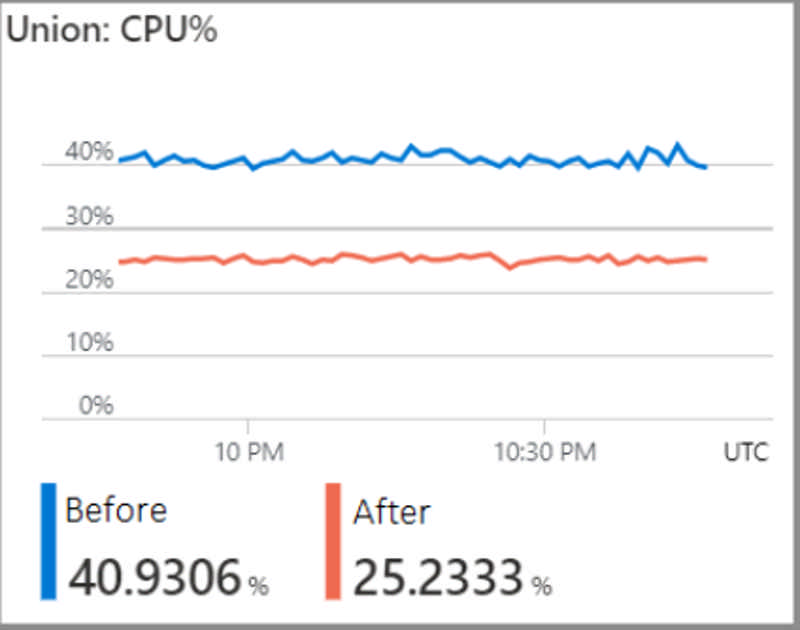
General availability: Up to 45% performance gains in stream processing
Announcing an up to 45% performance boost for CPU intensive jobs by default. This improvement allows you to reduce the number of streaming units assigned to such jobs and save on costs without impacting performance.
Source: General availability: Up to 45% performance gains in stream processing
Resource instance rules enable secure connectivity to a storage account by restricting access to specific resources of select Azure services.
Azure Storage provides a layered security model that enables you to secure and control access to your storage account. You can configure network access rules to limit access to your storage account from select virtual networks or IP address ranges. Some Azure services operate on multi-tenant infrastructure, so resources of these services cannot be isolated to a specific virtual network.
With resource instance rules, you can now configure your storage account to only allow access from specific resource instances of such Azure services. For example, Azure Synapse offers analytic capabilities that cannot be deployed into a virtual network. If your Synapse workspace uses such capabilities, you can configure a resource instance rule on a secured storage account to only allow traffic from that Synapse workspace.
Resource instances must be in the same tenant as your storage account, but they may belong to any resource group or subscription in the tenant.
Source: Generally available: Resource instance rules for access to Azure Storage
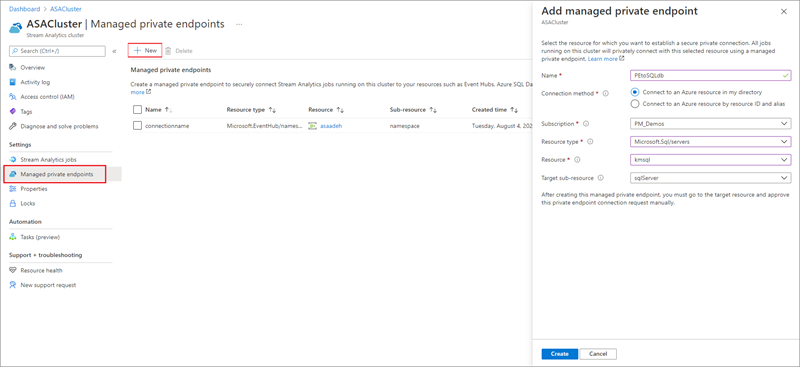
You can now use Stream Analytics clusters to securely connect your jobs to write to dedicated synapse SQL pools using managed private endpoints. Setting this up is a simple, two step operation. First add synapse SQL output to your job. Then go to your Stream Analytics cluster to add a managed private endpoint that establishes a secure, private connection between your resources. Learn how to configure managed private endpoints in your Stream Analytics cluster.
Source: General availability: Managed private endpoint support to Synapse SQL output
The general purpose Dps v5 and Dpds v5 Azure Virtual Machines series can run popular Linux enterprise workloads such as web and application servers, open-source databases, Java and .Net applications, gaming, and media servers, and more. The new VMs provide up to 4GiBs of memory per vCPU in sizes with up to 64 vCPUs, 208GiB of memory, and 40Gbps networking, with and without local temporary storage.
The Dpls v5 and Dplds v5 VM series offer one of the lowest starting price points within the general-purpose Azure Virtual Machines portfolio, providing 2GiBs per vCPU in sizes up to 64vCPUs, 128GiBs of memory, and up to 40Gbps networking with and without local temporary storage options.
Lastly, the memory optimized Eps v5 and Epds v5 VM series feature up to 8GiBs of memory per vCPU in sizes with up to 32 vCPUs, 208GiBs of memory, 40Gbps networking, with and without local temporary storage options, and are designed to meet the requirements associated with memory-intensive Linux-based workloads including open-source databases, in-memory caching applications, and data analytics engines.
All the VM series listed above are now generally available in multiple regions and feature the Ampere Altra Arm-based processor operating at up to 3.0GHz frequency. The Altra Arm-based processor was architected for scale-out cloud environments to deliver efficient performance and help reduce overall environmental impact of computing operations.
Source: Generally available: New Azure Virtual Machines with Ampere Altra Arm-based processors
Generally available: Enterprise-grade edge for Azure Static Web Apps
Enterprise-grade edge for Azure Static Web Apps is now generally available. Enable faster page loads, enhance security, and optimize reliability for your global applications. Enterprise-grade edge combines the capabilities of Azure Static Web Apps, Azure Front Door, and Azure Content Delivery Network (CDN) into a single secure cloud CDN platform.
Key features:
- Global presence in 118+ edge locations across 100 metro cities
- Caching assets at the edge
- Proactive protection against Distributed Denial of Service (DDoS) attacks
- Native support of end-to-end IPv6 connectivity and HTTP/2 protocol.
- Optimized file compression.
Source: Generally available: Enterprise-grade edge for Azure Static Web Apps
The Kusto Emulator is a Docker Container encapsulating the Kusto Query Engine available locally in a Docker Container. The Kusto Emulator was designed to enable local development and automated testing and is a free offering under the following license terms.
Automated testing can be done using the Kusto Emulator without provisioning an Azure Service and without connection to the internet. It can be an efficient way to use Kusto Query Engine for automated tests. Local development can be done without relying on an internet connection or a provisioned service.
Source: Generally available: Azure Data Explorer Kusto Emulator
The 1.4 version is the latest long term servicing (LTS) release of IoT Edge. This release will be serviced with fixes for regressions and critical security issues through November 12, 2024 (product lifecycle). This release also marks the end of servicing for the 1.3 release which will no longer receive bug fixes or security patches. The release is based on 1.3 and brings the following improvements in addition to long term servicing:
- Automatic cleanup of unused Docker images
- Ability to pass a custom json payload to DPS on provisioning
- Ability to require all modules in a deployment be downloaded before (re)starting any
- Use of the TCG TPM2 Software Stack which enables TPM hierarchy authorization values, specifying the TPM index at which to persist the DPS authentication key, and accommodating more TPM configurations
Full release notes can be found on the GitHub release page for 1.4.0. The companion release of Azure IoT Edge for Linux on Windows (EFLOW) 1.4 LTS will be coming later this fall. Release notes for EFLOW can be found on the EFLOW GitHub releases page.
Azure Cache for Redis now supports authenticating storage account connections using managed identity. Identity is established through Azure Active Directory, and both system-assigned and user-assigned identities are supported. This allows you to establish trusted access to storage for uses including data persistence and importing/exporting cache data. Using managed identity to connect to storage account limits the need to manage storage keys and gives you tighter and more secure control over storage account access.
Source: General availability: Managed identity to connect Azure Cache for Redis to storage
App Service and Azure Functions now support referencing configuration key-values from the Azure App Configuration service. App Configuration provides central management of configuration key-values that can span resources and deployment environments. When defining an application setting or connection string within App Service and Azure Functions, instead of providing a direct value, you can now specify a key-value in an external Azure App Configuration store. The app uses its managed identity to resolve the value from the store and expose it as an environment variable to your application.
This initial preview does not yet include support for network-restricted configuration stores or for resolution of configuration store references to Key Vault. Referenced key-values are not yet refreshed automatically, and new values will only be pulled in when the app restarts as the result of another config change such as modifying an app setting.
Source: Public preview: App Configuration references for App Service and Azure Functions
Use Azure Cosmos DB integrated cache to optimize read costs and latency for both point reads and queries. The Azure Cosmos DB integrated cache is an in-memory cache built-in to the Azure Cosmos DB dedicated gateway. The dedicated gateway is optional front-end compute that stores cached data and routes requests to the backend database. There’s no need to make code changes in your application to use the dedicated gateway and utilize the integrated cache. Integrated cache is currently available for Core (SQL) API only.
Source: General availability: Azure Cosmos DB integrated cache
Resizing a disk on Azure can provide increased storage capacity and better performance for your applications. As part of our commitment to continuously add new capabilities to our Azure Disk Storage portfolio, live resize for Premium SSD and Standard SSD Disk Storage is now generally available.
With live resize, you can dynamically increase the storage capacity of your Premium SSD and Standard SSD disks without causing any disruption to your applications. To reduce costs, you can start with smaller disks and gradually increase their storage capacity without experiencing any downtime.
Source: Generally available: Live resize for Premium SSD and Standard SSD Disk Storage
The Event Grid blob trigger handles events raised by a storage account and is now generally available.
The extension allows you to reduce latency by triggering on an event subscription to the same blob container. The event subscription uses Event Grid to forward changes in the blob container as events for your function to consume.
Source: Generally available: Azure Functions extension for Event Grid blob trigger
Ephemeral OS disk customers can choose encryption type between platform-managed keys or customer-managed keys for host-based encryption. The default is platform-managed keys. This feature would enable our customers to meet your organization's compliance needs.
Source: Public preview: Ephemeral OS disks supports host-based encryption using customer managed key
IPv6 support for Global Reach unlocks connectivity between on-premise networks, via the Microsoft backbone, for customers with dual-stack workloads. Establish Global Reach connections between ExpressRoute circuits using IPv4 subnets, IPv6 subnets, or both. This configuration can be done using Azure Portal, PowerShell, or CLI.
Source: General availability: ExpressRoute IPv6 Support for Global Reach
Process your real-time data streams in Azure Event Hubs using Azure Stream Analytics. The no-code editor allows you to easily develop a Stream Analytics job without writing a single line of code. You can develop and run a job that tackles many scenarios within minutes.
There are four new features that will help you build and monitor your jobs:
- Managed identity: You can now use ‘managed identity’ as authentication mode in Event Hub streaming input, Cosmos DB streaming output, and Azure Data Lake Storage Gen2. Managed identities eliminate the limitations of user-based authentication methods, like the need to reauthenticate because of password changes or user token expirations that occur every 90 days.
- Azure Data Lake StorageGen2 reference data: You can now use Azure Data Lake Storage Gen2 as reference data in the query. Reference data is either static or changes slowly over time. It is typically used to enrich incoming streaming and do lookups in your job.
- Metrics: You can now monitor the health of your job by viewing metrics within no code editor. The metrics shown are for the last one hour by default. You can select any time ranging from the last 1 hour to 30 hours to view metrics for the job.
- Save job: You can now save your job anytime while creating it. For starting the job, you have to configure the Event Hub, transformations, and streaming outputs for the job.
Note: While the no code editor is in preview, the Azure Stream Analytics service is generally available.
Source: Public preview: Four new features in no code editor in Event Hubs
Azure App Configuration now supports replicating your configuration data in the configuration store to replicas in other Azure regions. Available to standard tier subscribers, any updates or additions to key/values in the configuration store or in a replica will be automatically synchronized, using an eventual consistency model. This delivers benefits including:
- Increased resiliency – Replication across regions means that your configuration data will still be accessible should a service outage impact your store or any one of the replicas.
- Minimize latency – Now your applications can consume the data locally rather than issuing cross-region requests.
- Optimize request distribution – Replicas and the configuration store have unique applicable request limits, enabling you to distribute requests efficiently to avoid exhausting the request limits on either the replicas or the configuration store.
Source: Public preview: App Configuration geo replication support
Use server logs for Azure Database for MySQL - Flexible Server to enable logging for your server and save the results to a file. If you enable server logs and select the log type, you can download the logs from your server. Use the information in these logs to get detailed insights about the activities executed on your server, and then identify and troubleshoot potential issues.
Source: General availability: Server logs for Azure Database for MySQL - Flexible Server
Save up to 55 percent on your usage of the Enterprise and Enterprise Flash tiers of Azure Cache for Redis by purchasing reserved instances. The reservation discount will automatically apply to your matching cache resources so the process of purchasing a reservation is streamlined. Reservations are available on a one-year basis for up to a 35 percent discount or on a three-year basis for a 55 percent discount. This is a great way to maximize the cost efficiency of your Azure deployment and ensure you get the best deal.
Source: General availability: Reserved instance pricing for Azure Cache for Redis Enterprise
Today, we are announcing the general availability for a new Public IP capability on Azure VMware Solution. Most customer applications running on Azure VMware Solution require internet access. These applications require both outbound and inbound internet connectivity. Azure VMware Solution Public IP is a simplified and scalable solution for running these applications. With this capability, we enable the following.
- Direct inbound and outbound internet access for AVS to the NSX-T Edge.
- The ability to receive up to 1000 or more Public IPs.
- DDoS Security protection against network traffic in and out of the internet.
- Enable support for VMware HCX (migration tool for VMware VMs) over the public internet.
Source: Generally available: Public IP Capability for Azure VMware Solution
Azure Dedicated Host is a service that provides physical servers, able to host one or more virtual machines, dedicated to one Azure subscription. Dedicated hosts are the same physical servers used in our data centers, provided as a resource.
You can provision dedicated hosts within a region, availability zone, and fault domain. Then, you can place AKS VMs directly into your provisioned hosts, in whatever configuration best meets your needs.
Using Azure Dedicated Hosts for nodes with your AKS cluster enables:
- Hardware isolation at the physical server level. No other VMs will be placed on your hosts.
- Control over maintenance events initiated by the Azure platform. With dedicated hosts, you can opt-in to a maintenance window to reduce the impact to your service.
Disaster Recovery to cloud is a resilient and cost-effective way of protecting the workloads against site outages and data corruption events like ransomware. Leveraging the VMware VAIO framework, on-premise VMware workloads can be replicated to Azure Blob storage and recovered with minimal or close to no data loss and near-zero recovery time objective (RTO). JetStream Disaster Recovert (DR) can seamlessly recover workloads replicated from on-premises to Azure VMware Solution. JetStream DR enables cost-effective disaster recovery by consuming minimal resources at the disaster recovery site as well as using cost-effective cloud storage.
JetStream DR can also replicate and automate recovery to Azure NetApp Files datastores. It can recover independent VMs or groups of related VMs into the recovery site infrastructure according to runbook settings. It also provides point-in-time recovery for ransomware protection.
Source: Generally available: JetStream DR for AVS supports Azure NetApp Files datastores
Azure Load Testing now supports load testing for private endpoints. You can create an Azure Load Testing resource and enable it to generate load from within your virtual network (VNET injection).
This functionality enables the following usage scenarios:
- Generate load to an endpoint that is deployed in an Azure virtual network
- Generate load to a public endpoint with access restrictions, such as restricting client IP addresses
- Generate load to an on-premises service, not publicly accessible that is connected to Azure via ExpressRoute
Source: Public preview: Microsoft Azure Load Testing supports private endpoints testing
Network security groups (NSGs) support for private endpoints is now generally available. This feature enhancement provides you with the ability to enable advanced security controls on traffic destined to a private endpoint. In order to leverage this feature, you will need to set a specific subnet level property, called PrivateEndpointNetworkPolicies, to enabled on the subnet containing private endpoint resources.
At this time, Private Link network security group support is available in most public regions.
Source: General availability: Network security groups support for private endpoints
User-defined routes (UDRs) support for private endpoints is now generally available. This feature enhancement will remove the need to create a /32 address prefix when defining custom routes. You will now have the ability to use a wider address prefix in the user defined route tables for traffic destined to a private endpoint (PE) by way of a network virtual appliance (NVA). In order to leverage this feature, you will need to set a specific subnet level property, called PrivateEndpointNetworkPolicies, to enabled on the subnet containing private endpoint resources.
Source: General availability: User-defined routes support for private endpoints
Microsoft Dev Box is now in public preview. Microsoft Dev Box provides self-service access for developers to high-performance, cloud-based workstations preconfigured and ready-to-code for specific projects—all while maintaining security and corporate governance. With Microsoft Dev Box, organizations can:
- Maximize dev productivity with ready-to-code, self-service Dev Boxes.
- Centralize governance of workstations running anywhere to maintain greater security, compliance, and cost efficiency.
- Customize dev boxes with everything developers need for their current projects.
Today we are officially announcing availability of the migration capability to move your existing VMware virtual machine, protected using Azure Site Recovery, from classic protection experience to modernized protection experience. With this capability, customers can move their existing replications of VMware virtual machines enabled using configuration server, to the modernized experience enabled using the ASR replication appliance.
The migration is guided by a smart detection mechanism, which ensures that complete initial replication is not performed again for non-critical replicated items. The capability calculates and provides estimated migration time to better assist customers and plan their migration. Additionally, the tool is integrated with a robust rollback mechanism. If the migration fails due to any reason, the operation will be automatically rolled back, and you will be moved back to the classic replication experience.
Moving to the modernized experience is recommended, as it aims at enhancing security, reducing manageability efforts, simplifying scale, cutting down manual intervention and adopting an automation first approach.
Source: General availability: Upgrade VMware VMs protected by Site Recovery to modernized experience
Update management center, the next iteration of Azure Automation Update Management solution, is now in public preview. It provides an out-of-the-box, easy-to-use experience for central management and governance of OS updates across all the machines, including:
-
Machines with Windows and Linux Operating systems.
-
Machines deployed on Azure, and on-premises or on other cloud platforms via Azure Arc.
You get the following key upgrades over Azure Automation update management solution:
-
Management and governance of updates for entire fleet of machines including Windows & Linux, Azure & Arc workloads.
-
No pre-requisites, zero onboarding steps.
-
Granular access control on each machine using Azure roles and identity.
-
Install updates right away or schedule them for a later date.
-
Flexibility to define scheduling windows including syncing patch cycles with patch Tuesdays (unofficial term for Microsoft’s scheduled security fix release on every second Tuesday).
-
New ways of patching such as automatic VM guest patching in Azure, hotpatch, or custom maintenance schedules
-
Policy driven enforcement of assessment and patching at scale.
You can now protect your Kubernetes clusters and container workloads from potential threats by restricting deployment of container images with vulnerabilities in their software components.
This feature allows you to use Azure Policy and Azure Defender for Containers to identify and patch vulnerabilities prior to deployment.
Source: Public preview: Policy blocking the deployment of vulnerable images
Custom domain suffix capability is now available in App Service Environment (ASE), an Azure App Service feature that provides a fully isolated and dedicated environment for running App Service apps securely at high scale. Your apps are not restricted by the DNS settings for your App Service Environment’s default domain suffix to only be accessible by those domain names. Custom domain suffix is an internal load balancer (ILB) App Service Environment feature that allows you to use your own domain suffix to access the apps in your App Service Environment.
Source: General availability: Azure App Service Environment v3 support for custom domain suffix
Data Platform Virtual Summit 2022 (DPS 2022) is right around the corner! A FREE, global learning event for data professionals, DPS 2022 features a couple of learning formats including breakouts & Data Gurukuls. This content will be delivered by Azure Data Engineering, partner organizations, community leaders, and Data Platform MVPs. From September 19 to 23, the event is fine-tuned for multiple time zones running as five editions, ANZ, APAC, INDIA, EMEA, and AMERICAS making it a truly global and inclusive learning event. This year at DPS 2022 the content will be delivered in 14 different languages other than English. Attendees will get to learn about the latest SQL Server and Azure Data innovations and gain deep technical skills to move ahead in their careers.
We shared at Microsoft Inspire that one of our most anticipated features, Autoscale for pooled host pools, will soon be Generally Available on Azure Virtual Desktop. Today, we are happy to announce that Autoscale for pooled host pools is officially Generally Available!
The Enterprise and Enterprise Flash tiers of Azure Cache for Redis now support the popular RedisJSON module. This module adds native functionality to store, query, and search JSON formatted data, which allows you to store data more easily in a document-style format in Redis. This simplifies common Redis use cases like storing product catalog or user profile data.
RedisJSON support implements the community version of the module the collaboration with Redis Incorporated so you can utilize your existing knowledge and workstreams. RedisJSON is additionally designed to be used with the search functionality of RediSearch (also available in Azure Cache for Redis) to provide integrated indexing and querying of data.
Source: Public preview: RedisJSON available in Azure Cache for Redis Enterprise
Azure Dedicated Host gives you more control over the hosts you deployed by giving you the option to restart any host. When undergoing a restart, the host and its associated VMs will restart while staying on the same underlying physical hardware.
With this new capability, now in preview, you can take troubleshooting steps at the host level.
Serverless SQL for Azure Databricks, a new capability for Azure Databricks SQL, provides instant compute to users for their BI and SQL workloads, with minimal management required and capacity optimizations that can lower overall cost. You only pay for Serverless SQL when users start running reports or queries.
Serverless SQL was built for the modern business analyst who works on their own schedules and wants instant compute available to process their queries without waiting for clusters to start up or scale out. Organizations with business analysts who want to analyze data in the data lake with their favorite BI tools, including Power BI, will benefit from this capability. This makes it easier for organizations to expand adoption of the lakehouse for business analysts who are looking to access the rich, real-time datasets of the lakehouse with a simple and performant solution.
The ability for GitHub Enterprise Cloud owners to display members’ IP addresses for all audit logs events for private repositories and other enterprise assets, such as issues and projects, is generally available.
These IP addresses can be used to improve threat analyses and further secure your software. Note, IP addresses will continue to not be displayed for activity related to public repositories.
Azure Database for PostgreSQL – Flexible Server provides maximum flexibility over your database, built-in cost-optimization controls, and support for latest PostgreSQL major versions compared to Single Server.
You typically must perform manual migrations using PostgreSQL dump and restore or using Azure Database Migration Service. The new migration tool (available in select regions) includes a seamless, inline experience to migrate your Single Server to Flexible Server and has automated a number of steps required for migration. It supports online and offline modes of migrations, and suitable for databases less than 1TB size.
Source: Public preview: Migration tool feature with Azure Database for PostgreSQL – Flexible Server
Currently, VMs running on Azure Dedicated Host support the use of Standard and Premium Azure disks as data disks. With this preview, we are introducing support for Azure Ultra Disks on Azure Dedicated Host.
Azure Ultra disks are highly performant disks on Azure that offer high throughput (maximum of 4000 MBps per disk) and high IOPS (maximum of 160,00 IOPS per disk) depending on the disk size.
If you are running IaaS workloads that are data intensive and latency sensitive, such as Oracle DB, MySQL DB, other critical databases, and gaming applications, you will benefit from using Ultra disks as data disks on VMs hosted on Azure Dedicated Host.
Source: Public preview: Azure Dedicated Host support for Ultra SSD
Currently, Azure Monitor VM insights requires a Log Analytics agent and a dependency agent installed on each virtual machine or virtual machine scale set to be monitored. This public preview will introduce a version of VM insights that makes use of the new Azure Monitor agent and would replace the existing Log Analytics agent.
Several key capabilities have been released in preview:
- Easy configuration using data collection rules to collect VM performance counters and specific data types.
- Option to enable/disable processes and dependencies data that provides Map view, thus, optimizing costs.
- Enhanced security and performance that comes with using Azure Monitor agent and managed identity.
Source: Public preview: Enable VM insights using Azure Monitor agent
The AKS node pool start/stop feature allows you to completely stop specific user node pools and pick up later where you left off with a switch of a button, saving time and costs.
Previously, you had to either scale a user node pool and all its workloads down to zero in order to save costs or keep it running with a low footprint to avoid re-deployment, adding to operations time, or wasting compute resources. The start/stop feature keeps user node pool configurations in place, like the previous node count, allowing you to pick up where you left off without reconfiguring the node pools.
Source: Generally available: AKS node pool user start/stop feature
With next hop IP support, you can deploy network virtual appliances (NVAs) behind an Azure Internal Load Balancer (ILB) to achieve key active-passive connectivity scenarios and improve connectivity performance. To learn more about this feature, check out next hop IP support.
Source: General availability: Next hop IP support for Route Server
Azure Kubernetes Service (AKS) provides the capability for organizations to deploy containers at scale. We are expanding the Azure confidential computing portfolio to enable AMD-based confidential VM node pools in AKS, adding defense-in-depth to Azure's already hardened security profile.
With the general availability of confidential virtual machines featuring AMD 3rd Gen EPYC™ processors, with Secure Encrypted Virtualization-Secure Nested Paging (SEV-SNP) security features, organizations get VMs with isolated, encrypted memory and genuine confidentiality attestation rooted to the hardware.
AKS is now equipped to have confidential and non-confidential node pools on a single cluster. This means that applications processing sensitive data can reside in a VM-level Trusted Execution Environment (TEE) node pool with memory encryption keys generated from the chipset itself.
Confidential node pools on AKS enable a seamless transition of Linux container workloads to Azure without the overhead of changing code.
Source: Public preview: AMD-based confidential VMs for Azure Kubernetes Service (AKS)
Previously, when creating a fork all branches from the parent repository were copied to the new fork repository. There are several scenarios where this is unneeded, such as contributing to open-source projects. When all branches are copied, it could result in slow repo cloning and unnecessary disk usage. With this new feature, only the default branch is copied; no other branches or tags. This may result in faster clones because only reachable objects will be pulled down.
Source: You can now fork a repo and copy only the default branch
Effective July 31 2022, all Public IPv6 Addresses and Public IPv6 Prefixes will be free. The Public IP billing meters will also reflect this change with updated naming: Basic IPv4 Public IP, Basic IPv4 Static Public IP, and Standard IPv4 Static Public IP.
For more information about Public IP pricing, visit the Public IP Pricing page. For more information about Public IPs, visit the Azure IP Services page.
Source: Generally available: Azure Public IPv6 offerings are free as of July 31
Azure IoT Central now gives you step-by-step instructions on how to connect your phone as a device so you can pilot key features. Connecting your phone to an Azure IoT Central application allows you to see raw data such as altitude and battery level flowing from your phone to the application. Once your phone is connected to Azure IoT Central, you will also have the ability to execute commands remotely. The tour gives you direct instructions on how to connect your phone to your Azure IoT Central application, configure a remote job, and create a new rule. The in-app guidance allows you to experience key capabilities of Azure IoT Central and prepares you for your IoT device onboarding.
To get started on the guided tour, navigate to the Azure IoT Central Build page to create a new application and then click on the Use phone as a device button to trigger the in-app guidance and explore the capabilities of Azure IoT Central.
Source: Generally available: Guided tour experience added to Azure IoT Central
Azure Synapse Analytics Spark pools now support elastic pool storage. Apache Spark in Azure Synapse Ananlytics utilize temporary disk storage while the Spark pool is instantiated. For many Spark jobs, it's difficult to estimate the pools storage requirements, which can cause some Spark jobs to fail if the temporay storage is exhausted. Today we are enabling elastic pool storage which allows the Spark engine to monitor worker node temporary storage and attach additional disks if needed. No action is required by you, plus you should see less job failures as a result.
Source: Public preview: Azure Synapse Analytics Spark elastic pool storage
Azure SignalR Service Premium Tier is now generally available. This plan provides greater resiliency, scalability, and flexibility.
Key features, including:
- An SLA including 99.95% availability.
- Availability Zone support: Distribute workloads evenly across multiple zones in a supported Azure region and redirecting traffic to other zones in the event of a failure.
- Autoscale capabilities: Specify rules that make it easy scale up and down to meet capacity needs and optimize resource usage.
- Custom domain support: Add your desired custom domain names to your application.
Source: Generally available: Azure SignalR Service Premium Tier
You can now configure your Azure Stream Analytics job to write to a table in your Azure SQL Database that hasn't yet been created. You have to do the following steps:
- Make sure that there is incoming streaming data in your Azure Stream Analytics job
- Write your Stream Analytics query (or use the existing template of Select *)
- Test your Stream Analytics query
- Select "Create table" - Stream Analytics will use the schema from Step 3 to create a new table in your SQL Database.
Source: Public preview: SQL DB output connector improvements in Stream Analytics
Direct shared gallery is a new feature of Azure Compute Gallery that simplifies the sharing of resources with all users within the same subscription, same tenant, different subscription and different tenants without the need for any auxiliary tokens. When the gallery is shared with a target subscription or tenant, all users in the subscription or tenant will have read-only access to the gallery and they can create a VM or a VM scale set on the target subscription.
Source: Public preview: Share images across subscriptions and tenants with new Compute Gallery feature
VM Apps is a service that simplifies the management, sharing, and global distribution of application packages at scale. The ability to manage application packages at scale is critical to you. Today, you can manage application packages in storage accounts. While this is secure and reliable, managing and deploying these packages at a scale is a challenge.
Using VM Apps, you can create and securely store application packages in an Azure Compute Gallery. The create experience is as simple as packaging all the application-related files (including install and uninstall scripts) in a compressed package and uploading it to Azure. Package management is simplified with logical grouping and versioning capabilities available with the feature. These packages can then be shared with other users in your organization, across subscriptions, and tenants, who can deploy them on VM. Shared Applications give you the flexibility to make application packages available to a VM, even if the VM is locked down with no internet access.
With VM Applications, you can now define application packages, replicate, share and deploy them automatically to your VMs and Virtual Machine Scale Sets using ARM templates, the portal, CLI, or PowerShell. Add an application to a VM or VMSS at creation, or add, remove, and update applications on existing resources.
This feature provides flexibility and simplicity in managing, sharing, and deploying applications. Some features include:
- Support for pre-deployment applications settings, or a default configuration across all deployments.
- Deploy VM Apps to VM or VMSS across subscriptions using IAM.
- Package your applications and configuration in either page blobs or block blobs and replicate them across the desired regions.
- Proxies all packages to prevent direct access to any of the replicas from the VM.
- Ability to auto select “latest” available VM Apps version when installing an application.
Source: General availability: VM Applications – Manage and deploy applications to VMs and VMSS
Customers and Azure partners who are looking to build business continuity and disaster recovery solutions can use VM restore points to capture app consistent and crash consistent backups natively on the Azure platform. This can then be used to restore disks and VMs during scenarios such as data loss, data corruption, or disaster recovery.
The new Predefined and CustomV2 policies on Application Gateway come with TLS v1.3 support. They provide improved security and performance benefits, fulfilling the needs of your enterprise security policies. You may use out-of-the-box predefined policies or configure a preferred cipher-suite list by using the CustomV2 policy.
Source: Public preview: TLS 1.3 support on Application Gateway
This week at Microsoft Inspire it announced that Scheduled Agent Updates on Azure Virtual Desktop is now Generally Available!
This feature gives IT admins control over when the Azure Virtual Desktop agent, side-by-side stack, and Geneva Monitoring agent get updated. You can specify the time of day you want to update the Azure Virtual Desktop agent. You can schedule agents to be deployed at convenient times such as outside peak business hours so that business critical work and end user productivity is not interrupted.
To enable this feature in the Azure Portal, simply select the Scheduled Agent Updates tab for your host pool, check the box to enable Scheduled Agent Updates, enter your desired maintenance window and time zone setting, and select Apply.
Today, Azure SQL Managed Instance supports cross-instance distributed transactions, meaning that you can run distributed transactions between multiple databases hosted on several managed instances.
The scope of this improvement can enable you to run distributed transactions between Azure SQL Managed Instance and other distributed transaction participants and that includes:
- Azure SQL Managed Instance
- SQL Server hosted anywhere
- Relational Database Management Systems
- Other software that can participate in distributed transactions, such as MSMQ.
Running distributed transactions in a heterogenous environment can enable you to perform transparent migration of your databases from SQL Server; to entirely or partially migrate or modernize your existing solutions; and develop new applications with complex transactional patterns on Azure SQL Managed Instance.
Today, Azure SQL Managed Instance supports cross-instance distributed transactions, meaning that you can run distributed transactions between multiple databases hosted on several managed instances.
The scope of this improvement can enable you to run distributed transactions between Azure SQL Managed Instance and other distributed transaction participants and that includes:
- Azure SQL Managed Instance
- SQL Server hosted anywhere
- Relational Database Management Systems
- Other software that can participate in distributed transactions, such as MSMQ.
Running distributed transactions in a heterogenous environment can enable you to perform transparent migration of your databases from SQL Server; to entirely or partially migrate or modernize your existing solutions; and develop new applications with complex transactional patterns on Azure SQL Managed Instance.
You can now get advisor recommendations scoped to a business unit, workload, or team and filter recommendations and calculate scores using tags you have already assigned to Azure resources, resource groups, and subscriptions. You can also use tag filters to:
1. Identify cost-saving opportunities by business units
2. Optimize critical workloads by comparing scores
Your organization can fully benefit from this functionality if a tagging strategy is adopted.
Azure Monitor for SAP solutions (version 2) is in public preview. SAP on Azure customers can collect and visualize end-to-end technical monitoring for SAP workloads in the Azure portal. Both SAP BASIS teams and infrastructure teams can use this product to view SAP telemetry and infrastructure telemetry at one place. Azure Monitor for SAP solutions is easy to use, deploy, and maintain.
Going forward, the new product version launched today will be referred to as Azure Monitor for SAP solutions (AMS). The previous version of product will be referred to as Azure Monitor for SAP Solutions (classic).
Azure Monitor for SAP solutions provides telemetry for SAP NetWeaver, SAP HANA, High-availability (Pacemaker) Linux clusters, Microsoft SQL Server, IBM Db2, and Operating System (Linux). You can view pre-defined alert templates and configure alerts of your choice with few clicks.
This release of Azure Monitor for SAP solutions comes with new architecture. Azure Functions is a collector unit and makes connections to source systems that need to be monitored to collect telemetry data. Telemetry data is stored in Azure Log Analytics.
Microsoft announced the preview of Premium SSD v2, the next generation of Microsoft Azure Premium SSD Disk Storage. This new disk offering provides the most advanced block storage solution designed for a broad range of input/output (IO)-intensive enterprise production workloads that require sub-millisecond disk latencies as well as high input/output operations per second (IOPS) and throughput—at a low cost. With Premium SSD v2, you can now provision up to 64TiBs of storage capacity, 80,000 IOPS, and 1,200 MBPS throughput on a single disk. With best-in-class IOPS and bandwidth, Premium SSD v2 provides the most flexible and scalable general-purpose block storage in the cloud, enabling you to meet the ever-growing demands of your production workloads such as—SQL Server, Oracle, MariaDB, SAP, Cassandra, Mongo DB, big data, analytics, gaming, on virtual machines, or stateful containers. Moreover, with Premium SSD v2, you can provision granular disk sizes, IOPS, and throughput independently based on your workload needs, providing you more flexibility in managing performance and costs.
With the launch of Premium SSD v2, our Azure Disk Storage portfolio now includes one of the most comprehensive sets of disk storage offerings to satisfy workloads ranging from Tier-1 IOPS intensive workloads such as SAP HANA to general purpose workloads such as RDMS and NoSQL databases and cost-sensitive Dev/Test workloads.
Today we are announcing improvements that 1) Enable resumable database backup restores for Azure SQL Managed Instance in case of impactful system updates, and 2) Removal of the 36 hrs. limitation to hold off system updates once a migration from SQL Server to managed instance has started. These improvements apply to Log Replay Service (LRS), Azure SQL migration extension for Azure Data Studio, and Azure Database Migration Services (DMS).
Log Replay Service (LRS) is our implementation of the SQL Server log shipping to the cloud, and perhaps the most used feature for orchestration of migration jobs from SQL Server 2008-2019 to Azure SQL Managed Instance. LRS infrastructure powers Azure SQL migration extension for Azure Data Studio, and Azure Database Migration Services (DMS). Azure Blob Storage is used as an intermediary to store backup files from SQL Server, and LRS is used to restore these backup files on managed instance in NORECOVERY mode. Customers can add differential and log backups continuously to Azure Blob Storage, and these will be continuously restored on Managed instance. Once the last backup file has been restored, and manual or automated cutover initiated, the migration is complete.
Previously, Microsoft announced the public preview release of Gateway Load Balancer (GWLB), a new SKU of Azure Load Balancer targeted for transparent NVA (network virtual appliance) insertion supported by a growing list of NVA providers. Today, placing NVAs in the path of traffic is a growing need for customers as their workloads scale. Common use cases of NVAs we’ve seen are:
- Allowing or blocking specific IPs using virtual firewalls.
- Protecting applications from DDoS attacks.
- Analyzing or visualizing traffic patterns.
And GWLB now offers the following benefits for NVA scenarios:
- Source IP preservation.
- Flow symmetry.
- Lightweight NVA management at scale.
- Auto-scaling with Azure Virtual Machines Scale Sets (VMSS).
With GWLB, bump-in-the-wire service chaining becomes easy to add on to new or existing architectures in Azure. This means customers can easily “chain” a new GWLB resource to both Standard Public Load Balancers and individual virtual machines with Standard Public IPs, covering scenarios involving both highly available, zonally resilient deployments and simpler workloads.
Figure 1: GWLB can be associated to multiple consumer resources, including both Standard Public Load Balancers and Virtual Machines with Standard Public IPs. When GWLB is chained to the front-end configuration or VM NIC IP configuration, unfiltered traffic from the internet will first be directed to the GWLB and then reach the configured NVAs. The NVAs will then inspect the traffic and send the filtered traffic to the final destination, the consumer application hosted on either the load balancer or virtual machine.
Source: Gateway Load Balancer now generally available in all regions
With the latest preview release for Azure IoT Central REST API (2022-06-30), there is now preview support for a series of new endpoints. Note: these capabilities should be leveraged to develop and test your solutions; however, you should avoid the use of any preview endpoints within your production scenarios. The Azure IoT Central product group strives for high stability across all of our preview and generally available endpoints; however, it reserves the right to change the preview endpoint schema based on customer feedback.
Source: Public preview: 2022-06-30 Azure IoT Central REST API release is now live
You can now set a retry policy using Event Hubs or timer triggers that re-execute a function until successful execution or the maximum number of retries occur.
Source: Generally available: Azure Functions retry policy for Event Hubs and timer triggers
As part of our commitment to delivering the best possible value for Azure confidential computing, we're announcing the support to create confidential VMs using Ephemeral OS disks. This enables customers using stateless workloads to benefit from the trusted execution environments (TEEs). Trusted execution environments protect data being processed from access outside the trusted execution environments.
Source: Public preview: Ephemeral OS disk support for confidential virtual machines
Azure Active Directory (Azure AD) authentication for Azure Monitor Application Insights is now fully released. By using Azure AD, you can now ensure that only authenticated telemetry is ingested in your Application Insights resources.
Typically, using various authentication systems can be cumbersome and pose risks since it’s difficult to manage credentials on a large scale. You can now choose to opt out of local authentication and ensure only telemetry that is exclusively authenticated using Managed Identities and Azure Active Directory is ingested in your Application Insights resource.
This feature is a step to enhance the security and reliability of the telemetry used to make both critical operational (alerting/autoscale etc.) and business decisions.
Source: General availability: Azure Active Directory authentication for Application Insights
The standard test can run any single request test required and is a major upgrade on the existing URL ping test. It has the reactive SSL check but also a proactive SSL certificate check. You can set a time period before a certificate expires to be alerted that it will need to be updated. The standard test also has a dedicated configuration section for more advanced tests, can be deployed in up to 16 locations.
As part of this release, standard tests will now incur additional costs to continue to utilize. If you have set up standard tests as part of the preview, these will no longer run without cost.
Source: General availability: Application Insights standard test for synthetic monitoring
With Windows Server 2022 support, you can now enable Container Insights for your AKS clusters running on this operating system.
The following limitations apply to Windows Server 2022 clusters:
- A maximum of 30 Windows Server containers are supported
- Windows does not provide the Memory RSS metric
- Disk Storage capacity information is not available
- Only Kubernetes, not Docker, environments are monitored
Source: Public preview: Container Insights now supports Windows Server 2022
Azure Monitor Agent (AMA) provides a secure, cost-effective, simplified, and performant way to collect telemetry data from Azure Virtual Machines, Virtual Machine Scale Sets, Arc-enabled servers, and Windows client devices. You must migrate from the Log Analytics agent (MMA or OMS agents) to this agent before August 2024. To make this process easier for you, we are launching a public preview today of agent migration tools.
AMA Migration Helper: A workbook-based solution in Azure Monitor that helps you discover what to migrate and track progress as you move from legacy agents to Azure Monitor agent on your virtual machines, scale sets, on-premise and Arc-enabled servers in your subscriptions. Use this single glass pane view to expedite your agent migration journey.
Source: Public preview: Migration tools for Azure Monitor Agent
Azure Monitor Agent (AMA) replaces Log Analytics agents and provides a secure, cost-effective, simplified, and performant way to collect telemetry data from Azure Virtual Machines, Virtual Machine Scale Sets, Arc-enabled servers, and Windows client devices. Today we are announcing public preview support for installation and authentication of AMA extension at-scale using Managed Identity user-assigned mode. You can use the built-in policies and initiatives to deploy the agent extension across virtual machines and scale sets.
User-assigned identity is more scalable and resilient compared to system-assigned identity. It is recommended for at-scale installation using agent extension on Azure Virtual Machines and Virtual Machine Scale Sets.
Source: Public preview: User-assigned Managed Identity support for Azure Monitor Agent
Whether you're a new student, a thriving startup, or the largest enterprise, you have financial constraints, and you need to know what you're spending, where, and how to plan for the future. Nobody wants a surprise when it comes to the bill, and this is where Microsoft Cost Management comes in.
- Viewing cost in the Azure mobile app
- Introducing a new API for configuring cost alerts
- Prevent budget overages with action groups common alert schema
- Amplify your learning experience in Cost Management
- Help shape the future of navigation in Cost Management and Billing
- What's new in Cost Management Labs
- New ways to save money with Microsoft Cloud
- New videos and learning opportunities
- Documentation updates
- Join the Microsoft Cost Management team
Seamless data sharing between organizations eliminates data silos, facilitates data-empowered decisions, and unlocks tremendous competitive advantages. Traditionally, organizations have shared data with internal teams or external partners by generating data feeds requiring data copy and refresh pipelines investment. The result is a higher cost for data storage and movement, data proliferation (i.e., multiple copies of data), and delay in access to time-sensitive data. Near-real time access to data is the key to harnessing the true power and scale of big data in enterprise data lakes to effectively realize consistent and reliable data driven decisions.
Source: Share data near real-time with Microsoft Purview in-place data sharing for Azure Storage
Multi-user authorization (MUA) for Backup adds an additional layer of protection for critical operations on your recovery services vaults, providing greater security for your backups. To provide multi-user authorization, Backup uses a resource guard to ensure critical operations are performed with proper authorization. With this, Azure Backup provides improved protection against operations that could lead to potential loss of backup data, including:
- Disable soft delete and hybrid security settings
- Disable multi-user authorization protection
- Modify backup policy (to reduce retention)
- Modify protection (to reduce retention)
- Stop protection with delete data
- Change MARS security PIN
The backup administrator, who typically owns the recovery services vault, needs to gain the contributor role on the resource guard to be able to perform the aforementioned protected (critical operations). This also requires action from the owner of the resource guard to approve and grant the required access. You can also use Azure AD Privileged Identity Management to manage just-in-time access on the resource guard. Additionally, you can create the resource guard in a subscription or a tenant different from the one that has the recovery services vault, to achieve maximum isolation.
Please refer to the documentation to learn more about multi-user authorization for Azure Backup, and for details on configuration and use.
Source: Generally available: Azure Backup multi-user authorization for recovery services vaults
Restoring a backup file is the easiest way to copy a SQL Server database to another instance. It allows you to create a copy of your production database for easier troubleshooting or debugging of an issue, to provide a copy of a database to your end users or eligible third parties, or as a light-weight business continuity/disaster recovery solution to restore functionality on another instance of SQL Server. These are just a few use cases, and the list is much longer and there are some very inventive ways of using backup-restore in the wild.
Azure Advisor provides a personalized list of best practices for optimizing your Azure Database for MySQL - Flexible Server instance. The feature analyzes your resource configuration and usage telemetry and then recommends solutions that can help you improve the cost effectiveness, performance, reliability, and security of your Azure resources.
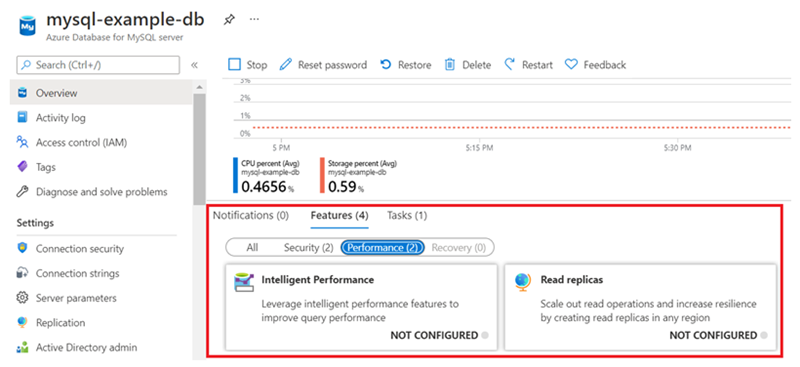
Source: General availability: Azure Advisor support for Azure Database for MySQL - Flexible Server
Azure Virtual Machine Backup enables you to create an enhanced policy to take multiple daily snapshots. Understanding your need to protect mission-critical workloads in Azure Virtual Machines, Azure Backup now previews low recovery point objective (RPO) to as low as four hours.
With this capability, you can define the duration your backup jobs would trigger and align your backup schedule with the working hours when there are frequent updates. Understanding your need for higher retention in instant restore, enhanced policy is designed to offer instant restore retention with a default of seven days retention and a maximum of 30 days. This ensures minimal data loss in the event of corruption or updates.
Source: Public preview: Multiple backups per day for Azure Virtual Machines
You can now apply a filter to limit exporting device data including telemetry, property changes, and device events from devices under an organization in your Azure IoT Central data exports. To apply this filter, use the organizations filter, under operator, and specify the organizations path as value in your Azure IoT Central data export. You can also include the entire organizations path in the export message. To include the organizations path, use the data transformation capability in data export to pass the "organizationPaths" in the outgoing message.
Source: Generally available: Export device data under an organization in Azure IoT Central
GitHub is transitioning map rendering services from MapBox to Azure Maps in our Free, Pro, and Team plans. This includes maps embedded in the site file viewer, embedded maps, and maps rendered in markdown. As part of the transition, custom icons and formatting of features in geojson and topojson files will no longer be supported. This change will not impact our Enterprise Cloud instances which will continue to use MapBox for map rendering. Documentation can be found here:
Durable Functions, an extension to Azure Functions that lets you define stateful serverless workflows in code, now supports Java. You can use Durable Functions to implement complex function orchestration that would otherwise require writing lots of boilerplate code for state management.
In this preview, you can leverage existing Durable Functions patterns such as "function chaining", "fan-out/fan-in", "async HTTP APIs", "monitor", and "human interaction". The sample below shows a simple, durable function that is triggered by an HTTP request and invokes tasks in a sequence.
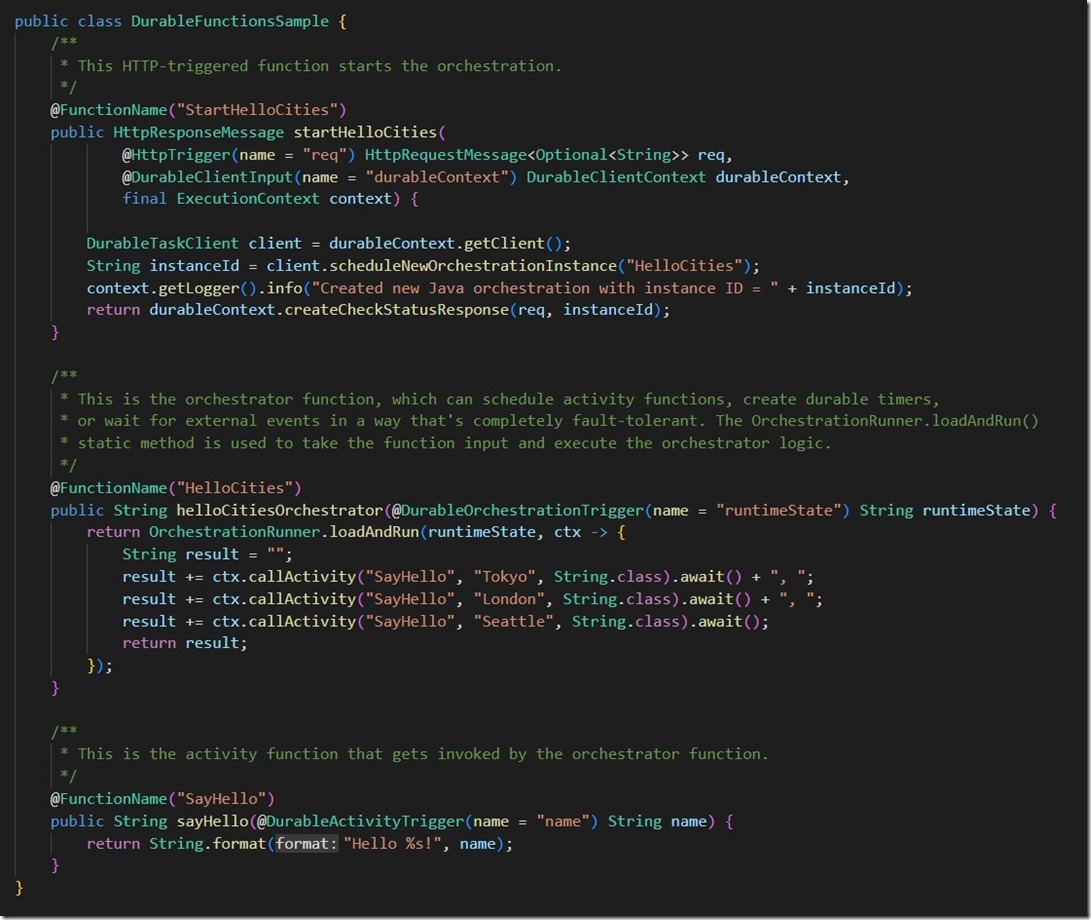
This version has a significant performance and robustness advantage over the old version.
To get a sense of improvement, consider this simple fan-out-fan-in orchestration of over 15k activities.
A fan-out-fan-in benchmark
Here we use Durable Functions Extension version 2.6.1 and run this benchmark on the Azure Functions Consumption plan for Windows. We then compare the performance of this benchmark between the npm package `durable-functions` version `1.5.4` and version `2.0.0`. See results below.
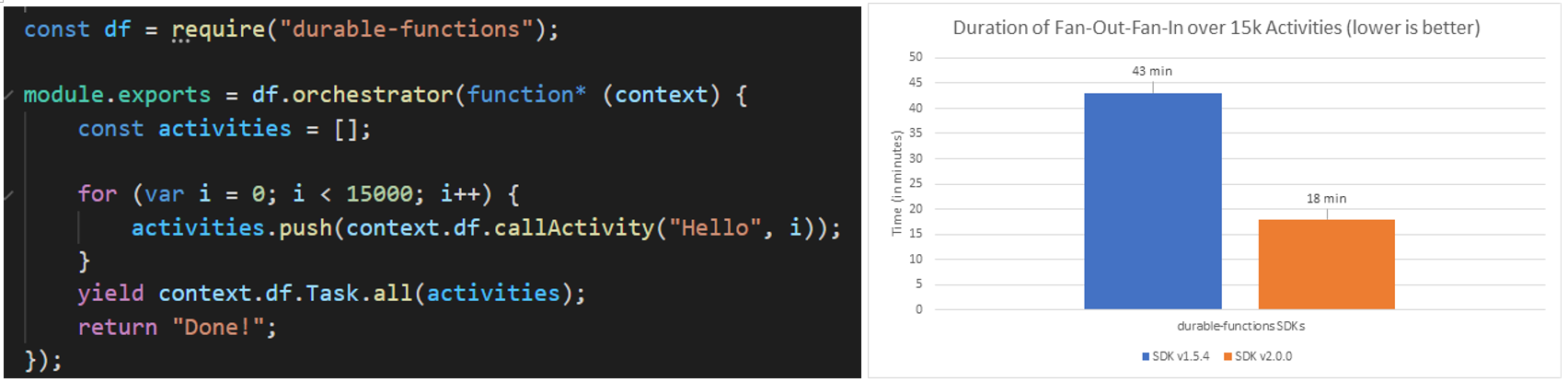
This release makes use of new features in the Durable Functions Extension to prevent race conditions that cause orchestrations to get stuck in large fan-out-fan-in scenarios, especially when durable timers are involved.
Try it out by installing version 2.0.0, or later of the SDK.
Important Note: This release has a few breaking changes for certain edge use cases. For details, please see our release notes.
Azure Kubernetes Service (AKS) clusters, whether deployed into a managed or custom virtual network, have certain outbound dependencies necessary to function properly.
Previously, in environments requiring internet access to be routed through HTTP proxies, this was a problem. Nodes had no way of bootstrapping the configuration, environment variables, and certificates necessary to access internet services.
This feature, now generally available, adds HTTP proxy support for AKS clusters, exposing a straightforward interface that cluster operators can use to secure AKS-required network traffic in proxy-dependent environments.
Source: Generally available: HTTP proxy support for AKS clusters
AKS support for Kubernetes release 1.24 is now in public preview. Kubernetes 1.24 delivers 46 enhancements. This release includes new changes such as the removal of Dockershim.
Source: Public preview: Kubernetes release 1.24 support in AKS
Our accessibility journey in Visual Studio has taught us that developers love to customize their experiences to help them be productive. Some developers have been telling us that they want to use sound to help them understand what’s happening in their code. A short, simple sound when the caret arrives on a line with an error can quickly help some developers understand where their attention needs to be.
Visual Studio Code introduced a handful of these audio cues, and many developers love them. We’re happy to bring them to Visual Studio.
Source: Listen Up, Visual Studio has a new feature you need to hear about!
The Azure Key Vault Secrets Provider extension enables fetching the secrets, keys, and certificates from an Azure Key Vault into an Arc-connected Kubernetes cluster. Remove the need to store and maintain secrets locally on the clusters and outsource the management of secrets to AKV as the central secrets management solution.
Source: General availability: Azure Key Vault secrets provider on Azure Arc enabled Kubernetes
Custom certificate authorities (CAs) allow you to establish trust between your Azure Kubernetes Service (AKS) cluster and your workloads as private registries, proxies, and firewalls. A Kubernetes secret is used to store the certificate authority's information until it is passed to all nodes in the cluster.
This feature is applied per node pool. Therefore, new and existing node pools must be configured to enable the feature.
You can now capture event streams of Azure Event Hubs in Parquet format to storage services.
Using Azure Event Hubs, no code editor for event processing, you can automatically capture streaming data in an Azure Data Lake Storage Gen2 account in Parquet format. The no code editor allows you to easily develop an Azure Stream Analytics job without writing a single line of code.
Source: Public preview: Apache Parquet capturing support in Azure Event Hubs
Today, we’re officially releasing GitHub Copilot, an AI pair programmer that suggests code in your editor, to all developers for $10 USD/month or $100 USD/year.
To show our appreciation to the Open Source and Learning communities, it will also be free to use for verified students and maintainers for popular open-source projects on GitHub.
Also thanks to users who are already in the technical preview program. You can continue enjoy free access until August 22nd.
Source: GitHub Copilot is now available to individual developers
Using application groups, you can create logical groupings between client applications that connect (publish or consume events) with Event Hubs and apply throttling and data access policies per each group. You can associate an application group with a uniquely identifiable condition such as the security context (shared access signatures (SAS) or Azure Active Directory (Azure AD) application ID - of the client application).
By defining an application group and using application group policies, you can throttle low priority producers or consumers while allowing high priority producers or consumers to stream data without any interruptions.
Source: Public preview: Resource governance for client applications in Azure Event Hubs
Azure Virtual Network Manager is now in public preview in nine new regions.
You can create an Azure Virtual Network Manager instance in nine additional regions and manage your virtual networks at scale across regions, subscriptions, management groups, and tenants globally from a single pane of glass.
- US South Central
- Southeast Asia
- Canada Central
- Japan East
- Japan West
- Australia East
- UK South
- Switzerland North
- Central India
With this announcement, Azure Virtual Network Manager public preview is now available in 20 Azure regions worldwide. Azure Virtual Network Manager helps you create your desired topologies like hub and spoke and mesh with just a few clicks. The security admin rules feature allows you to enforce security policies throughout your organization.
Source: Public preview: Azure Virtual Network Manager in nine new regions
Generate an authorization for the ExpressRoute Direct resource and redeem the authorization to create an ExpressRoute Circuit in a different subscription and/or Azure Active Directory Tenant. This feature is currently available in public preview.
Source: Public preview: ExpressRoute Direct and Circuit in different subscriptions
You can now benefit from remote management capabilities through a single pane of glass using the Windows Admin Center in order to manage multiple clusters from one central location.
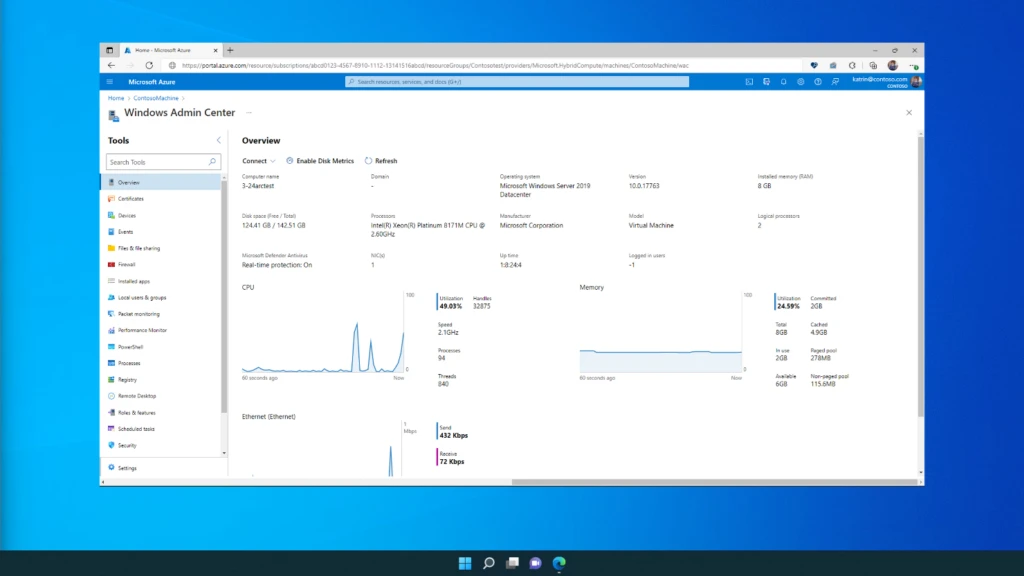
Source: Public preview: Windows Admin Center in the Azure portal
Azure Firewall Manager now supports managing DDoS Protection Plans for virtual networks and Azure Web Application Firewall (Azure WAF) policies for application delivery platforms: Azure Front Door and Azure Application Gateway.
Key benefits:
Central deployment and configuration
- Deploy and configure multiple WAF policies and DDoS plans
- Secure Azure Front Door Application Gateway with WAF policies at scale
- Protect Virtual Networks with DDoS plans and Azure Firewall simultaneously
- Upgrade from legacy WAF configuration to WAF policies on Application Gateway
View all application delivery platforms and virtual networks in a single place
- Gain visibility of all deployments across regions and subscriptions
Manage overall network security posture
- Adopt Zero-Trust principles by managing WAF, DDoS, and Azure Firewalls all in a central platform
- Monitor network security coverage in dashboard, across subscriptions
There are no additional charges for using WAF policy and DDoS management in Azure Firewall Manager.
Source: General availability: Azure WAF policy and DDoS management in Azure Firewall Manager
Azure Data Explorer connector for Power Automate, Logic Apps, and Power Apps enables you to automate alerts and notifications, orchestrate business workflows, and build low-code, no-code apps. This is done by using native Azure Data Explorer actions to execute KQL queries and commands on your cluster.
Some of the key scenarios that can be built using integration of Azure Data Explorer with Power Automate and Logic Apps:
- Automation of alerts and notifications
- Automation of recurring tasks and business workflows
- Automation of copy of data scenarios
- Automation of export of data
- Integration with Microsoft or 3rd party services
Some of the key scenarios that can be built using integration of Azure Data Explorer with Power Apps:
- Management of reference data
- Data entry scenarios such as audits in manufacturing plants
- Decision-making apps e.g. in energy and utilities industry, one of the common scenario is to predict the maintenance of machines and sending a technician to respond to those scenarios.
Source: General availability: Azure Data Explorer connector for Power Automate, Logic Apps, and Power Apps
To meet the demanding requirements of mission-critical enterprise workloads, new features are constantly added to Azure NetApp Files, and previously released preview features are moved into general availability. The following capabilities are recently generally available and no longer need registration for use: AES encryption for AD authentication, Backup policy users, Administrators privilege users and Dynamic change of service level.
Additionally, feature regional coverage continues to expand for Azure NetApp Files cross-region replication. The following are the cross-region replication region pair additions: Brazil South and South Central US, West US 3 and East US, Australia Central and Australia Central 2, France Central and West Europe.
Source: General availability: Feature general availability and feature expansion of regional availability
Azure Firewall Premium IDPS signature lookup is a great way to better understand the applied IDPS signatures on your network as well as fine-tuning them according to your specific needs. IDPS signatures lookup allows you to:
- Customize one or more signatures and change their mode to Disabled, Alert, or Alert and Deny. For example, if you receive a false positive where a legitimate request is blocked by Azure Firewall due to a faulty signature, you can use the signature ID from the network rules logs and set its IDPS mode to off. This causes the "faulty" signature to be ignored and resolves the false positive issue.
- You can apply the same fine-tuning procedure for signatures that are creating too many low-priority alerts, and therefore interfering with visibility for high-priority alerts.
- Get a holistic view of the entire 58,000 signatures.
- Smart search.
- Allows you to search through the entire signatures database by any type of attribute. For example, you can search for specific CVE-ID to discover what signatures are taking care of this CVE by typing the ID in the search bar.
Azure Databricks is a data analytics platform optimized for the Microsoft Azure cloud services platform. Azure Databricks offers three environments for developing data-intensive applications: Databricks SQL, Databricks Data Science & Engineering, and Databricks Machine Learning.
Azure Databricks is now generally available in Sweden Central and West Central US. For more information about Azure Databricks, see the Azure Databricks documentation.
Source: General availability: Azure Databricks available in new regions
With private link support, incoming traffic to an Azure Application Gateway frontend can be secured to clients running in another Azure Virtual Network, Azure subscription, or Azure subscription linked to a different Azure Active Directory tenant through Azure Private Link. Traffic between private endpoints in your virtual network and your Application Gateway will traverse a secure and private connection.
Source: Public preview: Private link support in Azure Application Gateway
The new Azure Monitor Agent (AMA) and the Data Collection Rules (DCR) improve on key areas of data collection. This includes cost reduction, improved security and performance, and easier management overall across its lifecycle. Upgrade your Azure Monitor Agents for Linux version to v1.19.3 to leverage these benefits on the latest distros like Ubuntu 22.04, Rocky Linux, and AlmaLinux.
Source: Generally available: Azure Monitor Agent available on latest Linux distros
Azure Functions now supports developing and editing applications, running on Linux, to be created and edited within the Azure portal.
Source: Public preview: Linux portal editing for applications
Network Watcher packet capture allows you to create packet capture sessions to track traffic to and from virtual machine scale set (VMSS) instances. This will help to diagnose network anomalies both reactively and proactively. Other uses include gathering network statistics, gaining information on network intrusions, debugging client-server communications, and more.
Packet capture is an extension that is remotely started through Network Watcher as virtual machine scale sets can have 2-100 instances. This capability eases the burden of running a packet capture manually on the desired virtual machine scale set instances, which saves valuable time. Packet capture can be triggered through the portal, PowerShell, CLI, or REST API. Filters are provided for the capture session to ensure you capture traffic you want to monitor. Filters are based on 5-tuple (protocol, local IP address, remote IP address, local port, and remote port) information. The captured data is stored in the local disk or a storage blob.
Source: Public preview: Network Watcher packet capture support for virtual machine scale sets
Azure Container Apps, a service for building and deploying modern applications and microservices using serverless containers, now supports custom domains and TLS certificates.
This feature is now generally available and allows you to use your own domains and TLS certificates to customize the hostname of your container apps and secure them using HTTPS.
Source: Generally available: Azure Container Apps support for custom domains and TLS certificates
Azure Container Apps, a service for building and deploying modern applications and microservices using serverless containers, now supports mounting Azure Files file shares and ephemeral volumes. This feature is currently in public preview.
Mount a file share to read and persist data in Azure Files. This is useful for loading large amounts of data without increasing the size of your container images. You can also use Azure Files to share data with other containers and applications.
With ephemeral storage, you can share data between multiple containers in a replica. Data written to ephemeral storage is persisted for the lifetime of the replica.
Source: Public preview: Mount Azure Files and ephemeral storage in Azure Container Apps
Microsoft is excited to introduce Azure Skills Navigator, a new learning resource designed especially for those that are new to Azure and want to learn more. Azure Skills Navigator is our very own ramp-up guide intended to help you develop a strong foundation on cloud technologies as you begin to explore Azure.
These downloadable Azure Skills Navigator guides offer a variety of resources to help build your skills and knowledge of Azure. Each guide features carefully selected digital training, learning courses, videos, documents, certifications, and more. Microsoft understands how important it is in today’s market to stay ahead of the tech curve. There is a high demand for professionals skilled in cloud technologies. Azure Skills Navigator guides ensure that you have a solid foundation as you begin exploring Azure. Microsoft has hand-picked a selection of resources that will help you develop a strong foundation of Microsoft Azure, allowing you to build and explore today. After you’ve mastered the content, Microsoft will help you navigate our intermediate and advanced level content.
With Azure VMware Solution you can now scale storage independently from compute using Azure NetApp Files datastores, enabling you to run VMware-based storage-intensive workloads like SQL Server, general-purpose file servers, and others in Azure.
Gain the flexibility and scalability of running your storage-heavy workloads on Azure VMware Solution, while delivering high performance and low latency.
Get started today
On Azure VMware Solution you can now scale storage independently of your compute costs and gain the performance, scalability, reliability, and security you need with Azure NetApp Files for Azure VMware Solution.
Source: Power your file storage-intensive workloads with Azure VMware Solution
Trusted launch is a seamless way to improve the security of generation 2 VMs. It protects against advanced and persistent attack techniques by combining technologies that can be independently enabled like secure boot and virtualized version of trusted platform module (vTPM).
Trusted launch support for VMs using Ephemeral OS disks is available in all Azure public regions. With this, customers using Ephemeral OS disk for VMs will benefit from the additional security offered by trusted launch.
Source: General availability: Trusted launch support for virtual machines using Ephemeral OS disks
When a file is renamed or moved to a new directory but half of it's contents remain the same, it's commit history will now indicate that the file was renamed, similar to git log --follow.
IPv6 support for Global Reach unlocks connectivity between on-premise networks, via the Microsoft backbone, for customers with dual-stack workloads. Establish Global Reach connections between ExpressRoute circuits using IPv4 subnets, IPv6 subnets, or both. This configuration can be done using Azure Portal, PowerShell, or CLI.
Source: Public preview: ExpressRoute IPv6 Support for Global Reach
Azure Firewall Manager now supports Azure Web Application Firewall (Azure WAF) policies for application delivery platforms, Azure Front Door, and Azure Application Gateway.
Key benefits:
Central deployment and configuration
- Deploy and configure multiple WAF policies
- Secure Azure Front Door Application Gateway with WAF policies at scale
- Upgrade from legacy WAF configuration to WAF policies on Application Gateway
View all application delivery platforms in a single place
- Gain visibility of all deployments across regions and subscriptions
Manage overall network security posture
- Adopt Zero-Trust principles by managing WAF, DDoS, and Azure Firewalls all in a central platform
There are no additional charges for using WAF policy management in Azure Firewall Manager. Learn more about pricing.
Source: Public preview: Manage Azure Web Application Firewall policies in Azure Firewall Manager
AI is revolutionizing the world we live in—from the way we entertain ourselves, to the products and services that we consume, to the way we care for our bodies, and how we go about our daily work. Organizations are leveraging the power of AI to transform our lives by accelerating superior product innovations, increasing organization competitiveness no matter their size or available resources, and immersing us into more amazing, photo-realistic virtual worlds in movies and games.
Azure Container Apps is a managed serverless container service which offers an ideal platform for application developers who want to run microservices in containers without managing infrastructure.
Write code using your preferred programming language or framework and build microservices with full support for Distributed Application Runtime (Dapr). Scale dynamically based on HTTP traffic or events powered by Kubernetes Event-Driven Autoscaling (KEDA).
Container Apps is built on a foundation of powerful open-source technology. Behind the scenes, every container app runs on Azure Kubernetes Service, with KEDA, Dapr, and Envoy baked in. This lets you perform modern application lifecycle tasks such as application upgrades, traffic shifting, and versioning ready-to-run for teams of every skillset.
To learn more about Azure Container Apps, visit the getting started guide on Microsoft Docs.
The subnet per node pool feature allows for use of multiple subnets in the same virtual network within an AKS cluster by assigning new node pools to different subnets. This allows for expansion of cluster address space over time as cluster size increases.
Azure Bastion now supports connectivity to Azure virtual machines or on-premises resources via a specified IP address. When IP based connection feature is enabled, Azure Bastion can be used to RDP/SSH into an on-premises resource over ExpressRoute and Site-to-Site VPN.
Source: General availability: Azure Bastion IP based connection
Microsoft is announcing the general availability of new storage optimized Azure Virtual Machines. The new Lasv3 and Lsv3 VM series have been engineered to run workloads that require high throughput and high IOPS, including big data applications, SQL and NoSQL databases, distributed file systems, data analytics engines, and more.
The new VM series provide faster processors, increased networking, and higher remote disk throughput compared to prior generation storage optimized VMs. More specifically:
- The Lsv3 VM series is based on the 3rd Generation Intel® Xeon® Platinum 8370C (Ice Lake) processor in a hyper-threaded configuration.
- The Lasv3 VM series features the 3rd Generation AMD EPYC™ 7763v (Milan) processor in a multithreaded configuration.
Both Lsv3 and Lasv3 VMs provide high throughput, low latency, directly mapped local NVMe storage and one 1.92TB NVMe SSD per 8 vCPUs, with up to 19.2TB available on the largest instance.
Source: General availability: Storage optimized Azure VMs deliver higher performance for data analytics.
Host your Google Remote Procedure Call (gRPC) apps on App Service. Google Remote Procedure Call uses the HTTP/2 protocol to streamline messaging between clients and back-end servers, providing an efficient way to connect services that require high-performance communication.
Source: Public preview: App Service Google Remote Procedure Call support
Customizing your node configuration allows you to configure or tune your operating system (OS) settings or the kubelet parameters to match the needs of the workloads.
When you create an AKS cluster or add a node pool to your cluster, you can customize a subset of commonly used OS and kubelet settings. These customizations allow you to choose where you may want to change default values in situations where workloads have certain performance demands on the kubelet or OS.
Source: Generally available: Custom node configuration on AKS
Automate the creation and management of Azure Cost Management scheduled emails with the ScheduledActions API. You can already create scheduled emails from within cost analysis in the portal. The API now allows you to automate scheduling new email alerts or triggering one-time emails to support advanced scenarios.
Learn more about subscribing to cost alerts and start looking into automation via the ScheduledActions API to increase cost visibility throughout your team.
Source: Public preview: Automate scheduled emails of your saved cost views via API
Microsoft is committed to the responsible advancement of AI to enable every person and organization to achieve more. Over the last few months, we have talked about advancements in our Azure infrastructure, Azure Cognitive Services, and Azure Machine Learning to make Azure better at supporting the AI needs of all our customers, regardless of their scale. Meanwhile, we also work closely with some of the leading research organizations around the world to empower them to build great AI.
Today, we’re thrilled to announce an expansion of our ongoing collaboration with Meta: Meta has selected Azure as a strategic cloud provider to help accelerate AI research and development.
As part of this deeper relationship, Meta will expand its use of Azure’s supercomputing power to accelerate AI research and development for its Meta AI group. Meta will utilize a dedicated Azure cluster of 5400 GPUs using the latest virtual machine (VM) series in Azure (NDm A100 v4 series, featuring NVIDIA A100 Tensor Core 80GB GPUs) for some of their large-scale AI research workloads. In 2021, Meta began using Microsoft Azure Virtual Machines (NVIDIA A100 80GB GPUs) for some of its large-scale AI research after experiencing Azure’s impressive performance and scale. With four times the GPU-to-GPU bandwidth between virtual machines compared to other public cloud offerings, the Azure platform enables faster distributed AI training. Meta used this, for example, to train their recent OPT-175B language model. The NDm A100 v4 VM series on Azure also gives customers the flexibility to configure clusters of any size automatically and dynamically from a few GPUs to thousands, and the ability to pause and resume during experimentation. Now, the Meta AI team is expanding their usage and bringing more cutting-edge machine learning training workloads to Azure to help further advance their leading AI research.
In addition, Meta and Microsoft will collaborate to scale PyTorch adoption on Azure and accelerate developers' journey from experimentation to production. Azure provides a comprehensive top to bottom stack for PyTorch users with best-in-class hardware (NDv4s and Infiniband). In the coming months, Microsoft will build new PyTorch development accelerators to facilitate rapid implementation of PyTorch-based solutions on Azure. Microsoft will also continue providing enterprise-grade support for PyTorch to enable customers and partners to deploy PyTorch models in production on both cloud and edge.
“We are excited to deepen our collaboration with Azure to advance Meta’s AI research, innovation, and open-source efforts in a way that benefits more developers around the world,” Jerome Pesenti, Vice President of AI, Meta. “With Azure’s compute power and 1.6 TB/s of interconnect bandwidth per VM we are able to accelerate our ever-growing training demands to better accommodate larger and more innovative AI models. Additionally, we’re happy to work with Microsoft in extending our experience to their customers using PyTorch in their journey from research to production.”
By scaling Azure’s supercomputing power to train large AI models for the world’s leading research organizations, and by expanding tools and resources for open source collaboration and experimentation, we can help unlock new opportunities for developers and the broader tech community, and further our mission to empower every person and organization around the world.
MultiValue (MV) Traffic Manager profiles enable you to specify a set of IPv4 and IPv6 endpoints in the same profile. MultiValue profiles are often nested under other profiles and traffic is routed from parent profiles to MultiValue profiles only if a minimum number of endpoints are healthy. This threshold of the minimum number of healthy endpoints is specified by users through the minChild parameter of the MultiValue profile.
Until now, you could only specify an aggregate number of minChild parameters and could not distinguish between IPv4 and IPv6 endpoints. This worked well for dual-homed scenarios where the number of IPv4 endpoints was the same as the number of IPv6 endpoints. However, this is lacking when you have single stack IPv4-only and IPv6-only endpoints which may have different capacity and availability characteristics.
With these enhancements, you will now be able to specify minChild property separately for IPv4 and IPv6 endpoints, enabling them to account for capacity differences in these stacks. This will offer greater design flexibility while you are chalking out your IPv6 adoption strategy.
Source: General availability: Enhanced IPv6 functionality for MultiValue profiles in Azure Traffic Manager
Dynamic concurrency automatically determines optimal per trigger concurrency settings for your workloads and adjusts as your load patterns change over time. Using dynamic concurrency can provide the following benefits to your function apps:
- Increased throughput
- Simplified concurrency configuration
- Dynamic adjustments to changing load patterns
- Instance health protection
This feature currently supports Service Bus, Azure Blob, and Azure Queue triggers.
Learn more about the benefits of dynamic concurrency and how to optimize concurrency.
Source: Generally available: Dynamic concurrency in Azure Functions
Azure Synapse Link for SQL automates the extraction and movement of data from your relational operational data stores in both Azure SQL Database and SQL Server 2022 to Azure Synapse Analytics dedicated SQL pools.
Your data is replicated in near-real-time without the need to develop and deploy ETL or ELT pipelines. Once in Azure Synapse Analytics, the data can be used in advanced analytics and other downstream processing systems much faster than traditional batch-based ETL or ELT scenarios.
NGINX for Azure is a natively integrated software as a service (SaaS) solution with advanced traffic management and monitoring. The Azure integration enables ease of use with provisioning and configuration in a couple steps though the Azure portal.
Leverage advanced traffic management features, such as JSON Web Token (JWT) authentication and active health checks, with built-in security integrations like Azure Key Vault for SSL/TLS certificate management. You can purchase this solution through the Azure Marketplace, receive a unified bill for all services you use on Azure, and leverage existing enterprise agreements.
Source: Public preview: NGINX for Azure
Azure AI is introducing two updates in preview to Azure Cognitive Services to help you deploy high-quality models as APIs and infuse language capabilities into your apps more efficiently and responsibly:
Azure OpenAI Service, an Azure Cognitive Service, is now available in limited access preview. Approved customers will be able to access 25 different models from OpenAI, including the GPT-3 base series (Ada, Babbage, Curie and DaVinci), Codex series and embedding models, with the enterprise capabilities of Azure. Azure OpenAI Service will help you enable new reasoning and comprehension capabilities for building cutting-edge applications for use cases such as writing assistance, code generation, and making sense of unstructured data. With features like fine-tuning and built-in responsible AI, you can also tailor the model to your specific needs and detect and mitigate harmful use. Learn more.
Azure Cognitive Service for Language now offers summarization for documents and conversations, a new capability which helps you quickly surface key information in documents and contact center calls, such as reason for the call and resolution. Learn more.
The Azure Migrate tool now offers additional capabilities that make it easier for you to move applications from on-premises environments to Azure App Service and Azure Kubernetes Service.
Azure App Service bulk migration capabilities are now in public preview through the Azure Migrate feature:
- Discover and assess ASP.NET web apps in addition to categorizing which apps are ready for migration.
- Suggest a destination for migration and provide a guided content and configuration experience for ASP.NET web apps to Azure App Service.
- Discover and migrate with Java Tomcat applications to App Service Linux and to Azure Kubernetes Service.
- Containerize your ASP.NET web apps and move them to either Windows Containers on App Service or to Azure Kubernetes Service.
Source: Public preview: App Service new migration capabilities
Leverage a rich set of first party solutions on AKS using the cluster extension feature. This feature builds on top of the packaging components of Helm by providing an Azure Resource Manager driven experience for installation and lifecycle management of different Azure service capabilities on the Kubernetes cluster.
The cluster extensions can be enabled using Azure CLI and allows you to accelerate your deployments on AKS by leveraging a broad range of services.
AKS now supports Key Management System (KMS) plugin integration which enables encryption at the rest of your Kubernetes data in etcd using Azure Key Vault. You can now store secrets in bring your own key (BYOK) encrypted etcd using KMS.
From the Kubernetes documentation on Encrypting Secret Data at Rest:
KMS Plugin for Key Vault is the recommended choice for using a third-party tool for key management. KMS plugin simplifies key rotation, with a new data encryption key (DEK) generated for each encryption, and key encryption key (KEK) rotation controlled by the user.
Features:
- Use a key in Key Vault for etcd encryption
- Bring your own keys
- Provide encryption at rest for secrets stored in etcd
Trusted launch is a seamless way to improve the security of generation 2 VMs. It protects against advanced and persistent attack techniques by combining technologies which can be independently enabled like secure boot and virtualized version of trusted platform module (vTPM). Azure Backup is announcing general availability of trusted launch VMs backup in all Azure regions where trusted launch Azure Virtual Machines are available. You will be able to configure the backup of your trusted launch Azure Virtual Machines through enhanced policy and enable backup through recovery services blade, manage blade, and create VM blade.
Learn more about trusted launch VMs backup here.
Source: General availability: Azure Backup support for trusted launch Azure Virtual Machines
Computer Vision's OCR (Read) API 2022 model with 164 supported languages is now generally available as a cloud service and Docker container.
- Support for 164 languages including Russian, Arabic, Hindi and other languages using Cyrillic, Arabic, and Devanagari scripts.
- Support for 9 languages with English, Chinese Simplified, French, German, Italian, Japanese, Korean, Portuguese, and Spanish.
- Enhanced support for single characters, handwritten dates, amounts, names, other entities commonly found in receipts and invoices.
- Improved processing of digital PDF documents and Input file size limit increased to 500 MB.
- Performance and latency improvements.
- Available as cloud service and Docker container.
To learn more, get started with the new OCR features.
Source: Generally available: OCR supports 164 languages in the Cognitive Services Computer Vision
Stream Analytics now allows you to use managed identities as an authentication mode when connecting to Azure Cosmos DB and Azure Service Bus. You can use either System-Assigned Managed Identity or your own User-Assigned Managed Identity when authenticating. This solves a common challenge when building cloud applications related to credential management. Keeping the credentials secure is important and shouldn't be stored in developer workstations or checked into source control.
To learn more, visit:
- Connect to Azure Cosmos DB using Managed Identity
- Connect to Azure Service Bus using Managed Identity
Source: Public preview: Additional support for managed identity authentication in Azure Stream Analytics
The Open Service Mesh (OSM) extension is a managed service mesh for Arc-enabled Kubernetes clusters that is lightweight and extensible. It can be configured with Service Mesh Interface APIs, works by injecting envoy proxy as a sidecar to each application instance, and brings a new Azure Portal experience for onboarding. Open Service Mesh covers some of the core features of a service mesh including:
- mTLS traffic encryption between microservices
- Traffic splitting for canary and blue/green deployments
- Fine grained access control policies for microservices communicating over HTTP, TCP, and gRPC
- Observability for application performance
- Traffic control for ingress with various tools such as Contour
- Progressive delivery with Flagger
Source: Generally available: Open Service Mesh extension for Azure Arc
Azure Data Lake Storage Gen1 will be retired on 29 February 2024. We recommend you migrate your data lake to Azure Data Lake Storage Gen2 and take advantage of the capabilities dedicated to big data analytics, built on Azure Blob Storage. To lower the barrier for this migration, we are now offering a simple and intuitive user experience in the Azure portal. You can provide your consent in the Azure portal and migrate your data from Azure Data Lake Storage Gen1 to Azure Data Lake Storage Gen2.
Source: General availability: Azure Data Lake Storage Gen1 to Gen2 using Azure Portal
Azure Container Apps, a service for building and deploying modern applications and microservices using serverless containers, now provides live log streaming and the ability to connect to a containers console.
Log streaming is helpful when testing and diagnosing your container(s) in your container app. Being able to connect to the console of a running container enables you to execute shell (e.g., Bash or sh) commands as needed.
Source: Public preview: Azure Container Apps now support log streaming and console connect
Microsoft offers two types of Azure DNS Zones—private and public—for hosting your private DNS and public DNS records.
- Azure Private DNS: Azure Private DNS provides a reliable and secure DNS service for your virtual network. Azure Private DNS manages and resolves domain names in the virtual network without the need to configure a custom DNS solution. By using private DNS zones, you can use your own custom domain name instead of the Azure-provided names during deployment.
- Azure Public DNS: DNS domains in Azure DNS are hosted on Azure's global network of DNS name servers. Azure DNS uses anycast networking. Each DNS query is answered by the closest available DNS server to provide fast performance and high availability for your domain.
Source: Announcing Azure DNS Private Resolver: Now in preview
Azure Database for MySQL - Flexible Server is now running on the latest MySQL minor versions 8.0.28 and 5.7.37. The new MySQL minor versions include bug fixes in terms of partitioning, replication, and some additional new functionality. As part of your maintenance window, your servers will be automatically updated to this version.
The minor versions allow you to get the most out of your experience with Azure Database for MySQL – Flexible Server—along with running on the most stable, compliant, and secure MySQL community versions.
Source: Generally available: Minor versions upgrade for Azure Database for MySQL – Flexible Server
Trusted launch provides a seamless way to improve the security of Azure Generation 2 VMs. It protects against advanced and persistent attack techniques by combining technologies which can be independently enabled like secure boot and virtualized version of trusted platform module (vTPM). Now you can use Azure Compute Gallery to create and share images of trusted launch virtual machines.
Source: Generally available: Azure Compute Gallery support for trusted launch Virtual Machines
Big news for computer science teachers! Today, we invite teachers to join GitHub Global Campus, the new home for all computer science teachers at GitHub! On Global Campus, teachers can access education resources and learn about new programs and events-all in one place! Teachers can also:
- Upgrade their GitHub organizations to GitHub Team.
- Connect with the teacher community on GitHub Discussions.
- Request swag for their classroom.
- Manage active GitHub Classrooms.
If you’re a teacher, you can join Global Campus by completing a short application for teacher benefits. Once accepted, you will be officially welcomed as a Global Campus teacher.
Big news for computer science (CS) teachers. GitHub verified teachers using GitHub Classroom get access to GitHub’s groundbreaking, browser-based IDE, Codespaces. It’s a seismic shift for CS education, breaking down barriers in a fundamentally new way. Whether you’re a teacher frustrated with the complexities of managing local machine-based developer environments, tired of troubleshooting your students’ tools rather than focusing on their code, or looking to reduce technical and cost barriers for your CS Classroom, Codespaces addresses so many of the pain points in CS education with one elegant solution – integration in GitHub Classroom.
You can enable Codespaces in GitHub Classroom and then choose it as the preferred editor when creating assignments.
Azure Static Web Apps now supports seamless CI/CD integration with Azure DevOps via Microsoft Azure Portal. You can now opt for DevOps as your deployment source and link your DevOps account to populate the repository details with a single click.
Source: Public preview: Improved Azure DevOps support in Static Web Apps
Secure webhook is an updated version of IT Service Management Connector (ITSMC). Both versions allow you to create work items in an IT Service Manager (ITSM) tool when Azure Monitor sends alerts. The functionality includes metric, log, and activity log alerts.
IT Service Manager Connector uses username and password credentials. Secure webhook has stronger authentication because it uses Azure Active Directory (Azure AD). Azure AD is Microsoft's cloud-based identity and access management service. It helps users sign in and access internal or external resources. Using Azure AD with IT Service Manager helps to identify Azure alerts (through the Azure AD application ID) that were sent to the external system.
The first two integrations are with ServiceNow ITOM and BMC Helix.
Private endpoints for Azure Arc-enabled servers enable you to manage your Windows and Linux servers from Azure without sending network traffic over the public internet for enhanced security.
Servers can be configured to use a private endpoint by associating them with an Azure Arc Private Link Scope and connecting your on-premises network to an Azure virtual network using a site-to-site VPN or Express Route.
Source: Generally available: Azure Arc-enabled servers support for private endpoints
Join to celebrate the one-year anniversary of Azure Static Web Apps! Connect with others in the developer community and increase your Azure Static Web Apps skills in a fun, collaborative way.
It's hard to believe that it was just under a year ago that Microsoft announced the general availability of Azure Static Web Apps.
Azure Static Web Apps service became generally available in May 2021, with support for many of the popular front-end frameworks and static site generators used for modern web app development.
Sign up now for the Azure Static Web Apps anniversary event.
Source: Join us and the developer community to celebrate Azure Static Web Apps
Azure Event Grid’s Partner Events enables users to grant authorization to partners in order to create partner topics or partner destinations in their Azure subscription. You need to opt-in to use this feature prior to July 2022. Event Grid will start requiring authorizations to create partner topics or partner destinations around June 30th, 2022. At that point, any attempt from a partner to create a partner topic or partner destination will fail. This authorization model does not apply to custom topic, domains, or system topics.
Source: Public preview: Event Grid enables user authorization to create partner topics
Virtual Network NAT (VNet NAT) is a fully managed and highly resilient network address translation (NAT) service. With Virtual Network NAT, you can simplify your outbound connectivity for virtual networks without worrying about the risk of connectivity failures from port exhaustion or your internet routing configurations.
Support for Resource Health check with Virtual Network NAT helps you monitor the health of your NAT gateway as well as diagnose or troubleshoot outbound connectivity.
With Azure Resource Health, you can:
- View a personalized dashboard of the health of your NAT gateway
- Set up customizable resource health alerts to notify you in near real-time of when the health status of your NAT gateway changes
- See the current and past health history of your NAT gateway to help you mitigate issues
- Access technical support when you need help with Azure services, such as diagnosing and solving issues
Source: General availability: Virtual Network NAT health checks available via Resource Health
Object replication now supports premium block blobs to replicate your data from your blob container in one storage account to another anywhere in Azure. The destination storage account can be a premium block blob or a general-purpose v2 storage account.
You can also specify up to 1000 replication rules (increased from 10) for each replication policy for both general-purpose v2 and premium block blob storage accounts.
Object replication unblocks a set of common replication scenarios for block blobs:
- Minimize latency – have your users consume the data locally rather than issuing cross-region read requests.
- Increase efficiency – have your compute clusters process the same set of objects locally in different regions.
- Optimize data distribution – have your data consolidated in a single location for processing/analytics and then distribute only resulting dashboards to your offices worldwide.
- Optimizing costs – after your data has been replicated, you can reduce costs by moving it to the archive tier using life cycle management policies.
Source: General availability: Object replication on premium blob storage and rule limit increased
Node pool snapshots allow you to take a configuration snapshot of your node pool and then create new node pools or new clusters based off that snapshot, as long as that configuration and Kubernetes version is supported.
Object replication now supports premium block blobs to replicate your data from your blob container in one storage account to another anywhere in Azure. The destination storage account can be a premium block blob or a general-purpose v2 storage account.
You can also specify up to 1000 replication rules (increased from 10) for each replication policy for both general-purpose v2 and premium block blob storage accounts.
Object replication unblocks a set of common replication scenarios for block blobs:
- Minimize latency – have your users consume the data locally rather than issuing cross-region read requests.
- Increase efficiency – have your compute clusters process the same set of objects locally in different regions.
- Optimize data distribution – have your data consolidated in a single location for processing/analytics and then distribute only resulting dashboards to your offices worldwide.
- Optimizing costs – after your data has been replicated, you can reduce costs by moving it to the archive tier using life cycle management policies.
Source: General availability: Object replication on premium blob storage and rule limit increased
When a node is deallocated, the attached storage as well as the container image is still present on the node. When scaling up your deployments, all deallocated nodes will be started first before provisioning new nodes. This allows for faster operation speeds as your deployment leverages cached images. Scale-down mode allows you to no longer have to pre-provision nodes and pre-pull container images.
With the move of preview to GA, scale-down mode now supports spot node pools.
Azure Functions support for PowerShell 7.2 is now supported in public preview. This enables developing and deploying Azure Functions Apps for production scenarios using the latest version of PowerShell.
Source: Public preview: Azure Functions now supports PowerShell 7.2
Azure Web Application Firewall (WAF) is a cloud-native, self-managed security service that protects your applications and APIs running in Azure or anywhere else – from the network edge to the cloud. We offer two options – global WAF integrated with Azure Front Door and regional WAF integrated with Azure Application Gateway - for deploying Azure WAF for your applications and APIs.
On March 29, we announced the general availability of managed Default Rule Set 2.0 with anomaly scoring, Bot Manager 1.0, and security reports on global WAF. Today, we are excited to share the general availability of additional features on regional WAF. Take advantage of the latest Azure WAF enhancements that offer you better security, improved scale, easier deployment, and better management of your applications and APIs:
- Reduced false positives with Core Rule Set 3.2 integrated with Azure Application Gateway. The older CRS 2.2.9 ruleset is being phased out in favor of the newer rulesets.
- Improved performance and scale with the next generation of WAF engine, released with CRS 3.2
- Increased size limits on regional WAF for body inspection up to 2MB and file upload up to 4GB
- Advanced customization with per rule exclusion and attribute by names support on regional WAF
- Native consistent experience with WAF policy – new deployments of Application Gateway v2 WAF SKU now natively utilizes WAF policies instead of configuration
- Advanced analytics capabilities with new Azure Monitor metrics on regional WAF
Source: Generally available: Enhancements to Azure Web Application Firewall
Azure Bastion is a fully managed jumpbox-as-a-service that provides secure and seamless Remote Desktop Protocol (RDP) and Secure Shell Protocol (SSH) access to your VMs in local or peered virtual networks. Azure Bastion provides connectivity directly from the Azure portal using Transport Layer Security (TLS).
With Azure Bastion, your VMs do not need a public IP address, protecting your virtual machines from exposing RDP and SSH ports to threats on the public internet, while still providing secure access using RDP and SSH. With native client support available on the Standard SKU for Azure Bastion, you now unlock customizable features and added functionality in your VM sessions.
Source: Customize your secure VM session experience with native client support on Azure Bastion
With Static Web Apps, you can now configure Azure pipelines to deploy your application to preview environments. The Azure DevOps task for Azure Static Web Apps intelligently detects and builds your app’s frontend and API and deploys the entire application to Azure. You can fully automate the testing and delivery of your software in multiple stages all the way to production.
Azure Static Web Apps provides globally distributed content hosting and serverless APIs powered by Azure Functions. It also includes everything you need to run a full-stack web app, including support for custom domains, free SSL certificates, authentication/authorization, and preview environments.
Source: Public preview: Static Web Apps support for preview environments in Azure DevOps
Azure App Service now supports mounting Azure Files as a local share in Windows Code (in public preview). This complements existing file share support for Linux Containers and Windows Containers.
Enabling custom-mounted storage creates many opportunities for you to:
- Configure persistent storage for your App Service app and manage the storage separately.
- Make static content like video and images readily available for your App Service app.
- Write application log files or archive older application log to Azure File shares.
- Share content across multiple apps or with other Azure services.
Source: Public preview: Azure Storage as share in Windows Code in App Service
With the Azure Key Vault automated key rotation feature, now generally available, you can set a rotation policy on a key to schedule automated rotation and configure expiry notifications through Event Grid integration.
This feature enables end-to-end zero-touch key rotation for Azure services data encryption with customer-managed key (CMK) stored in Azure Key Vault.
Automated key rotation feature will be billed per scheduled rotation.
Source: Generally available: Automated key rotation in Azure Key Vault
Azure Lab Services offers classroom labs for higher education, K-12 institutions, and commercial organizations that don't want to use the on-premises hardware but rather want to harness the power of the cloud to host labs for students or users.
Microsoft is excited to announce major updates to Azure Lab Services including enhanced lab creation and improved backend reliability, access performance, extended virtual network support, easier labs administration via new roles, improved cost tracking via Azure Cost Management service, availability of PowerShell module, and .NET API SDK for advanced automation and customization, and integration with Canvas learning management system. Learn more about the new update and how to use it.
Along with making significant reliability enhancements to the backend, labs creation, and access performance improvements, this major update is bringing a whole slew of additional features for the IT departments and administrators, educators, and the students, who are the three key personas that use this service.
App Service has added Azure Portal support for configuring networking options regarding virtual networks and private endpoints. This capability (currently in public preview) allows you to use the Portal to ensure a secure configuration from the moment you create a new web app in App Service.
This capability is also available through the Azure CLI and ARM templates.
Source: Public preview: App Service - Configure networking in Azure Portal during app creation
Microsoft is announcing that Azure Purview is generally available as of September 28, 2021. You can now maximize the value of your on-premises, multicloud, and software as a service (SaaS) data with this unified data governance solution.
Easily create a unified map of your data assets and their relationships with automated data discovery and sensitive data classification, get insight into the location and movement of data across your hybrid landscape, and empower data consumers to find valuable data through a data catalog. Azure Purview also has turnkey integrations with Azure Synapse Analytics, SQL Server, Power BI, Azure SQL and more to automatically capture lineage relationships between data assets.
You can now rehydrate an archived blob by copying it to a different storage account, as long as the destination account is in the same region as the source account. Rehydration across storage accounts enables you to segregate your production data from your backup data, by maintaining them in separate accounts. Isolating archived data in a separate account can also help to mitigate costs from unintentional rehydration.
Source: Generally available: Rehydrate an archived blob to a different storage account
Virtual network integration and private endpoint support is now available in the Azure App Service App Service Basic pricing tier.
You can use VNet integration (outbound) to enable your apps to access resources in or through a virtual network, without granting inbound private access to your apps. You can use private endpoints (inbound) to allow clients located in your private network to securely access your apps over Private Link, eliminating exposure from the public internet.
This extends the robust security capabilities already available in other App Service pricing tiers to the Basic SKU, making it even easier to get started with Azure App Service.
Azure Container Apps, a service for building and deploying modern applications and microservices using serverless containers, now supports managed identities in public preview.
Managed identities provide an identity for applications to use when connecting to resources that support Azure Active Directory (Azure AD) authentication, such as Azure Key Vault and Azure SQL Database. When enabled, your container apps can connect to supported services without using secrets in connection strings. Both system- and user-assigned managed identity are supported.
Specify a service tag as the address prefix parameter in a user-defined route for your route table. You can choose from tags representing over 70 Microsoft and Azure services to simplify and consolidate route creation and maintenance. With this release, using service tags in routing scenarios for containers is also supported.
User-defined routes with service tags will update automatically to include any changes that services make to their list of IPs and endpoints. You will no longer need to manually update routes using the Service Tag and IP range data from the weekly downloadable JSON file.
Instead of creating several routes per route table to configure routing for multiple Microsoft and Azure services, each of which can contain dozens or hundreds of prefixes, one route with a service tag condenses all the ranges for that service. As a result, this feature can reduce the likelihood of hitting the routes-per-table limit of 400.
For example, the AzureCloud service tag includes more than 4,500 prefixes, which represent the Azure address space; one route containing the AzureCloud service tag will effectively route traffic intended for any of these AzureCloud prefixes through the desired next hop type.
This feature is available through Azure Portal, REST, PowerShell, CLI, and can be used in ARM templates.
Source: Generally available: Service tags support for user-defined routing
Today, Microsoft is announcing that Azure Managed Grafana is available in preview. With Azure Managed Grafana, the Grafana dashboards our customers are familiar with are now integrated seamlessly with the services and security of Azure.
The Grafana application lets users easily visualize all their telemetry data in a single user interface. With Grafana's extensible architecture, users can visualize and correlate multiple data sources across on-premises, Azure, and multi-cloud environments. Azure Managed Grafana particularly optimizes this experience for Azure-native data stores such as Azure Monitor and Data Explorer thus making it easy for customers to connect to any resource in their subscription and view all resulting telemetry in a familiar Grafana dashboard.
Source: Enhance your data visualizations with Azure Managed Grafana—now in preview
Visual Studio 17.2 Preview 3 introduces a brand-new All-In-One search experience that merges the existing VS Search (Ctrl + Q) and Go To (Ctrl + T) to allow you to search both your code and Visual Studio features quicker and easier than ever, all in the same place.
The All-In-One search streamlines your searching experience by providing you with a customizable UI (size, location, and dismissibility), compact search results with real-time matching as you type, and a fully keyboard friendly interface to ideally minimize your searching pain points.
Source: Introducing a New Way to Search Your Code and Visual Studio Features
Along with the announcement of Azure Managed Grafana, Microsoft is excited to introduce new Grafana integrations with Azure Monitor including the ability to pin Azure Monitor visualizations from Azure Portal to Grafana dashboards and new out-of-the-box Azure Monitor dashboards.
Full stack visibility from multiple sources in a single screen
Grafana allows you to query, visualize and create operational dashboards on Azure Monitor data. Using Azure Managed Grafana, you can now view your Azure monitoring data in Grafana dashboards in a few simple clicks. You can quickly pin Azure Monitor visualizations from the Azure Portal to new or existing Grafana dashboards by adding panels to your Grafana dashboard directly from Azure Monitor. Additionally, you can combine app and infrastructure metrics from multiple Azure sources into a single dashboard for full stack visibility.
When you deploy a site to Azure Static Web Apps, each pull request against your production branch will generate a preview deployment available at a temporary URL. Today, we’re announcing expanded support for preview deployments with stable URLs. This can be configured in the GitHub Actions workflow by enabling deployment from branches or by specifying a deployment environment name.
To deploy non-production branches to a preview environment, it is required to update the GitHub workflow to run when a push is made to the specific branches and define the production_branch property in the build_and_deploy_job configuration.
Alternatively, you can push changes to a named preview environment by configuring a deployment_environment property in the workflow.
Source: Public preview: Stable URLs for preview environments in Azure Static Web Apps
Continuous cost optimization can take place at all stages of an Azure workload’s lifecycle, but your Azure subscription provides a very effective benefit to further optimize your investment when you are ready to deploy that workload.
For cloud workloads with consistent resource usage, you can buy reserved instances at a significant discount and reduce your workload costs by up to 72 percent compared to pay-as-you-go prices. Azure Reservations can be obtained by committing to one-year or three-year plans for virtual machines, Azure Blob storage or Azure Data Lake Storage Gen2, SQL Database compute capacity, Azure Cosmos DB throughput, and other Azure resources.
Source: Optimize your cloud investment with Azure Reservations
Microsoft is pleased to announce that the next generation of NC A100 v4 series is now available for preview. These virtual machines (VMs) come equipped with NVIDIA A100 80GB Tensor Core PCIe GPUs and 3rd Gen AMD EPYC™ Milan processors. These new offerings improve the performance and cost-effectiveness of a variety of GPU performance-bound real-world AI training and inferencing workloads. These workloads cover object detection, video processing, image classification, speech recognition, recommender, autonomous driving reinforcement learning, oil and gas reservoir simulation, finance document parsing, web inferencing, and more.
Figure 1: ResNet50 results were generated using NC24s_v3 and NC96ads_A100_v4 virtual machine sizes.
Source: Accelerate your AI applications with Azure NC A100 v4 virtual machines
Security Overview at the organization level is now out of beta and generally available. GitHub Advanced Security customers can use Security Overview to view a repo-centric view of application security risks. They can also see an alert-centric view of all Code Scanning, Dependabot, and Secret Scanning alerts, across all repositories in an organization.
Microsoft Azure is a cloud platform integrated with data services, advanced analytics, and developer tools and services. When you build on, or migrate IT assets to Azure, we provide a secure, consistent application platform to run your workloads. To strengthen your security posture, we rolled out DNS reservations to prevent subdomain takeover in Cloud Services deployments. Subdomain takeovers enable malicious actors to redirect traffic intended for an organization’s domain to a site performing malicious activity.
The risks of subdomain takeover include:
- Loss of control over the content of the subdomain
- Cookie harvesting from unsuspecting visitors
- Phishing campaigns
- Further risks of classic attacks such as XSS, CSRF, CORS bypass
Ensuring that your organization has implemented processes to prevent dangling DNS entries and the resulting subdomain takeovers is a crucial part of your security program.
Please refer to the DNS reservation feature in Cloud Services to reclaim your subdomain here: Prevent subdomain takeovers
Source: Generally available: DNS reservations to prevent subdomain takeover in Cloud Services deployments
Private endpoints enable clients on an Azure virtual network to securely access Azure Static Web Apps through an IP address in the virtual network's address space over a private link. This enables network traffic between the virtual network and the Static Web Apps service to traverse over the Microsoft backbone, eliminating exposure from the public internet.
To learn more about Azure Static Web Apps, visit: https://docs.microsoft.com/azure/static-web-apps/overview
Source: Generally available: Azure Static Web Apps support for private endpoints
Your new and existing general purpose provisioned and serverless Azure SQL Database elastic pools allow for zone redundant configuration. This feature utilizes Azure Availability Zones to replicate databases across multiple physical locations within an Azure region. By selecting zone redundancy, you can make your databases and elastic pools resilient to a much larger set of failures, including catastrophic datacenter outages—without any changes of the application logic.
Source: General availability: Zone redundancy for Azure SQL Database general purpose tier
The latest release of Apache Kafka 2.4 includes:
- MirrorMaker 2 availability
- New metric category AtMinIsr topic partition
- Improved broker start-up time by lazy on demand mmap of index files
- More consumer metrics to observe user poll behavior
Source: Generally available: Apache Kafka 2.4 in Azure HDinsight
The latest release of Apache Spark 3.1 includes:
- Adaptive query execution
- Convert sort merge join to broadcast hash join
- Spark catalyst optimizer
- Dynamic partition pruning
- Create new Spark 3.1 clusters (not Spark 3.0 clusters (preview))
For additional details, review the document Apache Spark 3.1 on Microsoft Tech Community.
For a complete list of improvements, review the Apache Spark 3.1 release notes.
For more details on migration, review the migration guide.
Azure Automation diagnostic logs allows you to send runbook job status and job streams to the Log Analytics workspace. This data can be queried with the powerful KQL query language to gain deep insights across patterns, correlations, and more.
Today, we are announcing the ability to send audit data for Automation accounts to Azure Monitor Log Analytics workspace. This allows enterprises to monitor key Automation account activities for security and compliance. When enabled through the Azure Diagnostics mechanism, you will be able to collect telemetry about create, update, and delete operations for the Automation runbooks and Automation assets. This includes connection, credential, variable, and certificate. This telemetry, as with any other Azure Diagnostics-based telemetry, can be sent to an Azure Storage Blob, Azure Event Hub, or into Azure Monitor logs.
Source: Generally available: Diagnostic audit logs for Automation accounts
Note: Azure AD Graph will not retire on 30 June 2022 per announcement below. We are extending the retirement date for Azure AD Graph. A follow up announcement will be published before 31 December 2022 with more information on additional tools to assist you with your migration and an updated retirement date.
Azure AD Graph will continue to be supported but will not be receiving any new feature updates as we are investing our engineering resources in Microsoft Graph. We encourage you to update your apps to use Microsoft Graph as soon as possible. Please view details below to migrate to Microsoft Graph.
The latest release of Apache Kafka 2.4 includes:
- MirrorMaker 2 availability
- New metric category AtMinIsr topic partition
- Improved broker start-up time by lazy on demand mmap of index files
- More consumer metrics to observe user poll behavior
Source: Generally available: Apache Kafka 2.4 in Azure HDinsight
The latest release of Apache Spark 3.1 includes:
- Adaptive query execution
- Convert sort merge join to broadcast hash join
- Spark catalyst optimizer
- Dynamic partition pruning
- Create new Spark 3.1 clusters (not Spark 3.0 clusters (preview))
Source: Generally available: Apache Spark 3.1.2 in Azure HDinsight
Note: Azure AD Graph will not retire on 30 June 2022 per announcement . We are extending the retirement date for Azure AD Graph. A follow up announcement will be published before 31 December 2022 with more information on additional tools to assist you with your migration and an updated retirement date.
Azure AD Graph will continue to be supported but will not be receiving any new feature updates as we are investing our engineering resources in Microsoft Graph. We encourage you to update your apps to use Microsoft Graph as soon as possible. Please view details below to migrate to Microsoft Graph.
Azure Automation diagnostic logs allows you to send runbook job status and job streams to the Log Analytics workspace. This data can be queried with the powerful KQL query language to gain deep insights across patterns, correlations, and more.
Today, we are announcing the ability to send audit data for Automation accounts to Azure Monitor Log Analytics workspace. This allows enterprises to monitor key Automation account activities for security and compliance. When enabled through the Azure Diagnostics mechanism, you will be able to collect telemetry about create, update, and delete operations for the Automation runbooks and Automation assets. This includes connection, credential, variable, and certificate. This telemetry, as with any other Azure Diagnostics-based telemetry, can be sent to an Azure Storage Blob, Azure Event Hub, or into Azure Monitor logs.
Source: Generally available: Diagnostic audit logs for Automation accounts
With the new Azure Bastion native client support, available with Standard SKU, you can now:
- Connect to your target Azure virtual machine via Azure Bastion using Azure CLI and a native client on your local machine
- Log into Azure Active Directory-joined virtual machines using your Azure Active Directory credentials
- Access the features available with your chosen native client (ex: file transfer)
Source: General availability: Azure Bastion native client support
Azure Bastion support for Kerberos authentication, available with both basic and standard SKUs, is now in public preview. To learn more about the Kerberos authentication protocol and how to use it for VMs accessed via Azure Bastion, see the following resources below:
- Kerberos Authentication Overview | Microsoft Docs
- Configure Bastion for Kerberos authentication: Azure portal - Azure Bastion | Microsoft Docs
Source: Public preview: Azure Bastion support for Kerberos authentication
With Visual Studio 2022, Microsoft has converted the CPU Usage tool in the Performance Profiler to the profiler’s new analysis engine. This new change provides the tool with better source resolution, incremental/cancelable symbol loading, a performance boost, and a new flame graph.
Note: This is only available in the Performance Profiler (Alt+F2) version of the tool, but we are still working on supporting it in the Diagnostic Tools. Give it a shot and see what insights you can find!
Flame Graph
We have finally shipped our most requested feature, a flame graph, to visualize a call tree. This new view is in the CPU tool details tool window, above the source line highlighting view. Using the graph, you can get a visual overview of where time is being spent in your application and click on specific nodes to dig into them further. Stay tuned for a follow-up blog where I walk through a recent investigation I did with the tool to double the performance.
You can now create private endpoints to limit and secure device connectivity to your Azure IoT Central application with Private Link. This not only improves your security posture, but also simplifies your network architecture.
Devices running on connected or peered virtual networks, on-premises environments securely connected to Azure using ExpressRoute or VPN can now connect and enable bi-directional communication with Azure IoT Central via private endpoint.
Private endpoints use private IP addresses from a virtual network address space to connect your devices privately to your Azure IoT Central application. Network traffic between devices on the virtual network and the Azure IoT platform traverses the virtual network and a private link on the Microsoft backbone network, eliminating exposure on the public internet.
Auto-healing is a heavily used diagnostic feature of Azure App Service that allows end-users to configure a rich set of triggers that can be used to mitigate an app once it starts misbehaving. It not only allows you to mitigate the app from a bad situation but it also allows customers to capture diagnostic data that helps them debug the issues later.
Crash Monitoring and Proactive Crash Monitoring allow end-users to effectively diagnose and debug application crashes (process exits due to unhandled exceptions) easily.
One of the most asked features for both these features was the ability to view historical information about when these tools were triggered and what conditions cause them to trigger. Customers have also asked us to be able to view this information for a longer duration as by default the views available in Diagnose and Solve blade show you a maximum of 24 hours of information.
The new memory optimized Ebs v5 and Ebds v5 Azure Virtual Machines, now generally available, feature the latest 3rd Gen Intel Xeon Platinum 8370C (Ice Lake) processor in a hyper-threaded configuration. These VMs deliver up to 300% increase in VM-to-Disk Storage throughput and IOPS compared to the previous generation D/Ev4 VM series. The new VM series feature sizes from 2 to 64 vCPUs with and without local temporary storage best match your workload requirements.
These new VMs offer up to 120,000 IOPS and 4,000 MB/s of remote disk storage throughput. The increased storage throughput is ideal for the most demanding data-intensive workloads, including large relational databases such as SQL Server, high-performance OLTP scenarios, and high-end data analytics applications. You can also consolidate existing workloads on fewer VMs or deploy smaller VM sizes while achieving potential cost savings.
Source: Generally available: Azure Virtual Machines increase storage throughput by up to 300%
On-demand capacity reservations for Azure Virtual Machines let you deploy and manage the compute capacity required to run Azure Virtual Machines separately from the virtual machines (VMs) themselves. This new feature enables your IT organization to reserve compute capacity for a VM size. The reservation can be for any length of time in any public Azure region or availability zone and supports most VM series. You can create and cancel an on-demand capacity reservation at any time, no commitment is required.
The ability for you to access compute capacity–with SLA guarantees–ahead of actual VM deployments is particularly important to ensure the availability of business-critical applications running on Azure. On-demand capacity reservations can be combined with Azure Reserved VM Instances (RIs) to significantly reduce costs.
Source: General availability: On-demand capacity reservations
Generally available: On-demand capacity reservation with Azure Site Recovery safeguards VMs failover
Azure Site Recovery is now integrated with on-demand capacity reservation and is available generally. With this integration, you can leverage the power of capacity reservations with Site Recovery to reserve compute capacity in the disaster recovery (DR) region and guarantee your failovers. When you assign a capacity reservation group (CRG) for your protected VMs, Site Recovery will failover the VMs to that CRG. Additionally, a compute SLA gets added to the existing Site Recovery’s Recovery Time Objective (RTO) SLA of 2 hours.
For new VMs, you can create and assign a CRG while enabling replication with a single click. If you want to assign a CRG for your existing protected VMs, review the example in the screenshot below to navigate to the "Compute" blade and select the desired CRG. Assigning a CRG does not impact the Site Recovery License fee. For more information about the pricing of on-demand capacity reservation, refer the on-demand capacity reservations documentation.
Source: Generally available: On-demand capacity reservation with Azure Site Recovery safeguards VMs failover
Today Microsoft is announcing the general availability of Azure Spot Virtual Machines (VMs). Azure Spot VMs provide access to unused Azure compute capacity at deep discounts. Spot pricing is available on single VMs in addition to VM scale sets (VMSS). This enables you to deploy a broader variety of workloads on Azure while enjoying access to discounted pricing compared to pay-as-you-go rates. Spot VMs offer the same characteristics as a pay-as-you-go virtual machine, the differences being pricing and evictions. Spot VMs can be evicted at any time if Azure needs capacity.
Source: Announcing the general availability of Azure Spot Virtual Machines
When planning a potential migration of on-premises infrastructure to Azure, you may want to retain your existing public IP addresses due to your customers' dependencies or established IP reputation. Today, we are announcing the general availability of the ability to BYOIP (Bring Your Own IPs) to Azure. Public IP ranges can be onboarded to Azure as regional Custom IP Prefix resources, where they can be utilized in the same manner as Azure-owned public IP prefixes.
Source: General availability: Bring your own IP ranges to Azure
Azure Dedicated Host is a service that provides physical servers - able to host one or more virtual machines - dedicated to one Azure subscription. Dedicated hosts are the same physical servers used in our data centers, provided as a resource.
You can provision dedicated hosts within a region, availability zone, and fault domain. Then, you can place AKS VMs directly into your provisioned hosts, in whatever configuration best meets your needs.
Using Azure Dedicated Hosts for nodes with your AKS cluster enables:
- Hardware isolation at the physical server level. No other VMs will be placed on your hosts.
- Control over maintenance events initiated by the Azure platform. With dedicated hosts, you can opt-in to a maintenance window to reduce the impact to your service.
On 31March 2025, QnA Maker will be retired. Before that date, you’ll need to migrate your QnA Maker knowledge bases to custom question answering, a feature of Azure Cognitive Service for Language. Custom question answering provides all the capabilities of QnA Maker, plus enhancements such as:
- Improved relevance ranking.
- Availability across 31 regions.
- The ability to add and query unstructured content from documents and public URLs.
Beginning 1 October 2022, you won’t be able to create new QnA Maker resources or knowledge bases. All QnA Maker resources and knowledge bases created before that date will be supported until 31 March 2025.
With Azure Stack Hub’s 2108 update, you can preview Azure Container Registry on Azure Stack Hub. This service uses private container registries on Azure Stack Hub to store and retrieve OCI-compliant images to support both connected and disconnected scenarios for Azure Kubernetes Service (AKS), AKS engine, and other container orchestrator engines.
Source: Public preview: Azure Container Registry on Azure Stack Hub
Azure Front Door: The modern enterprise CDN
Every company is now a technology company challenged with managing a rapidly growing digital footprint, dispersed workforce, and evolving security threats. As a result, enterprises are looking for solutions that help meet the rising demands for better scalability, more security, higher performance, greater automation, and easier manageability—with reduced costs.
Whether you’re delivering content and files or building global apps and APIs, Azure Front Door can help you deliver higher availability, lower latency, better scale, and more secure experiences to your users wherever they are. Azure Front Door also enables you to define, manage, and monitor the global routing for your app.
Source: Introducing the new Azure Front Door: Reimagined for modern apps and content
You can now use Data Box to copy data directly to Archive tier blobs in Azure Storage. Indicate your intent to move data to Archive tier while ordering Data Box in the Azure portal. After Data Box arrives and you access its local UI, you can copy to the Block Blob (Archive) share shown under your storage account name. You can also copy to Archive tier using Data Box's data copy service.
Source: Generally available: Copy data directly to Archive Storage with Data Box
On 31 March 2025, Microsoft will retire the public preview templates functionality in the Azure portal. Before that date, you’ll need to start using template specs, which includes all the functionality of templates, plus enables you to:
- Securely store, share, and manage access to template specs in Azure Resource Manager.
- Iterate on template code to update an existing version or publish a new one.
- Deploy using PowerShell, Azure CLI, the Azure portal, REST, and other supported SDKs and clients.
Required action
To avoid losing access to your templates, follow the steps to convert them to template specs in the Azure portal before 31 March 2025.
Source: Templates functionality preview version in Azure portal will be retired on 31 March 2025
On 31 March 2023, Microsoft will be retiring support for Azure SDK libraries which do not conform to the Azure SDK guidelines. The new Azure SDK libraries are updated regularly to drive consistent experiences and strengthen your security posture. Please transition to the new Azure SDK libraries to take advantage of the new capabilities and critical security updates before 31 March 2023.
With Azure Stack Hub’s 2108 update, you can preview Azure Kubernetes Service on Azure Stack Hub. The same service that’s currently found in Azure is available in Azure Stack Hub. Manage Kubernetes clusters in the same way you currently do in Azure and utilize a familiar user experience, CLI, and API.
Source: Public preview: Azure Kubernetes Service on Azure Stack Hub
All Azure HBv3 virtual machine (VM) deployments from 21 March 2022 will include AMD EPYC 3rd Gen processors with 3D V-Cache, codenamed “Milan-X”. The enhanced HBv3 VMs are available in theAzure East US, South Central US, and West Europe regions. All VM deployments from today onward will occur on machines featuring Milan-X processors. Existing HBv3 VMs deployed prior to today’s launch will continue to see AMD EPYC 3rd Gen processors, codenamed “Milan”, until they are de-allocated and you create a new VM in its place.
HBv3-series VMs retain their existing pricing and do not require changes to your workloads. No other changes are being made to the HBv3-series VM sizes you already know and rely on for your critical research and business workloads. For more information on the Azure HBv3-series, please see official documentation for the Azure HBv3-series of Virtual Machines.
Microsoft announced the GA release of maintenance windows for Azure SQL Database and Azure SQL Managed Instance. Need for additional control and transparency into monthly maintenance events have been a continued feedback from customers of Azure SQL Database and Managed Instance. With the GA release of maintenance windows, you can choose from predefined time slots for maintenance in addition to having ability to set up alerts to be notified of upcoming maintenance events.
Azure Private Link support in Azure API Management is now in preview. With this, incoming traffic to Azure API Management's gateway can be secured to clients running in a virtual network through Azure Private Link. This will limit access to Azure API Management by assigning a virtual network private IP address to the Azure API Management gateway using Azure Private Link. Previously, only Developer and Premium tiers supported this integration with a virtual network. With this update, you can now integrate to clients in a virtual network privately, using the tiers- Developer, Basic, Standard, and Premium.
Source: Public preview: Azure Private Link support in Azure API Management | Azure updates | Microsoft Azure
It’s now been 25 years since the first release of Visual Studio in 1997 and such a big milestone deserves a proper celebration. The Visual Studio 25th Anniversary Event kicks off at 9 AM Pacific Time on Thursday, March 17, with exclusive content and exciting reveals all day long.
Source: Happy 25th birthday Visual Studio! - Visual Studio Blog (microsoft.com)
In addition to saving your analysis queries, now you can continually monitor the data by pinning it as a tile on a dashboard. To pin an analytics tile, you will need to save the analysis query first. While pinning, you will get the option to select the desired dashboard. After pinning, you can update the size, location, and title of the tile by editing the dashboard.
Microsoft partners with NVIDIA to bring GPU-accelerated confidential computing to Azure
Today, Microsoft are excited to announce the next chapter in this journey as NVIDIA and Microsoft are combining the power of GPU-accelerated computing with confidential computing for state-of-the-art AI workloads. This collaboration is the first step towards a shared vision to empower individuals and organizations to share and collaborate to derive new insights from data using GPU-accelerated computing without sacrificing security or privacy. With support for Ampere Protected Memory (APM) in NVIDIA A100 Tensor Core GPUs and hardware-protected VMs, enterprises will be able to use sensitive datasets to train and deploy more accurate models with state-of-the-art performance and an added layer of security that their data remain protected.
On 3 December 2022, extended support for Microsoft .NET Core 3.1 will end. After that date, your applications that are hosted on App Service will continue to run and your existing workloads will not be impacted. However, we'll no longer provide patches or customer service for .NET Core 3.1.
Update your App Service applications to use .NET 6, which is the latest version with long-term support and provides these enhancements:
- A unified set of base libraries and an SDK that make it easy to share code across any application type.
- Simplified development with new C# 10 features and minimal APIs.
- Hot reload that allows you to make code changes without explicit recompiling.
Recommended action
To avoid potential service disruptions or security vulnerabilities, follow the steps to update your App Service applications to use .NET 6 before 3 December 2022.
Today, Microsoft take a giant step toward making the dream of interoperability in healthcare real. Microsoft is announcing the general availability of Azure Health Data Services, a platform as a service (PaaS) offering designed exclusively to support Protected Health Information (PHI) in the cloud. Azure Health Data Services is a new way of working with unified data—providing your team with a platform to support both transactional and analytical workloads from the same data store and enabling cloud computing to transform how we develop and deliver AI across the healthcare ecosystem.
Import-Export overview
With Azure SQL Import-Export users can import a SQL Server database into Azure SQL Database using a BACPAC file or export from an Azure SQL Database into a BACPAC file. BACPAC files can be stored in Azure Blob storage(standard storage only) or local storage in an on-premises location. Importing a database into Azure SQL DB using Import-Export creates the database and imports schema and data into the database from the BACPAC file provided. Here is an overview of Import Export works:
To successfully run Import Export operations in Azure SQL Database, users must set “Allow Access to Azure Services” parameter under Firewall settings to ON. Otherwise, the Import Export operations fail with errors. But in many scenarios users would not want to give such a broad privilege for Import/Export operations and require a more precise and controlled way to perform the operation.
Import Export using Private Link now in Preview - Microsoft Tech Community
Azure Private Link is a service that enables you to access Azure resources (like Azure Event Hubs, Azure Storage, and Azure Cosmos DB) and Azure-hosted customer and partner services over a private endpoint in your Azure Virtual Network (VNet). With this general availability, you can now use private endpoint for Azure Digital Twins instances to allow clients in the virtual network (VNet) to securely access Azure Digital Twins instances over Azure Private Link. This feature allows you to further secure Azure Digital Twins instances by restricting traffic to the instances.
Manage approvals for business terms or self-service data access requests for your entire data estate. Azure Purview workflows empower you to achieve create, update, and delete validations and approvals using repeatable business processes with more control and less effort. You will not need to use manual controls such as emails or worksheets to review and approve the changes in your Azure Purview account.
Public preview: Azure Purview workflows | Azure updates | Microsoft Azure
Azure Database for MySQL—Flexible Server is now available as a deployment option in the US Gov Virginia region. You can now:
- Optimize lower total cost of ownership (TCO) with burstable SKU
- Access the stop/start feature
- Experience better resiliency with zone redundant high availability
- Increase control with scheduled maintenance
- Utilize enterprise security with virtual network isolation and data encryption
- Experience the openness of the MySQL database community version
- Bring your own keys to encrypt data at rest
Azure Chaos Studio now has faults available for Azure Key Vault and Classic Cloud Services. The Key Vault Deny Access fault blocks all network access to a Key Vault by temporarily modifying the Key Vault network rules, preventing an application dependent on the Key Vault from accessing secrets, keys, and/or certificates. The Classic Cloud Services Shutdown fault stops a deployment, simulating a service failure. Fault details are available in the fault library and these faults can be used in experiments created via Azure Resource Manager template or REST API. Adding these faults to an experiment using the experiment designer in the Azure portal will be available in the coming weeks.
Trusted launch is a seamless way to improve the security of generation 2 VMs. It protects against advanced and persistent attack techniques by combining technologies that can be independently enabled like secure boot and virtualized version of trusted platform module (vTPM). Today, we are announcing public preview of Trusted Launch support for VMs using Ephemeral OS disks.
Stay informed about changes to your cost in Azure Cost Management and Billing with scheduled emails. From cost analysis, select a private or shared chart view, click the subscribe command to manage all emails for this view, then click +add to configure a new email alert. You can subscribe to daily, weekly, or monthly updates and can even share those views with people outside the portal.
Learn more about how to subscribe to cost alerts and configure daily alerts for your costs today in cost analysis.
Public preview: Schedule automated emails of your saved cost views | Azure updates | Microsoft Azure
Azure Site Recovery is now integrated with on-demand capacity reservation and available in public preview. With this integration, you can leverage the power of capacity reservations with Site Recovery to reserve compute capacity in the disaster recovery (DR) region and guarantee your failovers. When you assign a capacity reservation group (CRG) for your protected VMs, Site Recovery will failover the VMs to that CRG. Additionally, when on-demand capacity reservation reaches general availability, a compute SLA gets added to the existing Site Recovery’s Recovery Time Objective (RTO) SLA of 2 hours.
For new VMs, you can create and assign a CRG enabling replication. If you want to assign a CRG for your existing protected VMs, review the example in the screenshot below to navigate to the "Compute" blade and select the desired CRG. Assigning a CRG does not impact the Site Recovery License fee. For more information about the pricing of on-demand capacity reservation, refer the on-demand capacity reservations documentation.
Now in preview, new Azure SQL Hyperscale databases can enable the zone redundant configuration. The zone redundant configuration utilizes Azure Availability Zones to replicate databases across multiple physical locations within an Azure region. By selecting zone redundancy, you can make all layers of your Hyperscale databases resilient to a much larger set of failures, including catastrophic datacenter outages, without any changes of the application logic. For more information see Hyperscale zone redundant availability.
Zone Redundancy for Azure SQL Database Hyperscale tier in preview - Microsoft Tech Community
Azure IoT Central is an IoT application platform that reduces the burden and cost of developing, managing, and maintaining enterprise-grade IoT solutions. Azure IoT Central provides a ready-to-use UX and API surface built to connect, manage, and operate fleets of devices at scale.
Azure IoT Central is now generally available in the South Central US and Canada Central azure regions. For more information, please visit Azure IoT Central homepage and see the Azure Regional Availability site for complete regional availability information.
As an Azure Purview data catalog grows in size, it becomes important for data consumers to understand what assets they can trust. Data consumers must know if an asset meet their organization's quality standards and can be regarded as reliable. Azure Purview allows data stewards to manually endorse assets to indicate that they're ready to use across an organization or business unit.
When searching or browsing the data catalog, you'll see a certification label on any asset that it's certified. Certified assets will also be boosted in search results, helping data consumers discover them easily.
When developing web apps, it’s common to use the browser developer tools to perform various tasks like; modifying the CSS, inspecting network traffic, etc. Because the browser is disconnected from the IDE, if you make changes to the running application in the browser, you will need to remember and reapply those changes to your code as well. To make you more productive, we have partnered with the Edge Developer Tools team to start integrating their developer tools into Visual Studio for ASP.NET Core, and ASP.NET, developers. You can download and install the preview extension at https://aka.ms/edgetools-for-vs. In the current Preview release we have enabled the both the Elements and Network tools. Below is an animated gif showing you the Elements tool in action.
Edge Developer Tools for Visual Studio (Preview) - Visual Studio Blog (microsoft.com)
Data virtualization capabilities, now in preview in Azure SQL Managed Instance, enable you to execute Transact-SQL (T-SQL) queries against data from files stored in Azure Data Lake Storage Gen2 or Azure Blob Storage and combine it with relational data stored locally in the managed instance using logical joins. This way you can transparently access external data while keeping it in its original format and location. There is no data duplication or need to run and maintain ETL processes, which means that you can extract and deliver insights faster. Currently supported file formats are Parquet, CSV, and JSON.
Announcing Data virtualization with Azure SQL Managed Instance – preview - Microsoft Tech Community
To protect your snapshots against accidental deletion, Azure Backup has added one more level of security to the Azure file shares snapshot management solution by integrating with the Azure Files platform capability of acquiring a lease on the snapshots. The lease operation creates and manages a lock on the snapshots for delete operations. After taking a snapshot, Azure Backup takes an infinite lease on it. This lease protects the snapshot from accidental deletion. To ensure that a snapshot does not get deleted during a restore operation, Azure Backup also checks the lease status at the beginning of the restore, and in case it is found to be non-leased, it acquires a lease on the snapshot.
Application consistent snapshot tool (AzAcSnap) v5.1 is a command-line tool enables you to simplify data protection for third-party databases (SAP HANA) in Linux environments (for example, SUSE and RHEL).
The public preview of application consistent snapshot tool v5.1 supports the following new capabilities:
- Oracle Database support
- Backint Co-existence
- RunBefore and RunAfter capability
These new features can be used with Azure NetApp Files, Azure BareMetal, and now, Azure Managed Disk.
Azure Application Gateway is announcing general availability for transport layer security (TLS) mutual authentication. Mutual authentication allows for two-way TLS certificate-based authentication, which allows both client and server to verify each other's identity. This release strengthens your zero trust networking posture and enables many connected devices, IoT, business to business, and API security scenarios.
You can upload multiple client certificate authority (CA) certificate chains on the Application Gateway to use for client authentication. You can also choose to enable frontend mutual authentication at a per-listener level on Application Gateway. We are also adding enhancements to server variables supported on Application Gateway to enable you to pass additional client certificate information to backend as HTTP headers.
With this release we are also extending support for listener specific TLS policies which allows you to configure predefined or custom TLS policies at a per listener granularity, instead of global TLS policies.
With Azure for Operators, we’re empowering operators to unlock the power of 5G by bringing cloud and edge closer together to modernize their networks so that they can streamline and optimize their business operations and deliver new services faster with greater reach and lower cost. With solutions that run on-premises, at the edge, or in the cloud but are always managed and secured by Azure, Microsoft meets you where you are, offering flexibility to transform on your terms and timelines. We are committed to partnering with you, not competing against you. Your consumer, enterprise, and government customers will benefit from a cloud platform with industry-leading security and governance built-in, and with an unmatched partner and developer ecosystem to maximize the value of the cloud at the edge. We’re applying Microsoft technology and developer ecosystem capabilities to offer the next-generation Azure for Operators portfolio—carrier-grade hybrid cloud platform, voice core, mobile core, and multi-access edge compute.
Azure Static Web Apps allow configuration of various settings such as routing, authentication, and networking via the staticwebapp.config.json file. You can now specify an API language runtime via the same configuration file.
You can specify an API runtime version in your app’s staticwebapp.config.json configuration file as shown below:
{
"platform": {
"apiRuntime": "node:16"
}
}
You can now create a branch directly from an issue to begin development work that's correlated to that issue. Branches connected to an issue are shown under the "Development" section, which has replaced "Linked pull requests", in the sidebar of an issue. When you create a pull request for one of these branches, it is automatically linked to the issue.
The Azure Cosmos DB API for MongoDB version 4.2 includes new aggregation functionality and improved security features such as client-side field encryption. These features help you accelerate development by leveraging the new functionality instead of developing it yourself. The Azure Cosmos DB API for MongoDB 4.2 can be enabled in the Azure Portal with any new or existing database account in seconds, with zero downtime.
Azure NetApp Files is now available in the following additional region:
- Australia Central 2
- Additionally, cross-region replication has been enabled between Australia Central and Australia Central 2 region pair.
For the most current regional availability updates, please see the Azure product regional availability page.
For the most current list of cross-region replication pairs, please see the Supported cross-region replication pairs page.
Low recovery point objective (RPO) is a key requirement for Azure Files holding business-critical data. Azure Backup enables you to achieve recovery point objective for up to four hours using Azure Files snapshot-based backup solution. You can leverage the multiple backups per day feature to create or modify a backup policy to take multiple snapshots of your file share. This feature allows you to define a backup schedule aligning to your working hours when there are frequent updates to your Azure Files content.
In addition to the preview capability that allowed you to configure multiple backups from the Azure portal, you can now also use Powershell or Azure CLI to create a backup policy that triggers multiple snapshots a day as per your defined schedule.
The capability to set specific retention on AzureActivity and Usage data tables in Log Analytics workspaces is now in general availability. Keep AzureActivity and Usage data for longer periods of time, while maintaining the workspace retention as low as needed. Previously, AzureActivity and Usage were treated differently–they had a minimum of 90 days retention and couldn’t be set with specific retention as other tables which forced you to increase the workspace retention.
The minimum retention for AzureActivity and Usage remains 90 days to enable basic audit on operations and usability troubleshooting.
The Azure Purview UX team has localized Azure Purview studio in a variety of languages. You can go to settings on the top bar and select one of 18 languages to use. All user experiences that are generally available will be localized to the selected language.
General availability: Localization available in Azure Purview | Azure updates | Microsoft Azure
You can now create virtual machine restore points in any region of your choice regardless of the region where your virtual machine is deployed. Protect your Azure workloads by easily copying virtual machine restore points from one region to another region.
Read more about cross region virtual machine restore points on our blog and learn how to create and copy virtual machine restore points across regions by reviewing our public documentation.
Public preview: Cross region virtual machine restore points | Azure updates | Microsoft Azure
Automatically delete disks, NICs and Public IPs associated with a VM at the same time you delete the VM. With this feature, you can specify the associated resources that should be automatically deleted when you delete a VM. This will allow you to save time and simplify the VM management process.
To learn more about this feature and to get started, read our documentation.
We are excited to announce the general availability of Log Analytics data export, a capability that lets you continuously export ingested data for selected tables in your Log Analytics workspace, and sent it to an Azure storage account, or Azure Event Hubs.
How it works?
Data export is designed for scale and can support Terabytes of logs per day for each of your workspaces. Data export flow relies on destination resources that you own and manage, and you must assure sufficient ingress capacity for proper export operation, and prevent failures. See 'Scale considerations' for details.
Azure Monitor Log Analytics data export is generally available! - Microsoft Tech Community
Today, we’re announcing that the ability to prebuild codespaces is entering public beta. Prebuilding a codespace enables fast environment creation times, regardless of the size or complexity of your repositories. A prebuilt codespace will serve as a ‘ready-to-go’ template where your source code, editor extensions, project dependencies, commands, and configurations have already been downloaded, installed, and applied so that you don’t have to wait for these tasks to finish each time you create a new codespace.
Codespaces prebuilds now available in public beta | GitHub Changelog
Cost Management anomaly detection is now available for subscriptions in the cost analysis preview. To check cost anomalies for your subscription, open any view in the cost analysis preview and click the see insights link to view all insights and details.
If this is your first time using the cost analysis preview, you'll see a "check back tomorrow for cost anomaly insights" message confirming that you've been setup for anomaly detection. If you're already setup, then you'll either see a "no anomalies" message or a list of any anomalies that have been detected within the date range you're looking at. To get more details about the anomaly, click the insight link to view daily cost over the date range that was evaluated.
You can patch and install updates to your Windows Server virtual machines on Azure without requiring a reboot using hotpatch. This capability is available exclusively as part of Azure Automanage for Windows Server for Windows Server Azure Edition core virtual machines, and comes with the following benefits:
- Lower workload impact with less reboots
- Faster deployment of updates as the packages are smaller, install faster, and have easier patch orchestration with Azure Update Manager
- Better protection, as the hotpatch update packages are scoped to Windows security updates that install faster without rebooting
Generally available: Hotpatch for Windows Server virtual machines | Azure updates | Microsoft Azure
You can now apply tags to an Azure Kubernetes Service (AKS) cluster and its related resources using the Azure Resource Manager, the Azure CLI, and Azure PowerShell. For some resources, you can also use Kubernetes manifests to set Azure tags. Azure tags are useful for tracking resource usage for things like charge back.
General availability: Azure tags support in AKS | Azure updates | Microsoft Azure
AKS support for Kubernetes release 1.21 is now in public preview. Kubernetes 1.21 delivers a total of 50 enhancements in various stages of maturity, including 19 completely new capabilities. This release include capabilities such as a new memory manager and a more flexible scheduler.
Public preview: Kubernetes 1.21 support in AKS | Azure-Updates | Microsoft Azure
Alert processing rules (formerly action rules) provide post-processing capabilities for fired alerts in Azure Monitor, such as scheduled suppression and at-scale actions management. Following the updated public preview from December 2021, this feature is now generally available.
As part of the generally available announcement, we will be retiring the existing preview APIs of alert processing rules / action rules in June 2022, so update your environments accordingly. This includes ARM templates / PowerShell / CLI etc. We will also start to enforce a per subscription quota on the rules (1000 rules per subscription). See the limits document for more details.
Action required: Update your environments such as ARM templates / PowerShell / CLI etc. as soon as possible, as we will be retiring the existing preview APIs of alert processing rules / action rules in June 2022.
Generally available: Alert processing rules in Azure Monitor | Azure updates | Microsoft Azure
Predictive autoscale uses machine learning to help manage and scale Azure virtual machine scale sets with cyclical workload patterns. It forecasts overall CPU load to your virtual machine scale set, based on your historical CPU usage patterns. By observing and learning from historical usage, it predicts the overall CPU load ensuring scale-out occurs in time to meet demand.
Query across your subscriptions and tenants to discover changes to your resources with Azure Resource Graph. Resource configuration changes enable you to:
- Find when changes were detected on an Azure Resource Manager property
- See property change details for each resource change
- Query changes at scale across your subscriptions, management group, or tenants
At scale and on by default
This public preview iterates on the previous Resource Changes API with an entirely new pipeline that stores changes as extension resources at change time, enabling you to query changes to your Azure resources at scale through Resource Graph. In addition, this support includes the ability to craft charts and pin results to Azure dashboards based on specific change queries.
At-scale
Resource changes can be queried with Resource Graph, which supports querying at the resource, resource group, subscription, management group, and tenant scopes. With one query you can get details about all of the deleted, created, and/or modified resources in your environment over the past seven days.
On by default
No onboarding is required. This is a platform feature enabled by default and available at no additional cost.
Public preview: Resource configuration changes | Azure updates | Microsoft Azure
Virtual Machine level disk bursting supports M-series, Msv2-series Medium Memory, and Mdsv2-series Medium Memory VM families allowing your virtual machine to burst its disk IO and throughput performance for a short time, daily. This enables VMs to handle unforeseen spiky disk traffic smoothly and process batched jobs with speed. There is no additional cost associated with this new capability or adjustments on the VM pricing and it comes enabled by default.
Some example scenarios where bursting can be applied:
- Improve boot times: With your virtual machine and your disks both being able to burst and coming fully stocked with bursting credits at the start, your instance will be able to boot at a much faster rate than before.
- Handle batch jobs: Some application workloads are cyclical in nature, requiring a baseline performance for the majority of the time but a higher performance for a short period of time. For instance, an accounting program that processes daily transactions requiring a small amount of disk traffic but then monthly end reports which need a higher amount of disk traffic.
- Prepares for trafficspikes: Web servers and their applications can get a surge of traffic from unforeseen circumstances. With bursting virtual machines and disks backing the web servers, the web servers will handle traffic spikes smoothly and improve their customer’s experience by reducing load times under heavy stress.
Find guidence and support with updated documentation including new FAQ articles, guides for each phase of the solution development process, and a reorganized landing page and table of contents. The new FAQ articles include:
- Why should I start with Azure IoT Central?
- What’s the difference between aPaaS and PaaS offerings?
- How do I move between aPaaS and PaaS solution approach?
- How do I extend Azure IoT Central if it’s missing something I need?
- What are Azure IoT Central’s scale limits?
To get started, see the new documentation landing page.
If your IoT Central solution has a large number of devices, it can sometimes be difficult to find the device you are looking for simply scrolling through the device explorer. For quick access, you have always had the ability to search for devices using the search bar but what was returned was a simple list of results.
With this update, the search results experience has been redesigned allowing you to filter your results by different search fields such as device name, device id, property values, and cloud property values. We have also added bold text for matched terms (highlights) so you can understand why exactly a device showed up in the results.
Explore the latest search experience using the tips above.
Today Microsoft is announcing the Azure File Migration Program which gives customers and partners in the Solution Integrator and Service Provider ecosystem, access to industry-leading file migration solutions from Komprise and Data Dynamics—at no cost. These solutions help easily, safely, and securely migrate file and object data to Azure Storage.
Azure Migrate offers a very powerful set of no-cost (or low-cost) tools to help you migrate virtual machines, websites, databases, and virtual desktops for critical applications. You can modernize legacy applications by migrating them from servers to containers and build a cloud native environment. This new program complements Azure Migrate and provides the means to migrate applications and workloads that include large volumes of unstructured file data.
Migrating your files to Azure has never been easier | Azure Blog and Updates | Microsoft Azure
Azure Sphere OS version 22.02 is now available for evaluation in the Retail Eval feed. The retail evaluation period provides 2 weeks for backwards compatibility testing. During this time, please verify that your applications and devices operate properly with this release before it is deployed broadly via the Retail feed. The Retail feed will continue to deliver OS version 21.10 until we publish 22.02.
The evaluation release of version 22.02 includes an OS update only; it does not include an updated SDK. When 22.02 is generally available later in February, an updated SDK will be included.
Flash, as the project is internally known, is a collection of efforts across Azure Engineering, that aims to evolve Azure’s virtual machine (VM) availability monitoring ecosystem into a centralized, holistic, and intelligible solution customers can rely on to meet their specific observability needs. Today, we’re excited to announce the completion of the project’s first two milestones—the preview of VM availability data in Azure Resource Graph, and the private preview of a VM availability metric in Azure Monitor.
What is Project Flash?
Project Flash derives its name from our commitment to building robust and rapid ways to monitor virtual machine (VM) availability as comprehensively as possible—a key prerequisite for efficient application performance. It’s our mission to ensure you can:
- Consume accurate and actionable data on VM availability disruptions (for example, VM reboots and restarts, application freezes due to network driver updates, and 30-second host OS updates), along with precise failure details (for example, platform versus user-initiated, reboot versus freeze, planned versus unplanned).
- Analyze and alert on trends in VM availability for quick debugging and month-over-month reporting.
- Periodically monitor data at scale and build custom dashboards to stay updated on the latest availability states of all resources.
- Receive automated root cause analyses (RCAs) detailing impacted VMs, downtime cause and duration, consequent fixes, and similar—all to enable targeted investigations and post-mortem analyses.
- Receive instantaneous notifications on critical changes in VM availability to quickly trigger remediation actions and prevent end-user impact.
- Dynamically tailor and automate platform recovery policies, based on ever-changing workload sensitivities and failover needs.
You can now upload images to Wiki pages. Drag and drop, select or paste the file.
Computer Vision's OCR (Read) API expands supported languages to 164 with its latest preview:
- OCR support for print text expands to 42 new languages including Arabic, Hindi and other languages using Arabic and Devanagari scripts.
- OCR support for handwritten text expands to Japanese and Korean in addition to English, Chinese Simplified, French, German, Italian, Portuguese, and Spanish.
- Enhancements include improved support for extracting handwritten dates, amounts, names, and single character boxes.
- General performance and AI quality improvements.
See the OCR how-to guide to learn how to use the new preview features.
Simplify your monitoring and troubleshooting of Azure IoT Edge devices with deep integration with Azure Monitor through a set of built-in metrics, the IoT Edge Metrics Collector module, and a set of curated visualizations. With this integration, you can
- Analyze the efficiency of your solution
- Choose hardware to fit the performance demands on your devices
- Monitor locked down assets
- Unify cloud and edge monitoring
- Proactively identify issues with metrics-based alerts
- Rapidly troubleshoot problems
- Create custom metrics and dashboards
The latest IoT Edge metrics collector module release 1.0.3 is now available in the Microsoft container registry at mcr.microsoft.com/azureiotedge-metrics-collector:1.0.3.
General Availability: IoT Edge monitoring with Azure Monitor | Azure updates | Microsoft Azure
When deploying your SQL Server on Azure Virtual Machines using Azure Marketplace images, you can configure storage directly from the SQL Server for Azure Virtual Machine blade in the Azure portal. This is restricted to allowing an increase in the space for data and log storage pools but with the ability to configure tempdb.
- Perform common DBA tasks directly from the SQL VM blade such as adding data files of equal size and acting when the file sizes are not equal.
- Increase storage space using tempdb configuration blade when using on a remote disk.
General availability: Enhanced storage configuration with tempdb | Azure updates | Microsoft Azure
Azure Backup service is announcing the private preview of AKS persistent volume backup. With this release, you can backup and restore the persistent volumes of your Azure Kubernetes Service (AKS) cluster.
Benefits includes
- Recovery from data corruption or deletion of persistent volumes
- Clone or replicate persistent volumes to dev/test environments
Using this feature, you can
- configure backup for the persistent volumes of stateful applications deployed on the AKS cluster
- restore back one or more persistent volumes on to the same or different cluster
Use this feature to configure data protection for the stateful application deployed as Kubernetes workloads (namely Deployment, Statefulset) that saves application data in one or more persistent volumes.
Private preview: AKS cluster persistent volume backup | Azure updates | Microsoft Azure
Azure Communication Services has added support for Telephony Direct Offers in public preview for both Denmark and the UK. This means that both partners and you in Denmark and UK can purchase Toll-Free and Geographic phone numbers in their countries, helping them to build engaging communication experiences to connect to telephony (PSTN) users worldwide.
Learn more about pricing and quickstart template.
You now have more control over when your self-hosted runners perform software updates. If you specify the --disableupdate flag to the runner then it will not try to perform an automatic software update if a newer version of the runner is available. This allows you to update the self-hosted runner on your own schedule and is especially convenient if your self-hosted runner is in a container.
For compatibility with the GitHub Actions service, you will need to manually update your runner within 30 days of a new runner version being available. For instructions on how to install the latest runner version, please see the installation instructions for the latest release in the runner repo.
GitHub Actions: Self-hosted runners can now disable automatic updates | GitHub Changelog
The dependency graph now supports detecting GitHub Actions workflow YAML files. These will be displayed within the dependency graph section in the Insights tab. Repositories that publish actions will also be able to see the number of repositories that depend on that action from the Used By control on the repository homepage.
Dependency graph adds support for GitHub Actions | GitHub Changelog
Azure Site Recovery provides replication policies which govern retention history of recovery points during replication. Based on the replication policy applied while enabling replication, recovery points are retained, and app-consistent snapshots are captured.
With the roll out of support for longer retention of recovery points, you can now retain recovery points up to 15 days instead of 72 hours. Recovery points will be retained at a frequency of 5 mins for the first 2 hours. Subsequently, recovery points will be pruned and stored at a lesser frequency. You can enter any value from 0-15 (in days) to configure retention period for a replication policy and once used during replication, recovery points will be retained accordingly for that duration. In addition to this, you can enable the application-consistent recovery points if required. By default, this is disabled.
This provides enhanced protection as you have the flexibility of more recovery points. For instance, you can use older recovery points to recover in case recent recovery points are affected due to an incident, such as ransomware, that was undetected for a few days.
Scope: Azure to Azure, VMware to Azure, Physical to Azure disaster recovery scenarios.
With the new Azure Bastion native client support in public preview and included in Standard SKU, you can now:
- Use either SSH or RDP to upload files to a VM from your local computer.
- Use RDP to download files from a VM to your local computer.
Azure Functions support for PowerShell on Linux OS is now generally available in Azure Functions runtime 4.0 on all hosting plans. You can now develop Azure Functions PowerShell apps locally and deploy them to Azure Functions on Linux OS.
Generally available: PowerShell on Linux OS in Azure Functions | Azure updates | Microsoft Azure
Automate queries to your Log Analytics workspaces and Application Insights components to list or visualize results with Azure Monitor Logs connector. The connector 'time range' property can be set to either ‘set in query’, when the time filter appears in the query, or with a relative value (last hour, last 12 hours, etc.). Improve investigation utilizing an ‘exact’ time range to enable scenarios like diagnostics of alert incidents.
You can collect and send logs for Azure Storage to Azure Monitor log analytics workspaces, Azure Event Hubs, Azure Storage, and select Marketplace partners.
The pricing model for diagnostic settings is in effect for Azure Storage logs. Sending logs to Azure Storage, Azure Event Hubs, or Marketplace partners will incur a charge per GB sent by diagnostic settings and independently of any costs charged by the destination.
Read the Azure Monitor pricing page under Platform Logs to learn more about the pricing model and Azure Storage documentation to learn more details about the announcement. Note: Changes to the Portal UX and documentation to remove "preview" designation for this feature will follow over the next few weeks.
Opt-in to new feature updates, security improvements, and bug fixes in the Azure Monitor agent (AMA). These have been rolled out automatically across your virtual machines for new and existing agent installations. Attend to important updates and security fixes by enabling the automatic extension upgrade feature.
The new opt-in experience is available for Azure virtual machines and scale sets on both Windows and Linux. Review the migration guidance to start migrating from Log Analytics agents to the new agent.
You can now create Azure Container Apps environments into new or existing virtual networks. This enables Container Apps to receive private IP addresses, maintain outbound internet connectivity, and communicate privately with other resources on the same virtual network.
You can use Anomaly Detector’s multivariate detection synchronously with simple operations without the need to upload data to blob storage for inference. Put the data in the API request body and get the detection result in real-time. Detection results include additional information to help you deep dive into the root cause of an anomaly, giving you the most contributed variables and their related variables. Learn more on how to use Anomaly Detector on multiple variables for your time series data.
Microsoft’s Zero Trust Framework protects assets anywhere by adhering to three principles:
- Verify explicitly: Always authenticate and authorize based on all available data points, including user identity, location, device health, service or workload, data classification, and anomalies.
- Use least privileged access: Limit user access with just-in-time and just-enough-access (JIT and JEA), risk-based adaptive policies, and data protection to help secure both data and productivity.
- Assume breach: Minimize blast radius and segment access. Verify end-to-end encryption and use analytics to get visibility, drive threat detection, and improve defenses.
Enabling Zero Trust with Azure network security services | Azure Blog and Updates | Microsoft Azure
To ensure customers running on Azure are protected against ransomware attacks, Microsoft has invested heavily in Azure security and has provided customers with the security controls needed to protect their Azure cloud workloads.
Azure Firewall Premium comes into help with its intrusion detection and prevention system (IDPS) capability, every packet will be inspected thoroughly, including all its headers and payload to identify malicious activity and to prevent it from penetrating your network. IDPS allows you to monitor your network for malicious activity, log information about this activity, report it, and optionally attempt to block it.
A comprehensive overview of best practices and recommendations can be found in the "Azure Defenses for Ransomware Attack" e-book.
Azure Backup has recently released the below changes to the security features setting for the workloads protected via Microsoft Azure Recovery Service Agent, Azure Backup Server, or System Center Data Protection Manager.
Integration with MUA (Multi-user authorization)
The operation to “disable security features” is now defined as a critical operation that can be protected by a Resource Guard. Learn more
Unregistration blocked for protected servers with backup items in active or soft delete state
To provide protection against accidental or malicious deletion, a protected server cannot be unregistered if the security features are enabled for the vault and there are associated backups items in active or soft delete state.
Free retention of backup data in soft delete state
Customers will incur no cost for the backup data retained in the soft delete state.
No data loss if backups are retained in soft delete state
The backup policy is not enforced on the data retained in the soft delete state, and hence no data is deleted for 14 days.
At Ignite 2021, Microsoft launched the Zone Redundant Storage (ZRS) option for Azure managed disks. ZRS managed disks provide synchronous replication of data across zones in any given region, enabling disks to tolerate zonal failures. This means that if a virtual machine becomes unavailable in an affected zone, you can continue to work with the disk by mounting it to a virtual machine in a different zone.
However, zonal resiliency is insufficient in the event of regional outages. Thus, Azure Site Recovery (ASR) now supports ZRS managed disks. With ASR, you can protect your VMs that leverage ZRS managed disks by replicating them to a secondary region of your choice. ASR identifies the source disks to be ZRS managed disks and creates equivalent ZRS managed disks in the secondary region. If there is a regional outage and you are required to failover to the secondary region, the VM(s) that ASR will spin up for you in the secondary region will have ZRS managed disks attached to them, ensuring the same, high level of zonal resiliency that you want.
New Azure Maps features historical weather, air quality and tropical storms.
Develop weather and climatology enabled solutions using the historical weather, air quality and tropical storms features from Azure Maps Weather Services.
Azure Maps Weather Services has added three new features, historical weather, air quality and tropical storms. Like the other Azure Maps Weather Services, the data in these new features come from worldwide leading weather services provider, AccuWeather. Here are the specifics on what these new features include:
Historical weather provides actuals, normals and records climatology data by day, for a specified date range, up to 31 days in a single API request. Historical data may be available as far back as 5 to 40+ years and includes, temperatures, precipitation, snowfall, snow depth and cooling/heating degree day information, depending on the location and service.
Air quality provides detailed information about the current and forecasted concentration of air pollutants and air quality. Forecasted information is available by hour (upcoming 1, 12, 24, 48, 72, and 96 hours) and by day (upcoming 1 to 7 days). Information includes, pollution levels, air quality index values, the dominant pollutant, and a brief statement summarizing risk level and suggested precautions.
Tropical storms provides information on government-issued active tropical storms, government-issued forecasted tropical storms, the locations of an individual government-issued tropical storm and the ability to search government-issued tropical storms by year, basin ID, and government ID. Tropical storms are also known as, hurricanes, cyclones, and typhoons, depending on the region of the world.
To get started with Azure Maps and the Azure Maps Weather Services, please go to the Azure Maps documentation and create an Azure Maps account for free if you don’t already have one.
To show you the latest capabilities of using Linux and Azure—and share some exciting announcements—we will be hosting Azure Open Source Day on Tuesday, February 15, 2022, from 9:00 AM to 10:30 AM Pacific Time.
Push your apps and data to the next level by using Azure, open-source, and Linux together. Join this free digital event to learn how to natively run your open-source workloads on Azure, expand their capabilities, and innovate in new ways using Azure services.
At this event, you’ll learn how Microsoft is committed to open source and works with the open-source community to develop new technologies. Hear about the latest trends and capabilities of using Linux and Azure together—direct from Microsoft insiders. Whether you’re new to Azure or are already using it, you’ll discover how to turbocharge your apps and data with open source and hybrid cloud technologies.
Here are seven reasons to attend the event
- Get the inside scoop on CBL-Mariner, the Linux distribution built by Microsoft to host Azure open-source services.
- Find out how to better automate and manage Linux investments on Azure using Azure Hybrid Benefit and Project Bicep.
- Discover tools for every developer, including Visual Studio Code, GitHub Codespaces, and Azure managed database and AI services.
- Learn about application modernization best practices using containers and Azure Kubernetes Service (AKS).
- Hear from Microsoft insiders and Linux industry leaders like Red Hat and SUSE.
- Ask the experts your questions during the live chat Q and A.
- Plus, be among the first to hear Microsoft CEO, Satya Nadella, share a special announcement on the 30th anniversary for Linux.
Source: 7 reasons to attend Azure Open Source Day | Azure Blog and Updates | Microsoft Azure
We are happy to announce the availability of the public preview of the App Service Environment (ASE) v3 migration feature. With this feature, you’ll be able to migrate your existing ASE as well as the apps running on that ASE to ASEv3. ASEv3 provides a number of feature differences as well as performance enhancements and potential reduced overall costs compared to previous versions. To get a complete overview on ASEv3, read the ASEv3 focused App Service Environment overview.
Check out the following docs to learn more about migrating to ASEv3:
Source: App Service Environment v3 Migration Feature Public Preview - Azure App Service
Azure ultra disks offer high throughput, high IOPS, and consistent low latency disk storage for your stateful applications. One major benefit of ultra disks is the ability to dynamically change the performance of the SSD along with your workloads without the need to restart your agent nodes. Ultra disks are suited for data-intensive workloads.
Source: General availability: Ultra disks support on AKS | Azure updates | Microsoft Azure
Azure Pipelines Microsoft-hosted agents have supported windows-2022 since September 2021. We've listened to your feedback that helped us improve the windows-2022 image and are ready to have Windows Server 2022 as the default version for the windows-latest image.
Azure Pipelines
With the subscription wide limit and per vault limit doubled, i.e. for secret GET and RSA 2,048-bit software keys, you'll receive 4,000 GET transactions per 10 seconds vs 2,000 per 10 seconds previously. The service quotas are specific to operation type and the entire list can be accessed in Azure Key Vault Service Limits. You can also view your Key Vault's usage on the 'Overview' page in the Azure portal on the "Monitoring" tab.
Learn more about Monitor Key Vault with Key Vault insights and monitoring metrics for Azure Key Vault.
There is no manual step required for increased service limits and this is by default applicable on all vaults without any additional cost.
A new version of the K2Bridge connector (Kibana-Kusto/Azure Data Explorer free connector) now supports dashboards and visualizations, in addition to the Discover tab which was supported previously.
With Kibana's Visualize tab users can create visualizations like: Vertical bar, Area chart, Pie chart, Gauge, Data table, Heat map, Goal chart, and Metric chart. After creating visualizations, users can use them to build dashboards. Additionally, we upgraded the connector's Kibana to version 7.10.2 to improve the user experience and provide better filtering support for Kusto's dynamic data type.
To learn more about Elasticsearch to Azure Data Explorer migration, visit this blog post.
To install and learn more about K2Bridge, visit the documentation or the GitHub repository.
Log alerts are one of the alert types that are supported in Azure alerts. Log alerts enable you to use a Log Analytics query to evaluate resources logs in every set frequency, and fire an alert based on the results. Rules can trigger one or more actions using action groups. Log alerts with one-minute frequency, the alert query will be evaluated every minute to check the condition, reducing the overall time to fire of a log alert.
Learn more here.
You can now code, build, deploy, simulate and debug your IoT Edge solutions in Visual Studio 2022.
- New Azure IoT Edge project targeting different platforms (Linux amd64, Linux arm32v7, Linux arm64v8, Windows amd64)
- Add a new IoT Edge module (C#/C) to solution and now includes support of .NET 6 for C# module
- Edit, build and debug IoT Edge modules locally on your Visual Studio machine
- Build and push docker images of IoT Edge modules
- Run IoT Edge modules in a local or remote simulator
- Manage IoT Edge devices and modules in IoT Hub
Download the Visual Studio installer
Learn more about develop and debug edge modules with Visual Studio
As part of the application and cluster lifecycle, you can now upgrade to the latest available version of Kubernetes and take advantage of new features. These new events enable you to more easily view the upgrade status in the Azure portal or via the CLI.
Azure Cache for Redis now supports authenticating storage account connections using managed identity. Identity is established through Azure Active Directory, and both system-assigned and user-assigned identities are supported. This further allows the service to establish trusted access to storage for uses including data persistence and importing/exporting cache data.
Containerd is an industry-standard container runtime. Using containerd enhances pod creation speed as well as stability. Azure Kubernetes Services (AKS) now supports containerd for Windows server containers. This is available for Kubernetes version 1.20 and higher.
With the general availability of Windows containerd support in AKS, Windows customer now have the ability to run production workloads on containerd. This also means that from Kubernetes 1.23 containerd will be the only support runtime for Windows workloads, as it is on Linux.
Site performance is crucial when creating applications on the modern web. It has a direct impact on user experience, search engine rankings, and user conversion rates. With Azure Static Web Apps, we're committed to building a platform that helps you deliver the best results for your users at a global scale. It provides streamlined full-stack development and hosting across static content and serverless APIs to power high productivity from source code to global high availability.
Today, we are announcing the preview of the Azure Static Web Apps enterprise-grade edge powered by Azure Front Door which enables faster page loads, enhanced security, and increased reliability for your global apps with no configuration or additional code required.
As part of our commitment to delivering the best possible value for Azure confidential computing, we're announcing a price reduction on the DCsv2 and DCsv3-series VMs by up to 33%. The price reduction enables the data protection benefits of ACC with no premium compared to general-purpose VMs on a per physical core basis.
New prices took effect on 1/1/2022. If you are already using DCsv2 and DCsv3-series VMs prior to 1/1/2022, you will see the price reduction in your next bill.
Please visit Azure pricing page for more details and learn more about Azure confidential computing
You can now upgrade your Azure Load Balancer from Basic SKU to Standard SKU by using a PowerShell script. By upgrading to Standard SKU, the Load Balancer enables the network layer traffic to drive higher performance and stronger resiliency, along with an improved integration experience with other Azure services. The PowerShell script creates the Standard SKU Load Balancer with the same configurations as the Basic Load Balancer. In additon, the script migrates the backend resources to the Standard Load Balancer for you.
Learn more about the process to upgrade Azure Load Balancer.
Learn more about the differences between two SKUs.
Learn more about Standard Load Balancer pricing.
Use Azure Static Web Apps enterprise-grade edge (public preview) to increase your website page load speed, enhance security, and optimize reliability for your global applications. It combines the capabilities of Azure Static Web Apps, Azure Front Door and Azure Content Delivery Network (CDN) standard into a single secure cloud CDN platform.
Key features included with Azure Static Web Apps enterprise-grade edge:
- Global presence in 118+ edge locations
- Proactive protection against Distributed Denial of Service (DDoS) attacks
- Native support of end-to-end IPv6 connectivity and HTTP/2 protocol
We started 2021 with great hopes of putting the global pandemic behind us. While it's happening much slower than any of us may have wanted, we're getting there. Yet, while we evolve and learn new ways to work, the need to manage and reduce cost continues to grow. With that in mind, 2021 was more focused on platform capabilities in Azure Cost Management and Billing and the underlying commerce platform at Microsoft. You saw many improvements, but there are even more changes behind the scenes that are extending the foundation for many great things to come.
Azure Cost Management and Billing 2021 year in review | Azure Blog and Updates | Microsoft Azure
Based on customer feedback, we have increased the limit of devices that can be shown on a single tile on and Azure IoT Central Dashboard from 10 to 100. This change makes it easier to visualize and analyze data across a larger device group simultaneously.
Learn more about creating and managing dashboards in Azure IoT Central.
Azure Ultra Disk Storage is now available in West US 3. Azure Ultra Disks offer high throughput, high IOPS, and consistent low latency disk storage for Azure virtual machines (VMs). Ultra Disks are suited for data-intensive workloads such as SAP HANA, top tier databases, and transaction-heavy workloads.
Semantic Search, a feature of Azure Cognitive Search, has entered ungated public preview. You can now turn on Semantic Search features directly from the Azure portal. We are also releasing the following updates:
- Billing for semantic search is now available. Customers can select between Free and Standard plans. See our pricing page for more details.
- We have expanded semantic search availability to the following regions: Australia East, East US, East US 2, North Central US, South Central US, West US, West US 2, North Europe, UK South, West Europe
- Customers can also leverage Semantic Configurations– a new feature within Semantic Search that allows customers to indicate title, description, and keyword fields as part of index definitions. This will help optimize search relevance by indicating the relative importance of certain fields
Public preview: Semantic Search update | Azure updates | Microsoft Azure
Microsoft is helping to reshape the automotive industry in the way it serves its drivers with in-vehicle infotainment systems. As an example, Azure is partnering with XPENG to enable AI voice experiences for automotive brands and customers.
The solution provides the industry with a fresh take on text-to-speech and expressive voice, global languages, speaker fidelity, and self-service customization. XPENG joins a growing trend of automakers rethinking investments in environmental voice.
“This is a cutting-edge exploration of vehicle voice interaction in the auto industry,” XPENG automotive AI product senior expert Hao Chao said. “The experience delivers a whole new level of natural speech. With a deep understanding of urban mobility, we are finding many more scenarios to leverage AI technology for a high level of driver-machine intuition.”
You may be using the same tile configuration across dashboards or similar dashboards across apps in Azure IoT Central. With Copy Dashboards new capability, you can leverage your existing work to build new dashboards by simply duplicating an existing dashboard.
This feature helps you to save time and eliminates the need to build a similar dashboard from ground up. When creating a copy, you will get the option to select a name and the dashboard type. After creating a copy, you can modify the tiles as per your needs.
Learn more about creating and managing dashboards in Azure IoT Central.
In December 2021, the following generally available updates and enhancements were made to Microsoft Defender for Cloud (formerly Azure Security Center):
Live Share has been on the frontiers of developer collaboration.
The extension comes built-in Visual Studio to make collaboration an intuitive part of their workflow. We gathered more information to learn that having communication channel within the tool could be of great value during collaboration. This is why, Visual Studio 2022 now has integrated chat built into Live Share. This allows each Live Share session to have a context specific chat. Whether it is long pairing sessions, quick-help or code walk-throughs, Live Share chat can add asynchronous context to the session.
See more at Integrated Chat in Live Share for Visual Studio 2022 - Visual Studio Blog (microsoft.com)
We are excited to announce the preview release of auto-failover groups for Azure SQL Hyperscale tier. This preview release includes support for forced and planned failover for Azure SQL Hyperscale databases that use active geo-replication and auto-failover groups. Some key benefits of auto-failover groups include:
Simplified management of a group of geo-replicated databases including ability to failover the entire group of databases.
Ability for application to maintain the same read/write and read-only endpoints after failover.
Recovery during loss of an entire region through geo-failover which can be initiated manually or through an automatic failover policy.
Readable online secondaries that can be used for read-only workloads by connecting with read-only listener endpoints which remain unchanged during geo-failovers.
See more at Auto-failover groups for Azure SQL Hyperscale now in preview - Microsoft Tech Community
Azure Purview now supports Snowflake as a data source to help you generate a holistic map of your data landscape with automated data discovery. You can now scan your Snowflake databases to easily bring over metadata into the Azure Purview data map, then manage and govern the Snowflake data in Azure Purview.
More about Azure Purview - snippset
We are pleased to share that Microsoft is named a Leader in the 2021 Gartner® Magic Quadrant™ for Cloud Database Management Systems.1 This placement reflects our completeness of vision and ability to execute, and we feel is a testament to our ongoing innovation and the integration of a comprehensive cloud data management ecosystem into Microsoft’s end-to-end data platform.
Today’s organizations are modernizing their data platforms as part of a broader digital transformation and need to rely on data as a strategic asset and competitive differentiator. Azure offers a full range of solutions for businesses seeking to accelerate their recovery from economic uncertainty. Gartner evaluates these use cases across 15 distinct criteria to determine their Magic Quadrant placements.
In this sprint, we are announcing updates to hosted images. We will retire macOS 10.14 Mojave images on December 10. In addition, we've included the brownout schedule for Windows 2016 hosted images.
Check out the release notes for details.
Azure Pipelines
AI is expected to contribute nearly $16 trillion to the global economy by 2030. There are, however, growing concerns about the ethical risks associated with AI systems. Companies acknowledge the need and benefits of operationalizing Responsible AI principles to guide their processes and actions. The big challenge, however, lies in execution; while Responsible AI is about rigorous engineering, its operationalization is tedious, manual, and time-consuming without the right tooling and infrastructure. There are minimal instructions, and few disjointed frameworks and tools available to empower data scientists explore and evaluate their models holistically. Moreover, to truly enable responsible use of AI, one require a whole new world of tools, best practices, and examples to inform their responsible data-driven decision making processes.
Instead of allowing all or no users to force push, admins can now be selective about who can force push to a repository.
Now, you can be specific about the people and teams who are allowed to force push. As shown in the image below, select Allow force pushes and Specify who can force push. Then, search for and select the people and teams who should be allowed to force push.
Transparent data encryption (TDE) in Azure SQL Database and Managed Instance helps protect against the threat of malicious offline activity by encrypting data at rest. Azure SQL TDE with Customer-Managed Key (CMK) enables Bring Your Own Key (BYOK) scenario for data protection at rest and allows customers to have full control of the key lifecycle management.
The ability to use an RSA key stored in Azure Key Vault Managed HSM, for customer-managed TDE (TDE BYOK) in Azure SQL Database and Managed Instance is now generally available.
With this, along with the existing option of using Azure Key Vault (standard and premium tiers), customers now have the flexibility to use Managed HSMs for storing their encryption keys to protect their most confidential workloads in Azure SQL.
You can now send device telemetry in different shapes and transform the telemetry into structured data at Azure IoT Central ingress. Data mapping in Azure IoT Central enables you to map a JSON path in device message to a friendly name (alias) at a device level. IoT Central will then use the device alias information to provide a structured data (mapped data) that you can leverage to create device templates and device management experiences in IoT Central such as Rules, and export the mapped data to any destination. With this capability, you can send industrial equipment data into IoT Central and create device management experience for your industrial equipment.
Using IoT Central portal, you can map the data for any or all your devices. Navigate to a device Raw data view, expand any telemetry message and hover the mouse pointer over a message path to add an alias. Once an alias is mapped to a JSON path, you can verify that IoT Central is mapping the telemetry by checking the ‘_mappeddata’ section in Raw data.
Learn more about transforming telemetry on ingress in Azure IoT Central.
The new Azure Monitor agent and data collection rules now support private virtual network configurations via private links and a new Azure resource type called data collection endpoints. This is now generally available. It will allow you to use these capabilities in restricted environments that need special networking requirements and isolation from the public internet. More information below:
- It’s configured using data collection endpoint, which must be created and ‘associated’ to the respective machines with the new agent installed
- It leverages the use of Azure Monitor Private Link Scopes (AMPLS)
- It can only be configured for data being sent to Azure Monitor logs; no support for Azure Monitor metrics
Read the documentation to configure the new agent to upload data via private links only, without accessing the public internet directly. If you haven’t already, review the updated migration guidance to start migrating to the new agent. And if you have any feedback, please share feedback on our feedback channel.
Azure Storage is announcing the public preview of the ability to create an additional 5000 Azure Storage accounts per subscription per region. This is a 20 times increase from the current limit of 250 and helps you create several hundred or thousand storage accounts to address your storage needs within a single subscription instead of creating additional subscriptions.
Source: Public preview: Create an additional 5000 Azure Storage accounts within your subscription
Microsoft announces that Microsoft Teams Give and Take Control is now generally available on Azure Virtual Desktop. Give and Take Control allows a meeting participant to control the presenter’s shared content during screen sharing.
With Give and Take Control:
- A presenter can give control of the shared content to another meeting participant to help present, change a file, make modifications, or demonstrate something. Both will be in control of the sharing and the presenter can take back control anytime.
- A meeting participant can request control while another person is sharing. The presenter can approve or deny the request.
- .NET
- .NET 6.0 Migration
- 5 Best websites to read books online free with no downloads
- 5 surprising things that men find unattractive
- 5 Ways To Take Control of Overthinking
- 6 simple methods for a more productive workday
- 6 Ways To Stop Stressing About Things You Can't Control
- Add React to ASP.NET Core
- Adding reCAPTCHA to a .NET Core Web Site
- Admin Accounts
- Adobe Acrobat
- Afraid of the new job? 7 positive tips against negative feelings
- Agile
- AKS and Kubernetes Commands (kubectl)
- API Lifecycle Management
- arc42
- Article Writing Tools
- Atlassian
- Azure API Management
- Azure App Registration
- Azure Application Gateway
- Azure Arc
- Azure Arc Commands
- Azure Architectures
- Azure Bastion
- Azure Bicep
- Azure CLI Commands
- Azure Cloud Products
- Azure Cognitive Services
- Azure Container Apps
- Azure Cosmos DB
- Azure Cosmos DB Commands
- Azure Costs
- Azure Daily
- Azure Daily 2022
- Azure Daily 2023
- Azure Data Factory
- Azure Database for MySQL
- Azure Databricks
- Azure Diagram Samples
- Azure Durable Functions
- Azure Firewall
- Azure Functions
- Azure Kubernetes Service (AKS)
- Azure Landing Zone
- Azure Log Analytics
- Azure Logic Apps
- Azure Maps
- Azure Monitor
- Azure News
- Azure PowerShell Cmdlets
- Azure PowerShell Login
- Azure Private Link
- Azure Purview
- Azure Redis Cache
- Azure Security Groups
- Azure Sentinel
- Azure Service Bus
- Azure Service Bus Questions (FAQ)
- Azure Services Abstract
- Azure SQL
- Azure Tips and Tricks
- Backlog Items
- BASH Programming
- Best LinkedIn Tips (Demo Test)
- Best Practices for RESTful API
- Bing Maps
- Birthday Gift Ideas for Wife
- Birthday Poems
- Black Backgrounds and Wallpapers
- Bootstrap Templates
- Brave New World
- Brian Tracy Quotes
- Build Websites Resources
- C# Development Issues
- C# Programming Guide
- Caching
- Caching Patterns
- Camping Trip Checklist
- Canary Deployment
- Careers of the Future You Should Know About
- Cheap Vacation Ideas
- Cloud Computing
- Cloud Migration Methods
- Cloud Native Applications
- Cloud Service Models
- Cloudflare
- Code Snippets
- Compelling Reasons Why Money Can’t Buy Happiness
- Conditional Access
- Configurations for Application Insights
- Create a Routine
- Create sitemap.xml in ASP.NET Core
- Creative Writing: Exercises for creative texts
- CSS Selectors Cheat Sheet
- Cultivate a Growth Mindset
- Cultivate a Growth Mindset by Stealing From Silicon Valley
- Custom Script Extension for Windows
- Daily Scrum (Meeting)
- Dalai Lama Quotes
- DataGridView
- Decision Trees
- Deployments in Azure
- Dev Box
- Development Flows
- Docker
- Don’t End a Meeting Without Doing These 3 Things
- Drink More Water: This is How it Works
- Dropdown Filter
- Earl Nightingale Quotes
- Easy Steps Towards Energy Efficiency
- EF Core
- Elon Musk
- Elon Musk Companies
- Employment
- English
- Escape Double Quotes in C#
- Escaping characters in C#
- Executing Raw SQL Queries using Entity Framework Core
- Factors to Consider While Selecting the Best Earthmoving System
- Feng Shui 101: How to Harmonize Your Home in the New Year
- Flying Machines
- Foods against cravings
- Foods that cool you from the inside
- Four Misconceptions About Drinking
- Fox News
- Free APIs
- Funny Life Quotes
- Generate Faces
- Generate Random Numbers in C#
- Genius Money Hacks for Massive Savings
- GitHub
- GitHub Concepts
- Green Careers Set to Grow in the Next Decade
- Habits Of Highly Stressed People and how to avoid them
- Happy Birthday Wishes & Quotes
- Helm Overview
- How to Clean Floors – Tips & Tricks
- How to invest during the 2021 pandemic
- How To Make Money From Real Estate
- How To Stop Drinking Coffee
- Image for Websites
- Inspirational Quotes
- Iqra Technology, IT Services provider Company
- Jobs Of 2050
- jQuery
- jQuery plugins
- JSON for Linking Data (JSON-LD)
- Json to C# Converters
- Karen Lamb Quotes
- Kubernetes Objects
- Kubernetes Tools
- Kusto Query Language
- Lack of time at work? 5 simple tricks to help you avoid stress
- Lambda (C#)
- Last Minute Travel Tips
- Last-Minute-Reisetipps
- Latest Robotics
- Leadership
- List Of Hobbies And Interests
- Logitech BRIO Webcam
- Management
- Mark Twain Quotes
- Markdown
- Meet Sophia
- Message-Oriented Architecture
- Microservices
- Microsoft Authenticator App
- Microsoft Power Automate
- Microsoft SQL Server
- Microsoft Teams
- Mobile UI Frameworks
- Motivation
- Multilingual Applications
- NBC News
- NuGet
- Objectives and Key Results (OKR)
- Objectives and Key Results (OKR) Samples
- OKR Software
- Online JSON Viewer and Parser
- Outlook Automation
- PCMag
- Phases of any relationship
- Playwright
- Popular cars per decade
- Popular Quotes
- PowerShell
- PowerShell Array Guide
- PowerShell Coding Samples
- PowerToys
- Prism
- Pros & Cons Of Alternative Energy
- Quill Rich Text Editor
- Quotes
- RACI Matrix
- Razor Syntax
- Reasons why singletasking is better than multitasking
- Regular Expression (RegEx)
- Resize Images in C#
- RESTful APIs
- Rich Text Editors
- Rob Siltanen Quotes
- Robots
- Run sudo commands
- Salesforce Offshore Support Services Provider
- Salesforce Offshore Support Services Providers
- Sample Data
- Save Money On Food
- Score with authenticity in the job interview
- Security
- Semantic Versioning
- Serialization using Thread Synchronization
- Service Worker
- Snipps
- Speak and Presentation
- SQL References
- SQL Server Full-Text Search
- Successful
- Surface Lineup 2021
- Surface Lineup 2021 Videos
- SVG Online Editors
- Team Manifesto
- Technologies
- Technology Abbreviations
- Technology Glossary
- TechSpot
- That is why you should drink cucumber water every day
- The Cache Tag Helper in ASP.NET Core
- The Verge
- Theodore Roosevelt Quotes
- These 7 things make you unattractive
- Things Successful People Do That Others Don’t
- Things to Consider for a Great Birthday Party
- Things to Consider When Designing A Website
- Thoughts
- TinyMCE Image Options
- TinyMCE Toolbar Options
- Tips for a Joyful Life
- Tips for fewer emails at work
- Tips for Making Better Decisions
- Tips for Managing the Stress of Working at Home
- Tips for Writing that Great Blog Post
- Tips On Giving Flowers As Gifts
- Tips you will listen better
- Top Fitness Tips
- Top Healthy Tips
- Top Money Tips
- Top Ten Jobs
- Track Authenticated Users in Application Insights
- Unicode Characters
- Visual Studio 2022
- Vital everyday work: tips for healthy work
- Walking barefoot strengthens your immune system
- Walt Disney Quotes
- Ways for Kids to Make Money
- Web Design Trends & Ideas
- Web Icons
- Web Scraping
- Webhooks
- Website Feature Development
- What are my options for investing money?
- What happens when you drink water in the morning
- What Is Stressful About Working at Home
- What To Eat For Lunch
- Windows 11 Top Features You Should Know
- Winston Churchill Quotes
- XPath
- You'll burn out your team with these 5 leadership mistakes
- ZDNet